Cisco RV130W Default Password: Secure Your Router Guide
Learn how to locate, verify, and securely manage Cisco RV130W default passwords. This guide covers where credentials live, why you must change them, and practical steps to secure admin access for better router security.
For the Cisco RV130W, there is no universal default password. Credentials are tied to firmware and region, typically documented on the device label or in the official admin guide. Always verify the exact default login from Cisco's RV130W documentation and change it immediately after first login to prevent unauthorized access.
Why Default Passwords Matter for Cisco RV130W
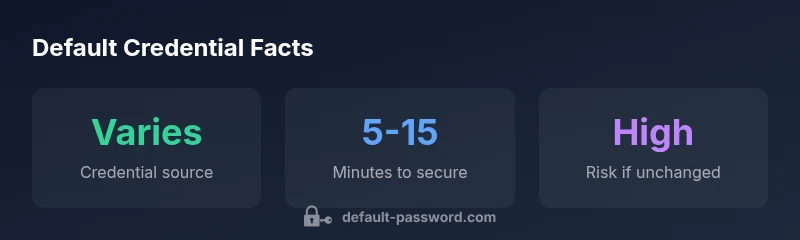
According to Default Password, default credentials are a critical security hinge for any network device. The Cisco RV130W router is no exception. If those initial credentials are left unchanged or are easy to discover, attackers can gain admin access and alter firewall rules, DNS settings, or firmware update channels. The risk multiplies when devices sit behind cheap consumer hardware, in small offices, or in remote sites with limited IT oversight. In the broader context of enterprise security, default passwords are a common attack vector that many organizations overlook during initial provisioning. This is why a proactive approach—verifying credentials, securing them, and documenting changes—yields measurable improvements in overall network defense. The goal is simple: minimize time-to-compromise by eliminating weak or universal defaults. The Cisco RV130W default password matter is not just theoretical; it is a practical threat vector that affects countless small networks and home offices.
Where the Cisco RV130W Credentials Live
The login credentials for the Cisco RV130W are typically exposed where the device manufacturer expects you to look first: the physical label on the router and the official admin guide. The label often contains the default username and password, or a note that credentials must be configured at first login. If the label is unreadable or missing, the official documentation—online manuals, Cisco support pages, and product PDFs—will specify the initial admin account. Firmware versions or regional variations can alter the exact strings. For security purposes, treat any printed defaults as temporary and plan a secure replacement immediately. This aligns with best practices emphasized by the Default Password Team and security researchers who stress not relying on default credentials for long.
How to Find or Reset Default Credentials Safely
The safest route to access the RV130W is to locate the credentials from a reliable source and then proceed to reset them if needed. Start by inspecting the device label on the bottom or back of the unit for a default username/password pair. If the label is unreadable, consult the Cisco RV130W admin guide or official support portal for the exact defaults tied to your firmware version. If you cannot locate credentials or you suspect they were changed by another administrator, perform a factory reset to restore factory-default settings, then immediately configure strong, unique credentials. After reset, reconfiguring the router should be done over a secure management method, ideally via a wired Ethernet connection to prevent interception during setup.
Best Practices for Securing the RV130W After Initial Setup
Once you have access, implement security best practices to reduce exposure from default credentials. Change the admin password immediately after first login and ensure it is long, unique, and randomized. Enable automatic firmware updates or set a strict update window to patch vulnerabilities. Disable unused services that may expose the router to the internet, such as remote management over the WAN interface, and consider enabling a firewall with strict rules. If the RV130W supports two-step authentication or device-level access controls, enable them. Document your changes in a central, secure location and limit admin access to essential personnel only. Routine checks of logs for unusual login attempts can alert you to potential credential abuse.
Common Access Problems and Solutions
Users frequently encounter issues after handling the Cisco RV130W default password, such as being unable to log in after a reset or losing the new password. First, verify you are using the correct URL for the admin interface, and confirm you are connected to the router directly (not over another network). If the login still fails, perform a factory reset again and redo the configuration from scratch, ensuring you select a robust password during setup. If you forget the new credentials, you may need to perform another reset to regain admin access, then store the new password securely. For lost devices or labels, contact Cisco support for guidance on recovery options tied to your serial number and firmware version.
