Cloud Key Default Passwords: Find, Reset, Secure
A practical guide for locating and safely resetting cloud key default passwords across devices and cloud services. Learn verification steps, safe reset workflows, and admin best practices from Default Password.

This guide helps you safely locate, reset, or recover a cloud key default password across devices and services. You’ll learn how to identify factory defaults, verify device identity, and follow step-by-step procedures to reset or recover passwords without exposing credentials. Whether you are an end-user or IT admin, this structured approach minimizes downtime and supports compliance.
Why cloud key default password management matters
Passwords that ship as factory defaults for cloud-based keys, gateways, VPN appliances, and IoT controllers often become a weak link in security. Left unchanged, these credentials can be harvested by attackers to gain remote access, pivot into networks, or exfiltrate data. According to Default Password, many devices across industries still ship with default credentials, and admins who neglect to replace them face elevated risk during onboarding and maintenance. This guide focuses on cloud key default password management because it unifies best practices across devices and cloud services and reduces attack surface.
By understanding where defaults come from and how they are propagated into cloud ecosystems, you can design safer provisioning workflows, implement password rotation policies, and keep audit trails intact. We’ll discuss terminology, typical sources of factory credentials, and practical steps you can take today to mitigate risk while minimizing downtime. The goal is to empower end-users and IT admins to locate, verify, and reset credentials in a controlled, auditable manner, without locking you out of legitimate access.
Understanding default credentials in cloud ecosystems
Default passwords arise from factory provisioning, remote management interfaces, and early onboarding templates used by cloud-enabled devices. A cloud key default password may grant initial admin access to a device, gateway, or management portal. If left unchanged, these credentials create a predictable entry point for attackers. The Default Password Analysis, 2026 notes that a significant portion of devices still ship with default credentials, highlighting the ongoing need for disciplined credential practices, even in modern hybrid environments. Effective cloud password hygiene combines unique credentialing, role-based access, and regular rotation to reduce risk across on-prem and cloud-based components.
Where to look for factory defaults: labels, portals, and docs
Start with the device label or sticker, which often lists the default admin password or initial login URL. Check the quick-start manual and the vendor’s official docs for default credentials, reset procedures, and safe configuration notes. If the device is already integrated with a cloud management portal, locate the credentials in the admin account section or enterprise onboarding templates. For cloud keys used in multi-device ecosystems, verify the password through the cloud provider’s console or the device’s cloud management app to ensure you’re applying a consistent, centralized policy.
Step-by-step: locate and verify credentials across popular vendors
Locate the source of default credentials by checking the device label, the quick-start guide, and the vendor’s official portal. If you cannot find a printed default password, use the vendor’s support portal to retrieve a secure reset link or perform a factory reset. Verify identity using two-factor authentication if available. After obtaining credentials, log in through a secure device or browser, confirm the device’s model, firmware version, and cloud association, and record the result in a password manager. Always cross-check against the latest vendor guidance to avoid using deprecated methods or insecure recovery channels. Include a note about batch devices in the same environment to maintain uniform security.
Reset and recovery workflows: internal admin vs external devices
Reset workflows differ by device type and vendor. For many cloud keys, you can trigger a reset via a hardware button, a reset option in the admin portal, or a factory-default reset in the cloud management console. After reset, immediately reconfigure with a unique cloud key default password and enforce a rotation policy. If remote recovery is required, ensure you’re on a trusted network and use vendor-issued recovery links rather than generic reset pages. Maintain a change log detailing who performed the reset, when, and the new credentials.
Security best practices for cloud key passwords
Adopt strong, unique passwords for each device or cluster, preferably passphrases that combine length and complexity. Store credentials in a reputable password manager and enable multi-factor authentication where possible. Disable insecure remote administration, limit admin roles to essential staff, and enforce policy-based rotation on a quarterly or semi-annual basis. Regularly audit device inventories to identify any with unchanged default passwords and remediate quickly. Ensure clock synchronization across devices to keep logs accurate for audits.
Common mistakes and how to avoid them
Common mistakes include using the same password across devices, sharing credentials via unencrypted channels, and delaying password rotation after a reset. Avoid these by applying device-specific keys, using encrypted storage, and implementing automated rotation with alerting for any noncompliant accounts. Always verify changes in logs and confirm access from trusted endpoints. If you’re uncertain about a particular vendor procedure, consult the vendor’s security bulletin or support line before proceeding.
