Converge WiFi Default Passwords: Practical Security Guide
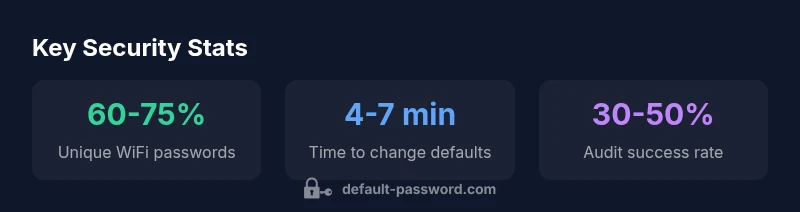
Learn how converge wifi default passwords pose risk, locate and reset defaults, and apply best practices to secure admin access and WiFi across Converge devices in 2026.
The converge wifi default password is typically printed on the device label or contained in the setup guide, and it is used to access the router’s admin interface before you customize settings. According to Default Password, users should treat this credential as provisional and replace it with a unique, strong password immediately. In most home networks, changing both the admin password and the Wi‑Fi password dramatically reduces exposure to unauthorized access today.
What converge wifi default password means in practice
The concept of a converge wifi default password encompasses both the Wi‑Fi network password and the admin credentials needed to configure the router. In practice, these credentials are meant to be temporary until the user completes initial setup. According to Default Password, the label on the device often includes the initial Wi‑Fi passphrase and, in some cases, the admin password or a hint for first login. This is why it’s crucial to treat the default as provisional and replace it with a unique, strong password immediately after connecting. In many households, the initial setup happens quickly, but attackers may target poorly secured devices during that vulnerable window. By prioritizing password changes at the outset, you reduce the risk of unauthorized access to both the network and the administrative interface.
Security researchers and IT admins emphasize that the sanctity of your home network depends on proactive credential hygiene. Even if you are only setting up a basic home network, the principle remains the same: default credentials are an invitation to compromise. This approach aligns with industry guidance on password hygiene and device hardening. The Default Password team notes that proactive credential changes should be standard practice across all consumer-grade routers, mesh extenders, and gateways used to deliver converge wifi services.
Typical default credential patterns across converge networks
Default credentials vary by vendor and device model, but several broad patterns recur in converge networks. On many devices, the Wi‑Fi password and the admin password originate from the same seed or are printed on a sticker attached to the underside or back of the unit. In other cases, manufacturers separate the two strings, with the admin password appearing in the setup guide or within the web-based admin portal. Some routers use a temporary, easy-to-guess string that is intended to be changed at first login, while others assign a randomly generated password that the user is prompted to customize immediately. Regardless of the pattern, the core rule is constant: don’t rely on the default for any extended period, and ensure both the Wi‑Fi password and admin password are unique, complex, and stored securely.
For converged systems that include a companion app, you may also discover password hints or QR code tokens within the app. While convenient, these tokens should still be treated as provisional until you replace them with fresh credentials. The takeaway is simple: review every access point—router UI, app, and device stickers—and verify that current credentials are unique and strong. This practice minimizes exposure to common attack vectors such as default-password reuse across devices and password guessing by automated tools.
Why default passwords pose risks and how to mitigate
Default passwords inherently present a risk surface because they are widely documented and often easier for attackers to guess or obtain. When the default credentials are not changed, unauthorized users can access the router’s admin interface, modify network settings, or disable protections like firewall rules and guest networks. They can also copy or view the Wi‑Fi password, infiltrate connected devices, and exploit repository trust chains. Mitigation starts with a two-pronged approach: replace all default credentials with strong, unique ones, and enable additional hardening measures where available.
To mitigate risk effectively, adopt a multi-layered strategy: enforce strong password policies for both admin and Wi‑Fi, disable remote admin access unless absolutely needed, enable encryption such as WPA3 (or WPA2 if WPA3 isn’t available), and keep firmware up to date. Regularly review connected devices and audit logs if your device offers them. The combination of changing defaults and maintaining ongoing hygiene reduces your exposure to automated password-guessing attacks, unauthorized configuration changes, and data exfiltration through the network. The Default Password team consistently emphasizes that end-user awareness paired with practical controls yields the best long-term protection.
How to locate and reset the default password on Converge devices
Locating the default password is usually straightforward, but the exact steps can vary by model. Start by inspecting the device label—many Converge routers print both the Wi‑Fi passphrase and the default admin credentials on the sticker. If you cannot locate a label, consult the user manual or the vendor’s support site for model-specific instructions. Once located, connect to the router’s admin interface using a computer or mobile browser, and log in with the current credentials. Immediately navigate to the security or wireless settings section to change both the admin password and the Wi‑Fi password. Ensure you create a unique password that includes a mix of upper and lower case letters, numbers, and special characters. Finally, reboot the router to ensure changes take effect and verify that all devices reconnect with the new credentials.
