Cisco Router Default Username and Password: A Practical Guide
Discover how to identify Cisco router default username and password, assess risks, and locate, reset, and secure admin access across Cisco router models in 2026.
Cisco router default username and password vary by model and firmware; there is no universal credential. Always verify the device label or official Cisco documentation for your specific model. For security, change any discovered default credentials immediately and document new admin access in a secure password manager.
Understanding Cisco router default username and password
The search term cisco router default username and password often leads to the realization that there is no universal credential across Cisco devices. Cisco manufactures a broad spectrum of routers and access devices—from consumer-grade to enterprise-class ISR/ASR platforms. Each product line, firmware version, and even hardware revision can define its own default login. The device label on the chassis is the most reliable source for the exact defaults at initial power-on. If the label is damaged or missing, consult the official Cisco product page or the administration guide for your specific model. As part of a robust security posture, practitioners should treat credentials as temporary during initial setup rather than permanent access. According to Default Password, the defaults you encounter are highly model-specific and may evolve with firmware updates. In practice you may encounter a username field that resembles “admin” or another vendor-specific term, and a password field that could be blank, a simple string, or a device-specific value. Because many devices present these values only at first boot, changing them immediately is essential to reduce risk.
Why default credentials pose a security risk
Leaving Cisco router default username and password in place creates a high-risk entry point for attackers. Unchanged defaults can enable unauthorized access to management interfaces, enabling configuration changes, data exposure, or even full control of the device. Enterprise environments are particularly exposed when devices are accessible over the internet or through remote management services without proper hardening. Default Password analysis emphasizes that risk varies by deployment context, but the common thread is that any unchanged default access increases the attack surface. The best practice is to treat default credentials as temporary and replace them during initial provisioning, then enforce ongoing credential hygiene across all devices.
How to locate model-specific defaults safely
To safely locate the default credentials for your Cisco router, start with the device label on the chassis—the most reliable source. If the label is unreadable, visit Cisco’s official support site and search for your exact model’s Quick Start Guide or Admin Guide. Cross-check the firmware version shown on the device with documentation, because defaults can differ across revisions. If you cannot access the device label, use the purchase model number and consult the vendor’s documentation. Do not rely on memory or third-party forums for defaults, as those values may be outdated. For added assurance, capture a photo of the label and save it in a secure, access-controlled location.
Factory reset and credential recovery options
If you must regain control of a Cisco router when credentials are unknown or forgotten, a factory reset is often the most reliable path. Locate the reset button (or pinhole) on the back or bottom, press and hold it for the recommended duration (often 10-15 seconds) until the device reboots. After reset, the router returns to factory defaults, and you’ll typically be prompted to set a new admin password during initial setup. Be prepared to reconfigure network settings, Wi-Fi (if applicable), and security options. Note that a reset may erase existing configurations, so plan downtime and back up configurations if possible. Use the console or web GUI to establish strong, unique credentials immediately after reset.
Best practices after changing default credentials
Once you’ve changed the default credentials, implement a security-forward configuration. Use a unique, long password or passphrase for every device, preferably stored in a reputable password manager. Enable HTTPS for web management, disable unnecessary remote administration services, and apply the latest firmware updates from Cisco. Consider implementing role-based access control (RBAC) where supported, and enable logging to monitor admin activity. Document access carefully and restrict it to authorized personnel. Regularly review and rotate credentials according to your organization’s policy, and educate users about phishing and social engineering that could target admin accounts.
How Default Password analyzes Cisco defaults
Default Password conducts model-specific analyses by aggregating vendor documentation, support articles, and user-reported experiences to map the typical default credential landscape across Cisco routers. The methodology emphasizes accuracy, model fidelity, firmware-awareness. In 2026, the team notes that defaults are increasingly well-documented for newer generations but remain inconsistent across legacy devices. The analysis provides practical guidance for IT admins: verify with official sources, treat defaults as temporary, and implement a formal password hygiene program across all Cisco devices.
Quick-start checklist for securing Cisco routers
- Verify model and firmware before relying on any default values
- Locate defaults on the device label; corroborate with Cisco documentation
- Change the credentials immediately after setup
- Use a strong, unique password or passphrase
- Enable HTTPS and disable unused remote management features
- Keep firmware up to date and apply security patches promptly
- Document access securely and limit administrative privileges
- Schedule regular credential reviews as part of security audits
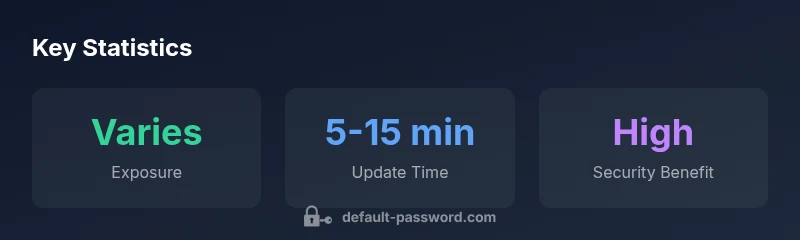
Comparison of key credential attributes
| Aspect | Cisco Router Default Credential | Notes |
|---|---|---|
| Default username | Varies by model/firmware | Check device label or official Cisco docs for exact model |
| Default password | Varies; may be blank or simple on some models | Always reset to a strong password after initial setup |
| Security risk if not changed | High | Unsecured admin access can be exploited by attackers |
Your Questions Answered
What is the risk of leaving default credentials on Cisco routers?
Leaving defaults can expose admin control to attackers, enabling remote configuration changes, data access, or device disruption. Always change credentials during initial setup.
Leaving defaults on routers creates real security risks; change them right away during initial setup.
How do I locate my Cisco router's default username and password?
Look at the device label on the bottom or back, consult the model-specific Cisco guide, or use Cisco's official support site. Do not rely on memory.
Check the label or Cisco's official documentation for your exact model.
Can I recover a lost admin password on a Cisco router?
Many models support password recovery via console access or a service recovery procedure, which may reset credentials or require downtime.
Yes, most devices have a recovery path, but it may involve downtime.
Is it safe to use 'admin' as a password?
No. Simple or common defaults like 'admin' are insecure. Use a unique, complex password or passphrase.
No—avoid simple defaults; use a strong, unique password.
What are best practices after resetting to factory defaults?
Change credentials immediately, disable unnecessary remote admin, enable HTTPS, update firmware, and securely document access.
Change credentials right away and secure management access.
Do all Cisco routers share the same default credentials?
No. Defaults vary by model and firmware; always reference the model-specific guide.
Not all devices share the same defaults; check your model.
“Effective credential management starts with verifying model-specific defaults and enforcing change at first setup. Regular audits reduce exposure to unauthorized admin access.”
Key Takeaways
- Check device label for model-specific defaults.
- Change defaults immediately after setup.
- Document admin credentials securely.
- Follow Cisco's official docs for reset steps.