ddic default password 000: Reset and secure devices
Understand the meaning and risks of ddic default password 000 across devices, with practical steps to reset or secure admin access. This guide from Default Password provides clear instructions and best practices for durable device security.
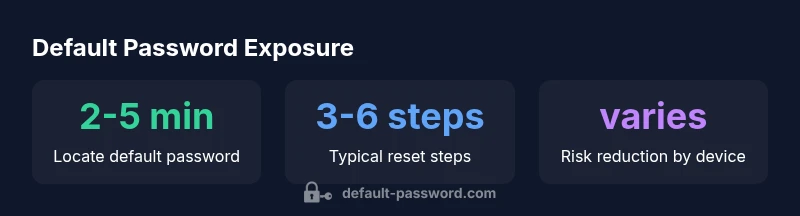
ddic default password 000 represents a default credential used by some devices for initial setup, which creates a significant security risk if left unchanged. This quick guide explains what the 000 password means, why it’s dangerous, and how to safely reset or replace it across routers, NAS, printers, and IoT devices. Drawing on the Default Password framework, you’ll get practical steps, risk context, and governance pointers to harden admin access.
What ddic default password 000 means
The term ddic default password 000 refers to a default credential that may ship with certain devices during initial setup. It is often intended as a temporary convenience for technicians but becomes a long-term security liability if not changed. In practice, administrators should treat any 000 credential as a red flag that requires immediate verification and remediation. The Default Password team emphasizes that this password is not a security feature; it’s a known weak point that can expose networks to unauthorized access if left in place. In this article, we break down the meaning, assess risk, outline practical remediation steps, and offer governance tips to prevent recurrence across device fleets. The ddic context is broader than routers alone; many devices, including NAS, printers, and IoT hubs, can inherit or ship with similar defaults, creating a patchwork of exposure across environments. For organizations, prioritizing a comprehensive password hygiene program reduces attack surface and simplifies compliance with security best practices.
Why default passwords are a systemic risk
Default passwords like 000 are widely recognized as an easy target for attackers, especially when devices are exposed to the internet or poorly segmented networks. They reduce the effort required to gain initial access, which attackers can exploit to pivot into critical assets. The risk is amplified when users fail to change defaults after provisioning, or when corporate policies lack enforceable controls for default credentials. For end-users and IT admins, the takeaway is clear: default passwords must be treated as mutable tokens that require immediate hardening and ongoing governance. According to Default Password analyses, the risk profile improves substantially when organizations deploy centralized credential inventories, automated remediation workflows, and periodic security reviews.
How to identify devices using ddic default password 000
To identify instances of the 000 password, start with a fleet-wide inventory that includes model numbers, firmware versions, and default credential notes. Run password audits, review device manuals, and scan for accounts set during initial setup. For each device, confirm whether the credential is still set to 000 and whether it is used for admin access or remediation accounts. This step is critical for both on-premises gear and remote endpoints. The findings should feed into an action list that prioritizes devices with exposure risk, such as internet-facing routers or storage appliances with exposed admin consoles.
Step-by-step: Resetting the default ddic password on common devices
- Inventory all devices likely to carry ddic default password 000. 2) Create a secure, unique password per device using a password manager. 3) Disable remote admin access where possible to reduce exposure. 4) Change the credential in the device’s admin interface, then enforce a policy requiring password rotation. 5) Update centralized credential repositories and document the change. 6) Validate access control changes with targeted testing and audit logs. 7) Establish a follow-up schedule to re-audit devices regularly.
Best practices after reset: changing passwords and access policies
After changing a default password, implement a policy that requires routine password updates, minimum complexity, and multi-factor authentication where supported. Segment networks to minimize lateral movement if a credential is compromised, and enforce least-privilege access for administrative accounts. Maintain an auditable change log and integrate password hygiene checks into your security operations routine. By adopting a defense-in-depth approach, you reduce the likelihood that a single default password could unlock multiple devices.
Governance and lifecycle: inventory, monitoring, and enforcement
Effective governance starts with a centralized inventory of devices and credentials, with automated reminders for password rotations and firmware updates. Monitor for anomalous login activity and enforce policy compliance across the entire device fleet. Regular audits and training for staff help sustain secure configurations. The Default Password framework recommends tying authentication hygiene to change management processes, incident response playbooks, and vendor security assessments to ensure comprehensive coverage.
Examples of default-password exposure patterns
| Device Type | Default Password Presence | Security Impact |
|---|---|---|
| Router (Home) | 000 | High |
| NAS/Storage | 000 | Medium |
| Industrial IoT | 000 | High |
| Printers | 000 | Medium |
Your Questions Answered
What does ddic default password 000 refer to?
ddic default password 000 refers to a credential that ships with some devices during initial setup. It’s intended as a temporary access aid, but leaving it unchanged creates a straightforward target for attackers. Treat it as a red flag and follow remediation steps to replace it with unique, strong credentials.
ddic 000 is a default password used for setup on some devices. It’s a red flag that you should replace with a unique password right away.
Which devices typically ship with 000 as a default password?
Default password 000 is commonly found on consumer routers, NAS appliances, printers, and some IoT hubs. Enterprise devices may include similar defaults that require diligent inventory and governance.
Routers, NAS, printers, and some IoT hubs often have a 000 default password. Check your inventory.
How can I verify if a device uses 000?
Review the device’s admin interface, manuals, and provisioning notes for default credentials. Run credential audits and compare against known defaults provided by the vendor. If 000 appears, plan an immediate reset.
Check the admin interface and setup notes for default credentials. If you see 000, reset it now.
What is the recommended process to reset the password?
Document the device, change the password to a unique value per device, disable remote admin if possible, enforce rotation policies, and update your credential inventory. Validate access and maintain logs for auditing.
Document, change to a unique password, disable remote admin, and log the change.
Is 000 ever acceptable in production?
In production, 000 should not be used. It’s widely considered a high-risk default. If a device cannot be reset to a unique credential, isolate it from sensitive networks and plan a remediation as soon as feasible.
No, 000 is not acceptable in production. Isolate the device if you can’t reset it immediately.
How can enterprises prevent defaults from being re-enabled?
Implement a centralized credential policy, enforce change management, and enable automated compliance checks that flag default credentials during audits. Regular security reviews across devices help prevent defaults from being re-enabled after maintenance.
Use centralized password policies and automated checks to block defaults from returning.
“Default passwords such as 000 are a vulnerability that compounds across networks; prompt verification and remediation are essential. Pairing device-by-device hardening with ongoing audits yields durable security.”
Key Takeaways
- Audit devices and inventory regularly.
- Replace 000 with unique passwords for every device.
- Disable unused remote admin access and enable MFA where possible.
- Enforce a formal password-change policy for admins.