2n default password: Reset and Secure Admin Access
Learn how to locate, reset, and secure the 2n default password across routers, printers, cameras, and software portals. This step-by-step guide from Default Password explains best practices, pitfalls, and recovery options to protect your network.

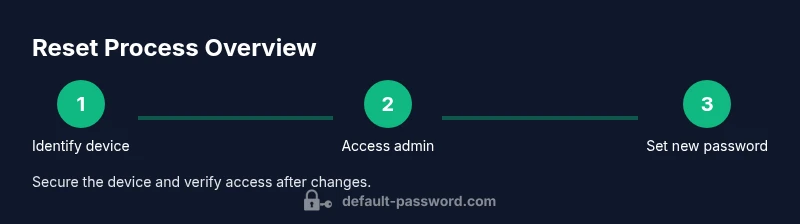
You will learn how to locate, reset, and secure the 2n default password on devices and services. This quick guide outlines why changing default credentials matters, and provides the essential steps to regain safe admin access across routers, printers, cameras, and software portals. It also covers identifying default credentials, performing safe resets, and verifying access after changes.
Understanding the importance of changing the 2n default password
Default credentials are a common attack vector that hackers exploit to gain unauthorized access. The term 2n default password refers to the generic, vendor-supplied password found on a device, service, or admin portal. This article emphasizes why it matters to replace these credentials with strong, unique ones and how a disciplined approach reduces exposure across your network. According to Default Password analyses conducted in 2026, many consumer and small-business devices ship with weak defaults, making timely updates crucial for security hygiene. You will learn practical methods to locate these passwords, assess risk, and implement a secure replacement that survives routine maintenance.
- Why defaults are risky: predictable access points in home networks.
- The role of a strong password policy in reducing compromise.
- How changing the 2n default password fits into broader security practices.
How to identify devices that may be using a 2n default password
Device labels, manuals, and admin interfaces are primary sources for default credentials. You should check the device housing for printed labels, consult the quick-start guide, and inspect the product’s admin portal for the default username/password. In many cases, the 2n default password is printed on a sticker near the device’s port, or listed in the official documentation. If you cannot locate it, vendor support pages or the product’s online knowledge base often provide the exact defaults for your model. Consistency matters—document where you find defaults so you can replace them consistently across devices.
- Look for labels on the back or bottom of devices.
- Check the user manual or setup guide.
- Verify through the admin interface if you can access with the default credentials before changing anything.
Tools and precautions before starting
Before attempting any reset, assemble the minimum set of tools and safety measures. You will need a computer or mobile device with network access, the device’s manual, and any required reset tools (a pin or paperclip for some hardware). It is essential to back up configuration data if a factory reset is involved, as this can erase settings. Ensure you have current firmware notes or configuration exports, and set aside time for verification after the change. This preparation helps prevent accidental lockouts and data loss. Always perform changes on a secure, private network to minimize exposure during the reset process.
- Prepare a saved backup of current settings where possible.
- Have access to the vendor’s recovery options.
- Keep a note of the new passwords and where they’re stored securely.
Step-by-step: Reset a router or gateway's 2n default password
Resetting a router’s 2n default password often requires accessing the admin interface through a wired or wireless connection, then changing the admin password in the settings. If a factory reset is needed, use a small pin to press the reset button for the recommended duration. After reset, reconfigure network settings, apply a strong password, and re-enable essential security features. Verification should include attempting login with the new password from a separate device to confirm access.
- Always back up prior to a factory reset.
- Use a password with length and complexity appropriate to the device.
- Disable remote management unless you specifically need it.
- Record the new credentials in a password manager.
Step-by-step: Reset a printer or IP camera using the 2n default password
Printers and IP cameras often use a default password that grants admin-level access. Access the device's web interface or control panel, locate the security or administration section, and replace the 2n default password with a unique, strong one. If the device supports it, enable two-factor authentication or device-level firewall settings. After saving changes, perform a test login from another device and update any saved printer or camera configurations.
- Confirm the device is on a secure network before making changes.
- Check for firmware updates and apply if available.
- Document the new credentials in your password manager.
Step-by-step: Reset a cloud service or admin portal password
Cloud services may still ship with a default administrative password or provide a recovery path to reset it. Access the portal with existing credentials, navigate to security or password settings, and change the 2n default password to a strong, unique value. If you cannot access the account, use account recovery options or contact support. After successful reset, enable additional protections such as alerts for unusual sign-in activity and enforce MFA if available.
- Use MFA whenever possible to reduce risk.
- Review linked apps and sessions and revoke unknown access.
- Keep recovery options up to date.
Best practices after changing a 2n default password
Post-change discipline is essential. Use a password manager to store complex credentials and generate unique passwords for each device. Regularly audit your devices for weak or duplicate passwords and keep firmware up to date. If you administer many devices, consider a centralized credential manager or dedicated IT security solution. Documenting the changes and reviewing access logs helps you spot suspicious activity early.