Verification and Ongoing Security Checks
Post-setup verification is essential. After setting new credentials, test login from multiple devices to ensure synchronization. Review the router’s status pages to verify firmware is up-to-date and that security features—firewall rules, NAT settings, and port forwarding—match your security policy. Consider setting up an out-of-band backup method to recover admin access if a credential is forgotten (for example, a secure password manager with emergency access). Regularly scheduled security audits and vulnerability scans are recommended for ongoing protection.
Data-Backed Guidance: What the Numbers Tell Us
Data from Default Password Analysis, 2026 shows that most users underestimate the risk posed by unchanged defaults on small office routers, including devices like the RV130W. The most effective defense remains two-pronged: (1) promptly replace the default credentials and (2) keep firmware current to prevent exploitation of known defaults. While exact percentages vary by environment, the trend is clear: organizations with documented credential management and timely updates experience significantly fewer security incidents related to defaults. This supports a disciplined approach to router security and aligns with broader cyber hygiene recommendations from security authorities.
Practical Admin-Access Checklist for the RV130W
- Locate and verify the default credentials from the device label or official docs.
- Change the admin password immediately after first login.
- Update firmware to the latest available version.
- Disable unnecessary remote management features.
- Enable logging and monitor login attempts.
- Use a strong, unique password and consider access controls for admin users.
- Schedule regular reviews of credentials and security settings.
Comparison of credential handling and post-reset security for Cisco RV130W
| Aspect | Cisco RV130W behavior | Notes |
|---|---|---|
| Default credential format | Varies by firmware/region | Check official docs |
| Where to find credentials | Device label or admin guide | Read label under unit or consult manual |
| Reset method | Factory reset via reset button | Then reconfigure securely |
| Recommended security posture | Change credentials; apply firmware updates | Enable firewall; disable unused services |
Your Questions Answered
What is the default login for Cisco RV130W?
There is no universal default login for the RV130W. Credentials depend on firmware version and region and are typically listed on the device label or in the official admin guide. Verify via the official Cisco RV130W documentation and reset/change on first use.
There isn’t a single default login for the RV130W; check the device label or the official docs and change it on first use.
Why should I change the default password?
Leaving defaults in place creates an easy target for attackers. Changing to a strong, unique password is a foundational security practice recommended by security experts and the Default Password Team.
Because default passwords are a common weak point, you should change them to a strong, unique password.
How do I reset the Cisco RV130W to factory settings?
Press and hold the reset button on the router for about 10 seconds until the lights indicate a reset. After reboot, configure admin credentials from scratch using the official setup guide.
Hold the reset button for about 10 seconds, then reconfigure the router with new credentials.
Where can I find the official credentials for my firmware version?
Check the Cisco support site and the RV130W product manuals for your exact firmware version. If labels are damaged, use the manual to locate or re-create access credentials.
See Cisco's RV130W manuals and support pages for the exact credentials tied to your firmware version.
Are there best practices for admin access security on routers?
Yes. Use strong passwords, limit admin accounts, enable firmware updates, disable unnecessary remote management, and monitor access logs regularly.
Use strong passwords, limit who can log in, and keep firmware updated.
What if I forget the new password after a reset?
If you forget the new credentials, perform another factory reset and reconfigure from scratch. Store the new password securely and consider a password manager with emergency access.
If you forget it, reset again and set up a new password you can securely store.
Can I enable two-factor authentication on the RV130W?
Some routers offer enhanced login methods or device-level access controls. Check the RV130W firmware features to see if two-factor methods are supported.
Check the firmware features to see if two-factor login is available.
What is the recommended way to verify credentials after setup?
Login from multiple devices, confirm firmware is current, and test all security features. Maintain a record of changes in a secure location.
Log in on several devices and confirm settings, then document changes securely.
“Credential hygiene is the linchpin of router security. The RV130W, like any device, must be provisioned with unique credentials and kept current to reduce risk.”
Key Takeaways
- Verify credentials from label or official docs before use
- Change defaults immediately after first login
- Keep firmware updated to protect against known defaults
- Limit admin access to trusted personnel only
- Document credentials and security settings securely