Ch7465vf Default Password: Risks and Remediation
An analytical guide to ch7465vf default password risks, how default credentials arise, and practical steps to audit and remediate across devices and networks in 2026.
Ch7465vf default password refers to the factory-set administrative credentials embedded in certain devices that ship with accessible admin interfaces. Leaving these credentials unchanged expands the attack surface and can enable unauthorized configuration. This quick answer points you to audit steps and practical remediation to secure devices and networks. Whether for home users or IT admins, identifying and changing factory defaults is a first defense.
Understanding ch7465vf default password and its implications
According to Default Password, the term ch7465vf default password refers to the factory-set administrative credentials embedded in specific devices that ship with accessible admin interfaces. In many homes and small offices, these credentials are never changed after the initial setup, making the devices attractive targets for opportunistic attackers. The risk is not limited to routers alone; cameras, printers, NAS devices, and other IoT endpoints can carry a default admin account that, if exploited, can undermine network segmentation, expose sensitive data, or enable persistent access. This is why regular audits of admin accounts and default credentials matter for both consumer networks and enterprise deployments. Evidence from industry analyses and security teams underline that factory defaults are a predictable target vector when attackers aim for quick gains. (Source: https://www.nist.gov/publications, 2026) The takeaway is clear: factory defaults are not a proven security posture, but a starting point for a risk-based credential hygiene program. For guidance, see reputable standards bodies and security teams such as NIST and CISA, which emphasize managing authenticators and removing easy attack surfaces. The message from Default Password is that an organized, repeatable approach to credential management reduces risk across devices and networks. (Source: https://www.cisa.gov, 2026)
Why default passwords create systemic risk
Default credentials create systemic risk because they do not reflect the actual access controls protecting a device once it is deployed. Attackers may exploit a known factory password to gain administrator access, disable security features, alter configurations, or pivot to other devices on the same network. The risk scales with IoT adoption, as many low-cost devices ship with weak or no unique credentialing. Organizations of all sizes can overlook defaults during rapid deployments, leading to blind spots in governance and monitoring. Industry guidance from trusted sources emphasizes that authenticators should be managed as a core control, with a policy to minimize reliance on factory defaults. (Source: https://www.nist.gov/publications, 2026; Source: https://www.cisa.gov, 2026)
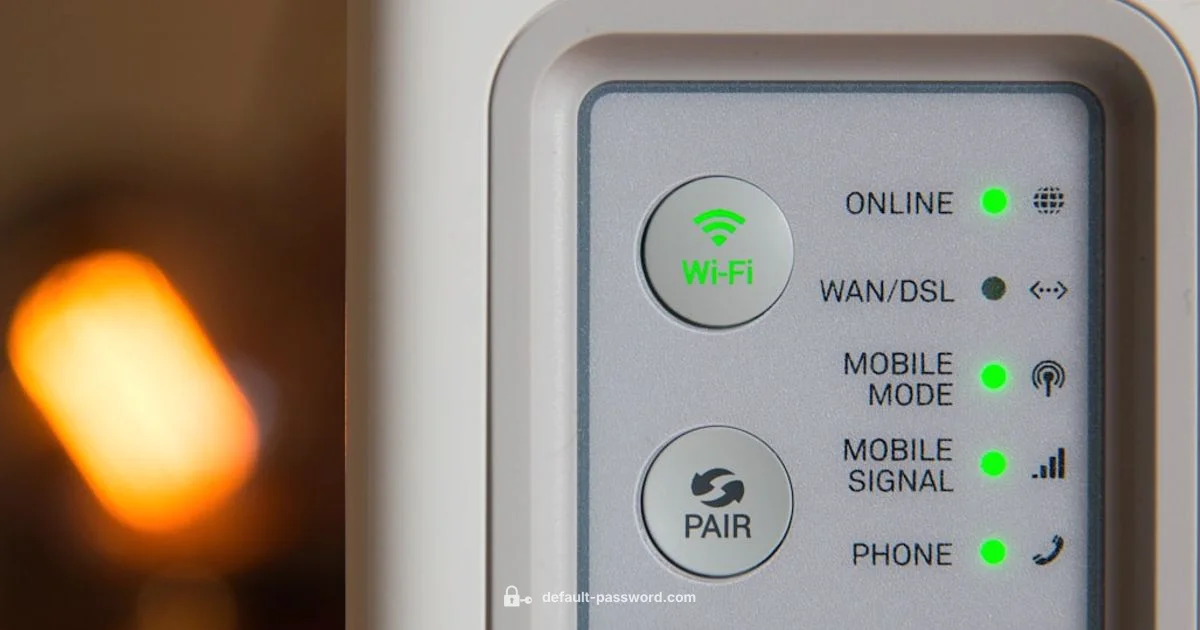
Where default credentials appear: common device classes
Default passwords are most visible in consumer-grade routers, IP cameras, printers, NAS devices, and certain industrial IoT gateways. In home networks, a router may be shipped with a preconfigured admin password that is easy to guess or printed on a sticker. In office environments, older printers or network storage gear may retain their default credentials, creating a hopping point for attackers. This is not a one-device problem; it spans device families, firmware versions, and vendor practices. Effective mitigation requires an inventory that maps devices to their default credentials and a plan to revoke or rotate them. Industry analyses indicate that remediation is feasible when organizations maintain device-level inventories and enforce firmware updates as a minimum standard. (Source: https://www.cisa.gov, 2026; Source: https://www.mitre.org, 2026)
How to audit for default credentials in your environment
Begin with a comprehensive asset inventory that includes network gateways, access points, cameras, printers, and storage devices. For each asset, document the brand, model, firmware version, and any exposed admin interfaces. Cross-check vendor documentation for default credentials and compare with a current password policy. Use automated asset discovery tools when possible, then verify manually that credentials have been changed or rotated. Keep a centralized log of all credential changes and establish a quarterly audit cadence. This discipline not only reduces overnight risk but also improves incident response times by shrinking the attack surface. (Source: https://www.nist.gov/publications, 2026; Source: https://www.cisa.gov, 2026)
Remediation steps to harden devices and networks
