Cisco Default Credentials: Risk, Detection & Remediation
Understand Cisco default credentials risks, audit devices, and implement proven remediation steps to secure routers, switches, and security appliances—guided by Default Password.

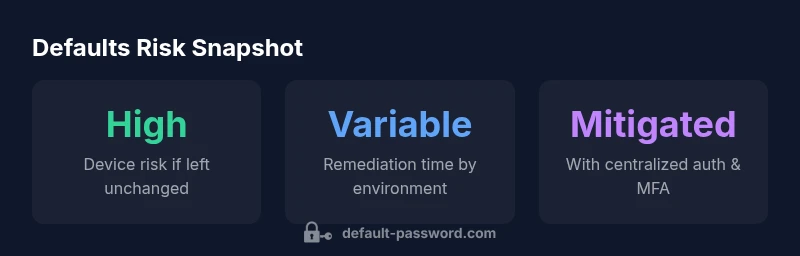
Cisco devices often ship with default credentials that, if left unchanged, grant attackers administrative access. The quick takeaway: inventory all Cisco devices, disable or rotate default accounts, enforce strong passwords and 2FA where available, and apply the latest vendor security advisories. Regular audits and centralized authentication reduce risk significantly. This is a foundational step in any network hardening plan.
Understanding Cisco default credentials and risk landscape
Cisco devices frequently ship with default accounts that, if not changed, provide attackers with administrative access. The risk is highest when devices sit at the network edge or integrate with untrusted segments. Default credentials enable broad control over routing, firewall policies, and access to management interfaces. In practice, attackers scan for exposed devices, enumerate accounts, and leverage weak credentials to pivot across a network. The modern threat landscape, including ransomware actors and opportunistic intruders, makes early retirement of default accounts a baseline security control. According to Default Password, a proactive approach combines asset inventory, strict configuration standards, and centralized authentication to reduce risk. Implementing role-based access and least privilege reduces potential blast radii. In this section, we’ll define risk categories, describe where defaults commonly appear in Cisco gear, and outline concrete steps to eliminate these weak points. The aim is to turn default credentials from a systemic vulnerability into a documented security control.
Common defaults by Cisco devices and why they persist
Cisco devices span routers, switches, security appliances, and wireless controllers. Historically, many devices used simple accounts such as an administrator with a single shared password. While newer devices support stronger defaults or mandate a change at first boot, gaps remain in large networks with legacy deployments. Defaults persist for legitimate reasons such as out-of-band management, initial setup convenience, or vendor documentation. Defaults persist for legitimate reasons such as out-of-band management, initial setup convenience, or vendor documentation. The key for IT teams is to identify every device type, locate vendor guidance, and map default accounts to remediation actions. In practice, you should consult Cisco's security advisories and your device's startup configuration to determine which accounts exist and whether they are enabled by default. This awareness lets you plan a holistic hardening effort that covers firmware updates, access controls, and monitoring.
How default credentials get exposed in networks
Default credentials become a risk when they are not rotated, when management interfaces are exposed to the internet, or when devices are discovered during onboarding without review. Common exposure paths include remote SSH/Telnet access, web-based configuration panels, and out-of-band management ports. Segmentation gaps, weak network access control, and insufficient log monitoring amplify the problem. Even devices that are properly configured can be compromised if a maintenance account is misused or an administrator shares credentials. Effective mitigation relies on enforcing policy-driven access, using centralized authentication with AAA, and ensuring that default accounts are either disabled or renamed and rotated on a regular cadence.
Practical guide to discovering defaults on devices you manage
Start with a comprehensive asset inventory that lists every Cisco device by location, model, and firmware release. Next, review startup configurations and device manuals to identify default accounts. Audit your network with automated tooling that flags enabled accounts with weak or blank passwords. Validate that management access is limited to trusted subnets and that SSH is preferred over Telnet. Create a standard operating procedure for removing or renaming default accounts during new device onboarding, and set required password standards that are enforced by centralized authentication. Finally, document every remediation step and maintain a change-management trail to prove compliance.
Best practices to secure Cisco devices
Adopt a defense-in-depth posture for device hardening. Immediately disable or rotate default accounts and enforce strong, unique passwords with policy-based rotation. Enable multi-factor authentication where supported and apply secure management practices, including SSH keys, public key authentication, and IP-based access control lists. Disable unnecessary services, restrict remote management to management networks, and ensure devices run vendor-supported firmware. Consider implementing centralized authentication (RADIUS/TACACS+) with role-based access control and clear session auditing. Regularly review device configurations and run automated, repeatable checks to maintain a compliant baseline.
