Default Password DDIC Client 000: Reset, Rotate, Protect Admin Access
Learn how to safely reset and manage the default password for DDIC client 000, prevent security gaps, and enforce best practices for admin access across devices and services.

You're here to reset or recover the default password on a DDIC client, specifically the 000 credential, and to harden admin access across connected systems. This guide provides a practical, step-by-step approach, security best practices, and troubleshooting tips to prevent unauthorized access. By following these steps, IT admins and end-users can safely reset, rotate, and verify credentials.
Why default passwords matter for DDIC clients
In SAP environments, the DDIC user is a privileged account used for data dictionary operations. If the default password remains unchanged, attackers may gain administrative access, compromising data dictionary integrity and system configuration. According to Default Password, many organizations underestimate the risk of not rotating credentials on factory defaults, especially when DDIC is exposed to networks or connected services. The phrase default password ddic client 000 often appears in onboarding guides, but it also highlights a critical security fault: a single weak credential can unlock access to multiple subsystems. This section explains the core risks and how to mitigate them through policy, governance, and secure operation strategies. You will learn how default credentials originate, why they persist, and how to begin a safer password-management lifecycle across your DDIC client environment. By aligning with security best practices and enterprise standards, you reduce the chance of credential-related incidents, meet auditing expectations, and improve overall resilience. The broader lesson is simple: treat factory defaults as temporary, enforce rapid rotation, and monitor for unusual login activity.
How to identify if your DDIC client uses a default password
Finding whether a default password like 000 is in use begins with an asset inventory and a credentials review. Start by listing all DDIC client instances in scope and checking their login configurations, including whether accounts were created with standard or non-unique passwords. Look for explicit references to typical defaults in vendor documentation or deployment guides. If you discover the phrase default password ddic client 000 in any location, escalate to your security team and implement immediate rotation. Use configuration auditing tools or scripts approved by your organization to scan for known default credentials. Document findings in your change log and prioritize remediation according to risk exposure, such as systems connected to the internet or those housing sensitive metadata. This approach ensures you know where to focus your hardening efforts and when to apply compensating controls, such as MFA and IP allow-lists, to reduce attack surfaces.
Risk scenarios when default credentials are left active
Active default passwords present several risk scenarios. An attacker could impersonate DDIC administrators during maintenance windows, tamper with metadata definitions, or extract sensitive configuration. Lateral movement becomes easier if the DDIC client shares credentials with other systems, increasing exposure across the landscape. In regulated industries, failing to rotate or remove defaults can trigger governance concerns and non-compliance findings. The problem compounds when credential storage practices are weak or when logs are incomplete, making incident detection harder. To mitigate, implement strict password-change windows, enforce strong passphrases, and integrate password rotation with centralized secret management. Regular audits and automated alerts for any reuse of credentials across services help maintain visibility and accountability.
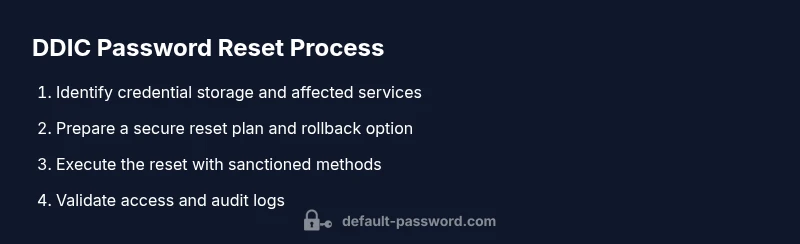
Secure password reset workflow overview
A robust reset workflow reduces risk and downtime. Start with a documented procedure that covers approval, verification, change execution, and validation, then map the workflow to your DDIC client’s architecture. Before making changes, gather sign-off from data owners and ensure a rollback plan exists. Execute the reset using sanctioned methods, ensuring you replace the old default password ddic client 000 with a unique, strong credential. Validate through login attempts, system logs, and automated health checks. Prepare for potential service interruptions and communicate expected windows to stakeholders. Finally, rotate related credentials across connected services and update all relevant access controls and documentation. Adherence to governance standards helps protect assets, preserves data integrity, and reduces incident-response time.
Best practices for securing DDIC admin access after reset
Security hygiene post-reset matters as much as the reset itself. Enforce MFA on the DDIC administrator account when supported, and require complex, unique passwords for each system. Keep credentials out of plain text, using a reputable password vault or enterprise secret-management tool. Enforce least privilege, apply role-based access control, and implement automatic lockouts after repeated failed attempts. Maintain an authoritative inventory of active accounts and conduct periodic reviews. Establish a clear incident-response plan that defines steps to take if a credential is suspected compromised. Finally, ensure that logging is centralized and tamper-evident, so auditors can verify access patterns during security reviews.
