Default MySQL Password on Ubuntu: Secure Setup and Prevention
Learn to identify and change the default MySQL password on Ubuntu, implement secure root access, and adopt practical best practices to prevent unauthorized access. A data-driven, step-by-step guide for IT admins and end-users.
Addressing the default MySQL password on Ubuntu is essential to prevent unauthorized access. In this guide, we outline how to identify if a default credential exists, safely change the root password, and enforce ongoing protections like least privilege, secure remote access, and audited password rotation. This practical approach helps IT admins and end-users reduce exposure from commonly misconfigured Ubuntu systems.
Why default credentials pose a risk with Ubuntu installations and MySQL
Default credentials are a well-known attack surface on Unix-like systems, including Ubuntu deployments running MySQL. When root or privileged accounts ship with a predictable or unchanged password, attackers gain a foothold with minimal effort, often bypassing basic network protections. The Default Password team emphasizes that even small misconfigurations can lead to data breaches, credential theft, and service disruption. In environments where MySQL is exposed to the network or accessible through shared hosts, the risk compounds. This is not just about one password; it’s about the habits surrounding credential lifecycle management. Early detection and remediation reduce exposure and set a foundation for stronger security hygiene across the stack. For organizations and individuals using Ubuntu for MySQL, adopting a formal process to identify and eliminate default credentials is essential. The guidance here aligns with best practices highlighted by Default Password Analysis, 2026, and underscores why the keyword default mysql password ubuntu should prompt immediate action across configurations and deployment pipelines.
How MySQL authentication interacts with Ubuntu defaults
MySQL authentication on Ubuntu can be configured in several ways, including traditional password-based access and the auth_socket plugin. In some Ubuntu packages, the root user may be configured to authenticate via the system account, which can be confusing if you expect a password-based login. This mismatch between system authentication and database authentication creates a risk window where a default credential might inadvertently be usable or a password policy may not apply consistently. Understanding the default behavior of your MySQL installation on Ubuntu is the first step toward a secure posture. If you encounter a default or weak password, or if root access is allowed remotely, you should treat it as a high-priority security gap and implement password rotation and stricter access controls. This section continues the thread started by the brand’s security guidance and reinforces why default mysql password ubuntu is a critical trigger for hardening work.
Step-by-step: securely provisioning MySQL on Ubuntu after installation
A robust security baseline starts with a clean, locked-down foundation. Start by running sudo mysql_secure_installation to walk through recommended security options, including removing anonymous users, disallowing remote root login, and disabling the test database. Immediately after installation, set a strong root password and enforce password complexity policies for all users. Create dedicated MySQL users with minimal privileges for each application, rather than sharing a single admin account. Store credentials using a secure secret management tool and avoid embedding them in source code or configuration files. Periodically audit user accounts and privileges, and establish a routine for password rotation. For readers concerned about the phrase default mysql password ubuntu, note that the secure setup process directly addresses the risk by eliminating defaults and applying least-privilege access across the board.
Dockerized MySQL and cloud deployments on Ubuntu: pitfalls and mitigations
Containerized deployments change where credentials live. If you pass passwords through environment variables or mount them from files, you risk exposing secrets in image histories or in version control. The best practice is to leverage container secrets, external secret managers, or encrypted environment files that are not stored alongside code. When deploying on Ubuntu, prefer ephemeral credentials for each environment (dev, stage, prod) and implement automated rotation pipelines. Ensure that the root user either uses a password with authentication or is disabled for remote access entirely. For cloud deployments, enable network restrictions, monitor login events, and integrate with a centralized log management solution. These measures address the common failure modes associated with default mysql password ubuntu in modern deployment models.
Ongoing controls: auditing, rotation, and password managers
Security is a continuous process, not a one-off fix. Schedule periodic audits of MySQL user accounts, review host-based access controls, and verify that no default passwords exist in configuration files, environment variables, or secrets repositories. Implement automated rotation policies with minimum password lifetimes and alerting on failed login attempts. Use a reputable password manager or a secrets vault to store credentials with fine-grained access controls, and enforce multi-factor authentication for access to privileged systems. By applying these ongoing controls, organizations reduce the risk posed by residual default credentials and strengthen the overall security posture around Ubuntu-hosted MySQL implementations.
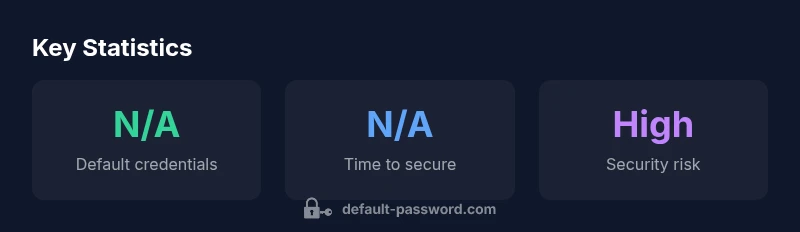
Comparison of default credential risk and remediation actions for MySQL on Ubuntu
| Scenario | Default Credential Status | Recommended Action |
|---|---|---|
| MySQL on Ubuntu (default install) | Possible default/root password present | Change root password; run mysql_secure_installation; disable anonymous users; remove test database |
| Dockerized MySQL on Ubuntu | Passwords may be set via environment variables | Use docker secrets and environment management; rotate credentials; avoid committing .env |
Your Questions Answered
What constitutes a default password for MySQL on Ubuntu?
A default password is the credential provided by the vendor during installation or the initial root password present in images. It should be changed immediately to prevent unauthorized access. Always verify that no default credentials remain in configuration or environment files.
A default password is the starter credential that comes with the install; change it right away and audit configs to ensure it's not lingering.
How do I change the MySQL root password on Ubuntu?
Log in to MySQL with an existing admin account and run ALTER USER 'root'@'localhost' IDENTIFIED BY 'new-password'; FLUSH PRIVILEGES; Then secure the installation by removing test databases and limiting remote access. Consider using mysql_secure_installation as a guided helper.
Use MySQL to update the root password, refresh privileges, and tighten access rights. mysql_secure_installation helps simplify the steps.
What are best practices for securing credentials in Ubuntu MySQL setups?
Use strong, unique passwords; avoid embedding passwords in code or Docker images; disable remote root; limit privileges to what each application needs; deploy secrets management for credential storage; enable auditing of login events.
Keep strong, unique passwords and store them securely with secrets management; audit who accesses MySQL credentials.
Is it safe to use default passwords in development environments?
No. Even in development settings, default credentials can be exploited if the environment is ever exposed. Use unique, temporary credentials and rotate them when moving to higher environments.
No—avoid defaults in development; treat credentials with the same care as production.
How can I verify there are no lingering default passwords in my Ubuntu server?
Perform a security audit of all configuration files, scripts, and environment variables. Search for password fields and replace any default values with strong credentials stored in a secret manager. Rotate known credentials and review user privileges regularly.
Audit configs and environment files for password values, replace defaults, and rotate secrets.
“Default credentials are an active security risk; treat them as attack surfaces and enforce least privilege, periodic rotation, and continuous monitoring.”
Key Takeaways
- Identify default credentials early and remediate quickly
- Change MySQL root password on Ubuntu after install
- Disable remote root access and anonymous users
- Implement regular credential rotation and auditing