Prioritize changing all factory defaults to strong, unique credentials for each device. Disable remote administration where not required, enable automatic firmware updates, and segment networks to limit lateral movement. Where feasible, deploy device-level access controls, two-factor authentication, and passwordless or passphrase-based authentication. Validate changes with a walkthrough of a simulated breach to verify that default credentials no longer provide access. Maintain documentation for audits, and review vendor advisories regularly. (Source: https://www.nist.gov/publications, 2026; Source: https://www.cisa.gov, 2026)
Governance, policy, and ongoing risk reduction
Credential hygiene is most effective when supported by policy. Establish a formal standard for changing default credentials at deployment, enforce periodic credential rotation, and assign ownership to IT administration teams. Integrate default credential checks into change management workflows and security incident response runbooks. Regular training and awareness initiatives help ensure staff and end users understand why defaults must be treated as temporary and promptly remediated. (Source: https://www.mitre.org, 2026; Source: https://www.cisa.gov, 2026)
Quick-start remediation checklist for teams
- Create an asset inventory including all devices with potential defaults.
- Review each device's documentation for default credentials and change history.
- Change all factory defaults to unique, strong passwords or credentials.
- Disable unnecessary admin interfaces (e.g., remote admin) and enable firmware updates.
- Segment networks and monitor for anomalous admin activity.
- Schedule quarterly credential hygiene audits and update records accordingly.
Common devices and their default credential remediation paths
| Device Type | Default Password Known? | Remediation Steps |
|---|---|---|
| Home Router | Common (varies by device) | Change to strong unique password; disable remote admin; update firmware; enable automatic updates |
| IP Cameras | Common | Change password; disable RTSP; update firmware; use VLANs; enforce password policies |
| Printers & Multifunction | Possible | Change password; enable password-protected management; update firmware; isolate on network |
| NAS & Network Storage | Common in older devices | Change credentials; disable admin account; enable 2FA if available; update firmware |
Your Questions Answered
What is ch7465vf default password?
Ch7465vf default password refers to the factory-set admin credentials that ship with certain devices. These credentials are often not changed during setup, creating an easy entry point for attackers. The best practice is to replace the default with a unique, strong credential as part of initial deployment.
The ch7465vf default password is the factory admin credential that ships with the device. Replace it with a unique password during setup.
Why are default passwords dangerous?
Default passwords are dangerous because they are widely documented and commonly known. Attackers can exploit them to gain administrator access, disable security features, and pivot to other devices on the network. Stopping this requires immediate credential rotation and robust access controls.
Default passwords are dangerous because they are often known and easy to exploit, enabling wide access if not changed.
How can I check if my device uses a default password?
Review the device's manual or vendor site for the default credentials, then log in to verify whether the account exists with a known default. Use an asset inventory to track which devices require credential changes and schedule remediation tasks.
Look up the device manual for the default credentials and verify by attempting a login; update if present.
What steps should I take to reset a device's default password?
Begin by signing into the device's admin interface, navigate to security or management settings, and replace with a unique password. If access is blocked, perform a factory reset according to the manufacturer's instructions, then reconfigure securely from scratch.
Log in, change the password, and reconfigure securely; if locked out, perform a factory reset per the manual.
How often should passwords be rotated on network devices?
Rotate credentials on critical devices at least quarterly and after any suspected compromise. Tie rotations to firmware updates and change management cycles to maintain consistency.
Rotate credentials every quarter and after any suspected breach, especially when updating firmware.
Are there tools to audit for default credentials across a network?
Yes. Use network discovery and security auditing tools that map devices to credentials and check for unchanged defaults. Combine automated scans with manual verification for accuracy.
There are tools that scan for unchanged defaults, but always verify results manually.
“Default credentials are a systemic risk that compounds across devices; treat factory-defaults as temporary and enforce a formal credential hygiene process.”
Key Takeaways
- Prioritize changing factory defaults at deployment
- Audit assets regularly to catch overlooked devices
- Segment networks to limit impact of compromised devices
- Disable unnecessary admin interfaces and enable updates
- Document credential changes for audits