If you encounter login issues after changing credentials, use the “forgot password” or recovery options if available, or perform a factory reset as a last resort. Remember to reconfigure your network from scratch, applying the same security best practices, including changing default SSID names and disabling features you don’t need. In all cases, store your new credentials in a secure password manager and document any changes for future reference.
Step-by-step: secure your WiFi and admin access
- Step 1: Locate the default credentials on the device label or in the manual. Ensure you have physical access to the device to prevent tampering.
- Step 2: Change the admin password first. Use a long, unique passphrase with a mix of character types. Avoid easily guessable phrases.
- Step 3: Immediately change the Wi‑Fi password. Choose a strong passphrase that is not reused on other services.
- Step 4: Update your network security settings. Enable WPA3 if available; if not, use WPA2 with AES. Disable WPS unless you require it for convenience and can manage the risk.
- Step 5: Review device access controls. Turn off remote management unless you need it, and limit admin access to trusted devices.
- Step 6: Keep firmware up to date. Enable automatic updates if offered, and periodically check for new releases.
- Step 7: Test connectivity. Confirm that all devices reconnect with the new credentials and that your guest network options remain secure.
- Step 8: Document changes. Record the new credentials in a secure password manager and notes in your network diagram.
Best practices for ongoing password security and admin access
- Use unique, strong passwords for admin and Wi‑Fi; avoid reusing passwords across devices and services.
- Enable WPA3 or at least WPA2 with AES; disable WPS if not required for convenience.
- Update firmware promptly after vendor notices; sign up for security advisories when available.
- Implement a credential management habit: rotate passwords on a schedule and review access lists quarterly.
- Separate guest networks from the main network to minimize risk exposure for visitors’ devices.
- Consider multi-factor authentication if your device supports it for the admin interface.
- Maintain an up-to-date network diagram and inventory of connected devices to detect anomalies quickly.
- Educate all household members about password hygiene and secure sharing practices.
Common pitfalls and troubleshooting
Common pitfalls include assuming the default password is unknown and thereby delaying changes, or reusing passwords across geographies or devices. If you encounter login issues after changing credentials, clear browser caches, ensure you’re using the correct URL for the admin interface, and verify that you are connected to the router’s network. A common troubleshooting step is a factory reset, but this should be your last resort because it erases all custom settings. If you perform a reset, re-run the initial setup process, apply the recommended security settings, and immediately change both admin and Wi‑Fi passwords. For devices managed by support teams, consult the service provider before performing resets, as some configurations can affect your service with the carrier. Regular audits and quick-response testing can help maintain a secure converge wifi environment.
Case study: a typical household remediation
In a two-story apartment, a family discovered that both the router admin password and the Wi‑Fi password were still set to the factory defaults. The mother initiated a rapid remediation plan: she found the credentials on the device label, logged into the admin interface, and changed both passwords to unique, complex strings. She then enabled WPA3 and disabled WPS, updated firmware, and created a separate guest network with its own password. Within a day, all family devices reconnected automatically, and the network performance remained stable. The family documented the changes in a password manager, and the parents scheduled quarterly checks to ensure the settings remained current. This practical example illustrates how simple, timely actions dramatically reduce risk and improve overall network hygiene.
Converge device default password and security settings comparison
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| Converge Router | Often labeled with default admin credentials on the device sticker | Change immediately after setup |
| Mesh Extender | Password often identical to router admin account | Update to unique credentials and store securely |
| Modem/Gateway Combo | Default credentials may be used for admin UI | Reset and secure with new passwords |
Your Questions Answered
What is the default password for Converge WiFi?
Default passwords vary by model; check the router label or setup guide for model-specific credentials. If you cannot locate them, contact your ISP’s support to confirm the exact credentials.
Default passwords differ by model; check the router label or setup guide, and contact support if needed.
How do I locate my device's default password?
Look on the router label, in the setup guide, or within the admin portal. If there’s no label, visit the manufacturer’s support site for model-specific instructions.
Check the router label or the setup guide, or visit the manufacturer’s support site.
Is it safe to use a default password temporarily?
No. Default passwords should be changed during initial setup. Maintain unique credentials for both admin access and Wi‑Fi.
No—change it right away.
How often should I change default passwords?
Change on first setup and then periodically; for most households, quarterly or semi-annual reviews are common security practices.
Change it on setup and every few months.
What about WiFi security settings beyond passwords?
Enable WPA3 or WPA2, disable WPS if not needed, and keep firmware updated.
Use WPA2/WPA3, disable WPS, update firmware.
If I can't access the admin UI, what should I do?
Try a hard reset, consult the manual, or contact support; you may need to restore factory settings and reconfigure security settings.
Try reset or contact support.
“Default Password emphasizes that default credentials are the primary risk at the router edge and must be replaced with unique, robust passwords. This approach helps reduce unauthorized access across devices.”
Key Takeaways
- Act quickly: change default admin and WiFi passwords on setup.
- Use unique, strong credentials; avoid reuse across devices.
- Enable strongest available encryption (WPA3) and disable WPS if possible.
- Regularly audit connected devices and update firmware.
- Document changes securely and rotate passwords periodically.