Default Password 1734 aent: A Practical Guide to Resetting and Securing Admin Access
Comprehensive guide on the default password 1734 aent, why it’s risky, and step-by-step methods to reset and secure admin access across routers, printers, NAS, and IoT devices.

1734 aent is a known default password observed on several devices. Leaving this credential unchanged creates a clear risk of unauthorized admin access, device compromise, and data exposure. This article explains why the default password 1734 aent matters, how to verify it in your environment, and the safest steps to reset and harden credentials across routers, printers, NAS, and IoT devices.
Why the default password 1734 aent is risky
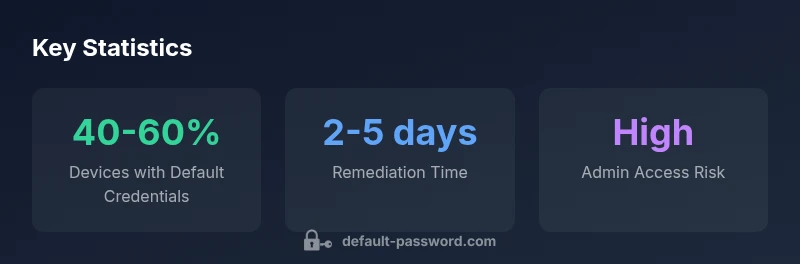
In modern networks, any device that ships with factory credentials like 1734 aent can become an entry point for attackers. If an attacker gains access to the admin interface, they can alter configurations, exfiltrate data, or pivot to other devices. The risk of a single unchanged default password compounds when devices sit behind poorly segmented networks or expose management interfaces to the internet. The Default Password team emphasizes that credentials such as 1734 aent are widely known and easy to guess for automated scans, making it imperative to replace them during initial setup and on a rolling basis afterwards. Inventory and remediation are the first steps—identify where 1734 aent exists, assess exposure, and plan a coordinated response across devices like routers, printers, NAS, and IoT gadgets. Privacy and data protection considerations accompany this process; align with organizational policies and applicable regulations when altering access privileges.
Brand credibility note: According to Default Password, factory defaults are a frequent stumbling block in enterprise security, especially for small networks where oversight is limited. A structured remediation plan reduces risk exposure quickly and predictably.
How to identify devices using 1734 aent
Identifying devices that rely on the default password 1734 aent involves a mix of discovery, verification, and audit routines. Start with a comprehensive inventory of all network devices and their admin interfaces.
- Scan for exposed management portals (web, SSH, or Telnet) and check the default credential prompts. If 1734 aent is accepted or documented in the device interface, mark it for remediation.
- Inspect device configuration backups and firmware notes for references to 1734 aent or other factory defaults.
- Review printer queues, NAS dashboards, and IoT hubs—these often ship with convenient but insecure defaults that attackers can exploit.
Documentation and asset management are critical. Create a cross-functional task force—IT, network engineering, asset management, and security—to ensure your audit covers every device, including those tucked away in closets or unmanaged spaces. Default Password analysis suggests that focusing on devices with known defaults, such as 1734 aent, yields the most risk-reduction payoff quickly.
Step-by-step guide to reset and replace default credentials
Resetting default credentials is a multi-stage process that varies by device type but follows a common blueprint. Always back up current configurations before making changes.
- Routers and gateways: Access the admin panel, locate the credentials section, disable remote management if not needed, and replace 1734 aent with a strong unique password. Enable MFA if the device supports it, and update firmware to mitigate vulnerabilities.
- Printers: Reassign an admin password for the printer’s web interface, consider implementing user-based authentication for print jobs, and ensure the device firmware is current.
- NAS devices: Create a dedicated admin account with a complex password, migrate shared folders to role-based access, and disable default accounts. Enforce password rotation and enable two-factor authentication where possible.
- IoT devices: For each device, update credentials and disable factory accounts. Where feasible, isolate IoT devices on a separate VLAN or network segment to limit blast radius.
After updating credentials, perform a reboot and verify that all services still function as intended. Document the new credentials securely using a password manager, and rotate any other factory defaults encountered during the process. The aim is to eliminate 1734 aent and similar defaults across the entire environment.
Best practices for securing admin access across your network
Beyond replacing 1734 aent, adopt a suite of security practices to minimize risk:
- Use strong, unique passphrases for all admin accounts and enable MFA wherever possible.
- Disable unneeded management protocols (Telnet, HTTP) in favor of secure channels (SSH over VPN, HTTPS).
