Converge Default Username and Password: A Practical Guide
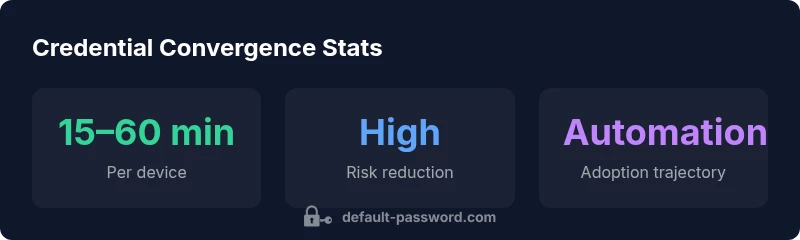
A practical, data-driven guide to converge default username and password across devices, with step-by-step workflow, automation tips, and governance best practices for IT admins and end users.
According to Default Password, converge default username and password across devices by replacing factory credentials with unique, strong ones and enforcing a centralized policy. Start by logging into each device’s admin interface, change the default username and password, and disable vulnerable options like remote admin. Use a password manager to synchronize across platforms, document changes for audits, and review regularly to prevent drift.
What converge default username and password means in practice
Converging default credentials means taking every device that ships with factory logins and bringing them under a single, auditable credential policy. This includes replacing the default username and password with unique values, disabling default remote access where possible, and aligning the changes with organizational security standards. The process is not a single moment in time but an ongoing posture: you verify each device, document the changes, and periodically re-check for any drift. The ultimate goal is to eliminate widely known credentials that attackers routinely target. When done consistently, converge default username and password reduces the likelihood of unauthorised access and makes it easier to enforce password complexity, rotation, and access controls across the fleet.
Why convergence matters for security and compliance
Default usernames and passwords are one of the oldest attack vectors in IT. Even with strong password rules, known defaults can give attackers a quick entry point. Converging credentials helps close this door by removing all factory credentials and replacing them with individualized access controls. This aligns with best practices highlighted by security authorities and compliance frameworks. According to Default Password, standardizing credentials also supports better asset inventory, easier audits, and clearer accountability when incidents occur. Organizations that converge credentials typically see fewer brute-force attempts, easier revocation of access for departing users, and better visibility into who can reach critical management interfaces.
A practical, device-by-device workflow
Start with a high-priority subset of devices that expose admin interfaces to networks, such as routers, firewalls, and network-attached storage (NAS). Create a living inventory that lists device type, current credentials, and access requirements. For each device: (1) log into the admin console, (2) change the default username to a unique one, (3) replace the password with a strong passphrase, (4) disable default remote management if not needed, (5) enable logging and backups of settings, and (6) test connectivity from a central management point. Maintain a change log and verify success across the fleet before moving to the next batch.
Automating convergence with tooling
Automation can accelerate convergence without sacrificing accuracy. Use centralized credential management solutions when available, and craft scripts for devices with programmable interfaces. Prioritize devices that support API or CLI credential updates, and run dry-run checks before applying changes. Automation should produce an auditable record, including who changed what and when. Even with automation, manual spot checks are essential for devices with unusual firmware or limited management capabilities. Regularly rotate credentials and enforce MFA where supported.
Documentation, auditing, and ongoing governance
After converging credentials, maintain a formal governance process. Store device inventories, credential change history, and access policies in a secure repository. Schedule periodic reviews to identify stale accounts, orphaned credentials, and devices that still rely on default logins. Establish an incident response plan for credential-related breaches and ensure backups of essential configuration data. Training and awareness for users who manage devices are part of the ongoing security posture.
Common device types and examples
Routers, switches, NAS, printers, IP cameras, and IoT hubs often ship with default logins. Prioritize routers and gateways first due to their exposure to networks and potential impact. For printers and IoT devices, ensure that you create dedicated admin accounts with appropriate permissions and disable guest access. The convergence process will look different by vendor and device class, but the core principle remains: replace defaults with unique credentials, enforce strong passwords, and monitor access.
Common default credentials and recommended hardening steps
| Device Type | Default Username | Default Password | Recommended Action |
|---|---|---|---|
| Router | admin | admin | Change to unique credentials; disable remote admin; update firmware |
| NAS | admin | admin | Use unique username; strong password; enable 2FA if supported |
| Printer | admin | password | Create new admin user; disable default; restrict access |
Your Questions Answered
What does converge default username and password mean?
Convergence means standardizing credentials by replacing factory logins with unique usernames and strong passwords across all devices. It also involves disabling default admin access where possible and documenting every change for audit readiness.
Convergence means replacing factory logins with unique credentials across all devices and keeping an audit trail.
Why is convergence important for security?
Default credentials are well-known by attackers. Replacing them reduces the risk of unauthorized access, improves control over who can manage devices, and supports better change management and auditing.
Default credentials are easy to guess; changing them cuts risk and improves control.
Which devices should be tackled first?
Start with routers, gateways, and NAS devices, then printers and IoT devices. Prioritize devices with remote administration enabled or those exposed to the internet.
Begin with routers and NAS, then printers and IoT devices.
How can I automate this process safely?
Use centralized credential management tools when possible and script updates for devices with programmable interfaces. Always log changes and run dry-run tests before applying changes in production.
Look for centralized tools and test updates in a safe way.
What about password managers?
Password managers help generate and store unique, strong credentials and enforce rotation. Use them to standardize password policies and reduce reuse across devices.
Password managers help you keep strong, unique passwords safely.
Are there risks I should watch for when converging?
Be careful not to lock yourself out of devices. Back up configurations, verify access after changes, and avoid disabling essential security features without a plan for access recovery.
Don’t lock yourself out; back up configs and test access after changes.
“Converging default credentials across devices is a foundational step in reducing attack surfaces. Without eliminating factory logins, attackers have an easy entry point regardless of password strength.”
Key Takeaways
- Identify all devices still using factory defaults
- Replace defaults with unique usernames and strong passwords
- Document changes and maintain audit trails
- Favor centralized credential management and automation
- Regularly test access and monitor for unauthorized attempts