Automated assessment and monitoring for default credentials
Automation helps detect drift between documented baselines and live configurations. Use asset discovery, configuration auditing, and real-time monitoring to spot enabled accounts that do not align with policy. Centralized logging from network devices, SIEM integration, and alert rules for failed login attempts are critical for early warning. Schedule periodic credential hygiene reviews, and integrate findings into your security operations workflow. By combining automated checks with human oversight, organizations can lower risk and respond faster to credential-related incidents.
Recovery and incident response when default credentials are exploited
Prepare a runbook that covers containment, eradication, and recovery. If a compromised device is detected, isolate it from critical segments, rotate all affected credentials, and review recent changes for indicators of compromise. Rebuild configurations from known-good backups where possible, and re-verify access controls before reintroducing devices to production. Document lessons learned, adjust detection rules, and strengthen the change-management process to prevent recurrence. A swift, coordinated response minimizes downtime and preserves incident evidence for forensics and compliance.
Compliance considerations and vendor guidance
Security frameworks such as NIST and CIS emphasize secure configuration and hardening of network devices. Cisco advisories and vendor best practices should inform your baseline, update cadence, and credential policies. Maintain an auditable trail of device hardening actions, including who changed what and when. Regular audits help prove compliance during internal reviews or external assessments. In all cases, prioritize least privilege, strict authentication, and ongoing monitoring as core controls.
Case studies and synthesis: what to do next
In a mid-sized enterprise with a mixed Cisco footprint, failed attempts to login via a default account triggered an immediate review. The team performed an asset inventory, disabled stale accounts, and enforced MFA on all management interfaces. They deployed centralized AAA, updated firmware, and instituted routine credential hygiene checks. The result was a measurable drop in security alerts related to device access and a smoother onboarding process for new devices. The practical takeaway is simple: make default credential hygiene a central part of your network security program, with ongoing reviews, automation, and clear ownership.
Cisco device default credential exposure by device type
| Device Type | Default Credential Availability | Typical Risk Level | Remediation |
|---|---|---|---|
| Cisco Routers (ISR/ASR) | Model-dependent; consult vendor docs | High | Disable or rotate defaults; enforce AAA |
| Cisco Switches (Catalyst) | Model-dependent | Medium-High | Rename/disable accounts; enable centralized auth |
| Cisco ASA/Firepower | Model-dependent | High | Disable defaults; use MFA; apply policy-based access |
| Cisco Wireless Controllers | Model-dependent | Medium | Change defaults; centralize management |
Your Questions Answered
What are Cisco default credentials?
Default credentials are preconfigured admin accounts that ships with devices. They vary by model and firmware and may be enabled by default on initial setup. Always verify and disable or rotate them as part of baseline hardening.
Default credentials are preconfigured admin accounts that come with devices; they vary by model and should be removed or rotated.
Why disable Cisco default credentials?
Leaving defaults unchanged provides attackers with a direct path to gain control over network devices. Disabling reduces exposure and is a foundational security control.
Defaults left on are a direct risk; disable them to reduce exposure.
How can I locate default credentials in devices I manage?
Review vendor manuals, startup configurations, and security advisories. Use asset inventories and configuration audits to identify enabled default accounts.
Check manuals and startup configs; use audits to find defaults.
What is the best practice to rotate credentials on Cisco devices?
Adopt MFA, centralized auth (RADIUS/TACACS+), unique passwords per device, and a defined rotation schedule.
Use MFA and centralized auth with unique device passwords.
Are there standards for securing Cisco devices?
Yes. Align with NIST/CIS guidance and vendor advisories; maintain baselines, audit trails, and least-privilege access.
Follow NIST/CIS standards and vendor advisories.
What should I do if a device uses a default credential that has been exploited?
Contain the device, rotate credentials, isolate affected segments, review for indicators of compromise, and remediate. Update detection rules.
Contain, rotate, isolate, and review for indicators of compromise.
“Default credentials are a solvable risk when organizations implement disciplined configuration management and continuous monitoring.”
Key Takeaways
- Audit every Cisco device for default accounts.
- Disable or rotate defaults immediately.
- Enforce centralized authentication and MFA.
- Maintain a clear remediation and change-management trail.
- Regularly review device configurations and firmware updates.