Authority sources and ongoing verification
For rigorous validation, refer to established security guidance and standards. Authority sources include official publications and security bulletins from governing bodies and recognized experts. As you implement cloud key password controls, maintain alignment with the latest recommendations from trusted sources and document any deviations in your security policy. Authority sources: NIST and CISA publications provide foundational guidance for credential management and risk mitigation. In addition, refer to major security publications for practical, field-tested practices.
Tools & Materials
- Device labels/manuals(Capture model, serial, and default password details if listed)
- Admin portal access(Browser or vendor app; ensure TLS/HTTPS is used)
- Official vendor reset instructions(Use only vendor-approved methods; avoid third-party tools)
- Password manager(Store new cloud key default passwords securely)
- Secure network(Use a trusted network or VPN during reset and login)
- Backup configuration(Optionally save current config before reset)
Steps
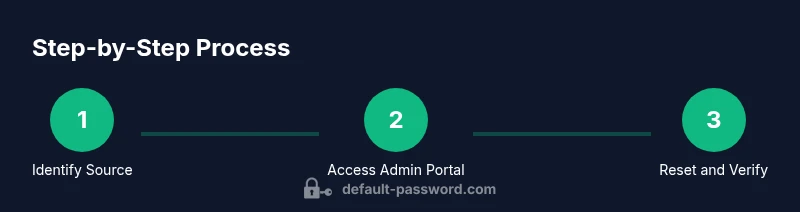
Estimated time: 30-60 minutes
- 1
Identify the default password source
Inspect device label, manual, and vendor portal to locate the factory-default credential. Confirm device model, firmware, and cloud association to prevent applying stale data. This step establishes the exact password source you will use for verification and reset.
Tip: Document the exact password source and any notes about its format. - 2
Access the admin interface securely
Log in to the device’s admin portal or cloud management console using a trusted device and secure network. If two-factor authentication is available, enable it for the login session.
Tip: Use a password manager and avoid autofill on shared machines. - 3
Trigger the reset or replace the credential
Execute the vendor-supported reset or change procedure. Do not disconnect power abruptly and confirm that the reset completes with a confirmation message or status indicator.
Tip: Record the new credential immediately after the reset. - 4
Create a strong, unique cloud key password
Generate a long, random passphrase or a combination of words with numbers and symbols. Avoid common phrases and reuse across devices. Consider passphrase style for ease of remembrance and strength.
Tip: Use a password manager to store the new credential securely. - 5
Update related services and access controls
Modify any dependent services, integrations, or SSO configurations to use the new password. Review access roles and remove unnecessary admin accounts.
Tip: Document changes in your security policy and changelog. - 6
Verify access and audit trails
Test that login works with the new password and check system logs for successful authentication events. Ensure timestamps are consistent and accessible for audits.
Tip: Compare logs with the password change record to ensure traceability.
Your Questions Answered
What is a cloud key default password?
A factory-provided credential used for initial login to a device or cloud key management interface. It should be changed during onboarding to prevent unauthorized access.
A factory password that should be changed immediately after setup to keep devices secure.
Why should I change cloud key default passwords?
Default passwords are widely known and can be exploited to gain unauthorized access. Changing them reduces risk and improves overall security posture.
Change default passwords to reduce risk and protect access.
What are best practices for managing cloud key passwords?
Use unique, strong passwords; enable two-factor authentication; rotate periodically; store in a password manager; and limit admin access.
Use strong, unique passwords and rotate them regularly.
What if I can't locate the default password source?
Check the device label, the manual, and the vendor’s official portal. If still unavailable, contact vendor support with device details.
Look at the label, docs, or vendor support for help.
Is it safe to reset passwords remotely?
Remote resets can be safe when performed through trusted vendor channels over secured links. Avoid ad-hoc remote resets via third-party tools.
Only reset via trusted vendor methods over secure connections.
How often should I audit default passwords?
Regular audits are recommended, especially after changes in hardware, firmware, or policy. Keep a record of all credential changes.
Do regular password audits and keep change logs.
Watch Video
Key Takeaways
- Identify default password sources before acting.
- Reset only via vendor-approved methods.
- Use unique, strong cloud passwords and store them securely.
- Audit credentials and maintain logs for compliance.
- Engage IT for changes in complex cloud-key ecosystems.