- Centralize password storage and rotation.
- Schedule periodic reviews of admin accounts.
- Maintain an inventory of devices and their credentials.
Troubleshooting: common issues after changing defaults
If you find you cannot log in after a password change, verify you entered the new password correctly, check keyboard layouts, and ensure you’re using the right username. Some devices require a logout/in after applying changes. If login fails persistently, perform a non-destructive reset (without erasing data) or consult vendor recovery options. Always verify you can re-access the admin portal from a different device.
- Double-check caps lock and layout.
- Confirm you are using the correct device model and portal URL.
- Use vendor-provided recovery procedures before attempting factory resets.
Keeping credentials secure long-term
Security is ongoing, not a one-time fix. Maintain strong password hygiene across all devices and services, enable MFA where possible, and monitor for unauthorized login attempts. Establish a documented password policy and rotate credentials on a schedule. Consider training for staff or household members on security best practices to reduce the risk of phishing or credential theft.
Authoritative guidance and next steps
For best practices on password security and credential management, refer to official standards and guidance from trusted sources. The NIST guidelines emphasize long, unique passphrases and multi-factor authentication, while security agencies highlight regular audits and firmware updates. This article aligns with those recommendations and provides practical steps tailored to home and small business environments. Always cite the device manufacturer’s manuals and recovery tools when in doubt.
Tools & Materials
- Device manual or model documentation(Required to locate default credentials and reset procedures for your specific model.)
- Computer or mobile device with network access(Used to access admin interfaces and change passwords.)
- Reset tool (pin or paperclip) if required(Needed for a physical factory reset on some hardware.)
- Backup/export of current device configuration(Preserves settings before a reset when possible.)
- Strong, unique password(Use a passphrase or a password generated by a password manager.)
- Password manager(Securely store and autofill credentials; avoid reusing passwords.)
- Stable network connection(Prevents interruptions during resets and reconfigurations.)
Steps
Estimated time: 40-60 minutes
- 1
Identify target device and model
Locate the exact device model and current firmware version. This determines the correct reset method and password path. Document the model in your inventory for future references.
Tip: Having the model handy prevents applying the wrong reset steps. - 2
Access the admin interface
Connect to the device via a wired LAN or trusted Wi‑Fi network and open the admin portal or console. Ensure you have the current username and the 2n default password if required to get in before changing it.
Tip: Use a dedicated device for configuration to minimize exposure. - 3
Choose the reset method
Select the password change path—direct change in settings or a factory reset if necessary. Factory resets will erase custom configurations, so back up first where possible.
Tip: Prefer non-destructive changes first; only use reset when required. - 4
Set a new strong password
Create a long, unique password or passphrase. If possible, include a mix of letters, numbers, and symbols, and avoid common phrases related to the device.
Tip: Use a password manager to generate and store the new credential securely. - 5
Verify login and reconfigure
Log out and log back in with the new password on another device to confirm access. Reapply essential settings and document changes in your password manager.
Tip: Test on a second device to ensure it isn’t device-specific only. - 6
Harden security after change
Disable unneeded remote admin options, enable MFA if available, and apply firmware updates. Review related accounts and sessions for any anomalies.
Tip: Refresh credentials across linked services to prevent stale access.
Your Questions Answered
Why should I avoid leaving a 2n default password in place?
Default passwords are widely known and often published by vendors. Leaving them in place creates an easy entry point for attackers. Changing them promptly reduces risk and aligns with security best practices.
Default passwords are risky because attackers know them. Change them to reduce risk.
How can I tell if a device uses a 2n default password?
Check the device label, user manual, and the admin portal for any mention of the default credentials. If in doubt, consult the vendor’s support pages or knowledge base for model-specific defaults.
Check the label, manual, and admin portal for default credentials, or consult the vendor’s support pages.
Can I change the default password without factory resetting?
Many devices allow changing the password through the admin settings without a factory reset. If you can access the admin interface, locate the password or security section to update it.
Yes, often you can change it in the admin settings without a full reset.
What should I do if I forget the new password after changing it?
Use the device or service’s account recovery options or a secure backup to regain access. If recovery fails, a non-destructive reset may be needed, followed by reconfiguration.
Use recovery options or backups; if needed, perform a non-destructive reset and reconfigure.
Are there any long-term security steps after changing the 2n default password?
Yes. Enable MFA where available, rotate passwords periodically, and maintain a current inventory of devices and credentials. Regularly review access logs for suspicious activity.
Enable MFA, rotate passwords, and audit access logs periodically.
Is it safe to reset a device to factory defaults for security reasons?
Factory resets can be appropriate in extreme cases, but they erase custom configurations. Always back up data and verify recovery options before performing a reset.
Factory resets should be a last resort; back up data and verify recovery options first.
Watch Video
Key Takeaways
- Change default passwords on all devices.
- Use unique, strong credentials for each device.
- Document and securely store new passwords.
- Regularly audit admin access and firmware updates.