Troubleshooting common issues with DDIC password resets
Even a well-designed reset can hit snags. If the new password fails to authenticate, verify the target system’s clock, as time skew can prevent token-based authentication from working. Check that the reset was applied to all relevant nodes or services that reference the credential, and confirm there are no cached credentials lingering in clients. If access remains blocked, re-run the reset using a secondary verification channel and consult the official vendor documentation. Ensure you update dependent scripts or jobs that rely on the old credential. When in doubt, revert to a known-good backup of configuration, re-test, and execute a cautious re-rotation following approval.
Compliance, auditing, and governance considerations
Organizations face audits that examine password practices for privileged accounts. Align your DDIC password management with security frameworks and regulatory expectations. Maintain an auditable trail of password changes, including timestamps, initiator identity, and affected assets. Use centralized secret management to minimize exposure and enforce rotation schedules. In multi-account environments, coordinate reset cycles to avoid simultaneous changes that could disrupt services. Regularly review access logs for anomalies and conduct simulated breach exercises to validate detection capabilities. By treating password governance as a continuous process, teams strengthen security posture and meet governance obligations.
Authority references
- https://www.nist.gov
- https://www.cisa.gov
- https://www.sans.org
Tools & Materials
- DDIC client admin account(Ensure admin rights on the target system)
- Official reset procedure document(Source from vendor/internal policy)
- Secure workstation(Dedicated, updated device for credential changes)
- Password manager/vault(Optional for storing new credentials securely)
- Multi-factor authentication (MFA)(Enable where supported for added protection)
Steps
Estimated time: 45-90 minutes
- 1
Identify credential storage location
Locate where the DDIC client stores credentials (config files, databases, or secret vaults). Verify the scope of systems affected and confirm you have admin authorization before proceeding.
Tip: Document the exact storage locations before editing to avoid misconfigurations. - 2
Back up configuration and logs
Create a secure backup of current DDIC settings and relevant logs. This enables rollback if the reset impacts services or access controls.
Tip: Store backups in a trusted vault and note the restore procedure. - 3
Initiate authenticated reset
Trigger the password reset using sanctioned methods and replace the 000 credential with a unique, strong password. Confirm the reset completes on all targeted nodes.
Tip: Use a test account to verify the reset works without locking out admins. - 4
Rotate credentials across linked services
Update credentials in all connected systems that rely on the DDIC client authentication. Ensure consistency to prevent service disruption.
Tip: Coordinate change windows to minimize downtime. - 5
Test access and logs
Attempt login with the new password and check system logs for authentication events. Verify that access is granted and that audit trails reflect the change.
Tip: Automated health checks speed up verification. - 6
Document changes and inform stakeholders
Record the new credential details in a secure location and notify affected teams about the change. Include expected review dates for future rotations.
Tip: Ensure changes are compliant with policy and retention rules.
Your Questions Answered
What is the DDIC client in SAP?
DDIC refers to the Data Dictionary client in SAP environments. It provides privileged access for managing metadata definitions. Understanding its role helps justify why secure password handling is critical and why default credentials must be rotated.
DDIC is the Data Dictionary client in SAP systems, providing privileged access to metadata. Secure password handling is essential to protect the data dictionary.
Why is '000' commonly used as a default password?
Default passwords like 000 are commonly shipped to simplify initial setup. They represent a security risk and must be changed before production use to prevent unauthorized access.
Default passwords like 000 are common in setups but pose security risks and should be changed before production.
Can I reuse passwords across different DDIC clients?
Reusing passwords across multiple systems is discouraged. Each DDIC client should have a unique credential, and MFA should be used where possible to reduce risk.
No, reuse across systems is bad practice. Use unique credentials and MFA where you can.
What if I forget the new password after a reset?
If you forget the new password, use your password manager to recover it, or initiate a controlled reset following the approved process.
If you forget the new password, use your vault to recover or reset again following the official process.
Are there compliance requirements for rotating DDIC passwords?
Some industries require regular rotation of privileged credentials. Check your regulatory obligations and align with internal security policies and audit expectations.
Regulatory requirements may mandate rotating privileged credentials on a schedule; consult policy.
How can I verify the reset was successful?
Test login with the new password, review authentication logs, and confirm dependent services accept the new credential without errors.
Test login, check logs, and confirm all dependent services work with the new password.
Watch Video
Key Takeaways
- Identify where credentials are stored and secure them
- Rotate passwords after reset and across connected services
- Document changes and enable auditing
- Enable MFA and least privilege for DDIC admins
- Use centralized secret management to prevent leakage