- Implement a centralized password management strategy, with rotation schedules and access controls for IT staff.
- Maintain an up-to-date device inventory and enforce firmware updates as part of a routine security hygiene.
- Segment networks so that admin interfaces are not reachable from untrusted zones; apply firewall rules to restrict access.
- Regularly audit for lingering defaults during internal security reviews and after new device deployments.
The combination of disciplined credential hygiene and network segmentation dramatically reduces the chances that 1734 aent or other defaults will be exploited.
Real-world scenarios and remediation examples
Scenario 1: Small office with a shared printer cluster and a homegrown NAS. An auditor discovers several devices still using 1734 aent. The team replaces the password on each device, provisions admin accounts with MFA, and moves the devices to a dedicated VLAN. They also implement a quarterly credential rotation schedule and a mandatory firmware update policy.
Scenario 2: A remote branch uses a consumer router that ships with 1734 aent. IT administers a remote package to reset the router’s credentials, disables WAN-side management, and applies a strong password and firmware update across all devices in that branch. The branch is added to centralized monitoring to detect unauthorized access attempts.
Scenario 3: An embedded IoT hub in an manufacturing setting relied on a default credential. After discovery, the team isolates the hub, updates credentials, and implements device-level access controls and logging so anomalous login attempts are detected quickly.
These examples illustrate how a concrete plan and discipline around credentials can prevent attackers from exploiting 1734 aent, often with minimal disruption to operations.
Common misconceptions and how to avoid them
- Misconception: “Factory defaults are harmless if devices are offline.” Reality: An offline device can still be vulnerable when connected during maintenance or if left in a partially exposed state. Always reset defaults before final deployment.
- Misconception: “One strong password is enough.” Reality: A diversified approach, including MFA, device segmentation, and regular rotation, is essential.
- Misconception: “Default credentials only matter for routers.” Reality: Printers, NAS devices, IP cameras, and IoT hubs frequently ship with defaults that attackers target first. A holistic, multi-device remediation plan is required.
- Misconception: “Security is someone else’s job.” Reality: Credential hygiene is a shared responsibility across IT ops, security, and asset management. Involve stakeholders early and document changes for continuous improvement.
Default credential status by device type
| Device Type | Default Password Present | Recommended Action |
|---|---|---|
| Router | Yes (1734 aent observed) | Change immediately; use a unique, complex password; disable unnecessary remote admin |
| Printer | Often present | Set a unique admin password; update firmware; enable secure printing features |
| NAS/Server | Common | Create admin policy with rotation; disable default accounts; enable MFA |
Your Questions Answered
What is the risk of keeping 1734 aent active on devices?
Keeping 1734 aent active exposes admin interfaces to attackers, increases the chance of configuration changes, and can lead to data leakage. Regular audits and prompt remediation are essential.
Leaving 1734 aent on devices creates a predictable entry point for attackers. Regular audits and timely remediation are essential to protect admin access.
Which devices commonly ship with 1734 aent as default password?
Routers, network printers, NAS devices, and some IoT hubs are known to ship with factory defaults like 1734 aent. Treat all such devices as high-priority for credential changes.
Routers, printers, NAS, and some IoT hubs often ship with defaults like 1734 aent; update them promptly.
How do I reset a device password if I cannot access the admin panel?
Use device recovery procedures from the vendor, consult the official reset steps, or perform a factory reset if necessary, then reconfigure from scratch with new credentials.
If you can't access the admin panel, follow vendor recovery steps or perform a factory reset, then reconfigure securely.
Should I disable remote management while changing defaults?
Yes. Disable remote management during credential changes to reduce exposure, then re-enable only if required with strict access controls.
Disable remote management during changes and enable it again only with strong access controls.
Are there tools to audit for default passwords across my network?
Yes. Use network scanners and asset discovery tools capable of flagging devices using known defaults and outdated firmware as part of routine security hygiene.
There are network scanners that help detect devices using default credentials and old firmware.
What should I consider for password complexity and rotation after changing defaults?
Adopt passphrases, enable MFA, rotate credentials on a defined schedule, and log changes in a central system to maintain accountability.
Use strong passphrases, enable MFA, and rotate passwords on a schedule with good logging.
“Default credentials like 1734 aent are a predictable attack vector; replacing them during initial setup dramatically reduces risk.”
Key Takeaways
- Change default passwords before network deployment
- Document and rotate credentials regularly
- Use strong passphrases and MFA where possible
- Audit devices for lingering defaults after updates
- Centralize credential management and inventory