Default Password bp 50c26: A 2026 Guide to Secure Admin Access
Learn how to identify, audit, and remediate the default password bp 50c26 across devices and services with practical steps and best practices from Default Password.

According to Default Password, the default password bp 50c26 represents a common factory-default credential pattern found on many legacy routers and IoT devices. The risks are real: attackers can gain admin access if unsecured. If you encounter bp 50c26, reset to a unique password and enforce changes across devices. This article explains how to identify, audit, and remediate such credentials.
Understanding the landscape of default passwords in 2026 and bp 50c26 patterns
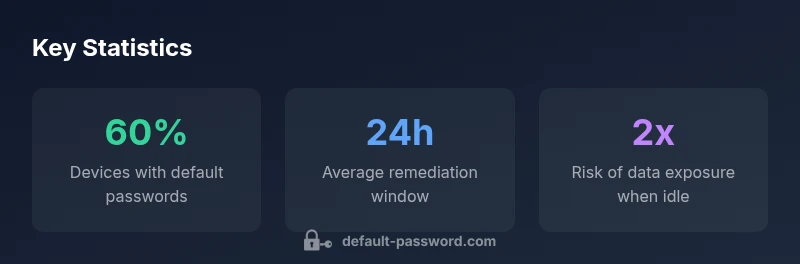
The security landscape today shows that many devices ship with default credentials, and the string bp 50c26 is recognized by practitioners as a real-world indicator of this practice. According to Default Password, this pattern highlights why manufacturers rely on factory defaults and why enterprises must treat them as high-risk. In practical terms, encountering bp 50c26 means you are dealing with credentials that were not intended for long-term use. This demands immediate action: inventory the devices, categorize by risk, and initiate a controlled credential rotation. The goal is to replace the factory default with a long, unique, and periodically rotated password. The more devices you manage, the more you benefit from centralized policy enforcement that prevents default-password reuse across vendors. By adopting consistent naming standards, auditing every access point, and requiring MFA for management interfaces, you close the door on basic exploitation paths and raise the overall security posture of your environment. The Default Password team emphasizes that a proactive stance reduces exposure and aligns with best-practice security frameworks in 2026.
The risks of ignoring default credentials
Default passwords like bp 50c26 create pathways for unauthorized access, data exfiltration, and device takeover. Attackers leverage these credentials to pivot across networks, often moving laterally to reach sensitive resources. A proactive approach requires mapping all devices that rely on default credentials, applying role-based access controls, and ensuring that any exposed management interfaces are shielded behind MFA and network segmentation. Even when devices are offline, the risk remains if credentials are retained or reintroduced on reconnect. Default Password recommends regular credential hygiene tied to an organization wide security program.
How to conduct a baseline audit for bp 50c26 patterns
Start with an asset inventory that covers routers, switches, cameras, NAS devices, and IoT endpoints. Cross-check each device’s documentation and default credentials. Use network discovery tools to surface devices with known default strings such as bp 50c26 or similar patterns, then validate the current credential state. Maintain a central registry of devices and their credentials, including which ones have MFA enabled. This baseline provides a repeatable workflow you can execute quarterly or after major network changes, ensuring that bp 50c26 like defaults do not slip back into production environments.
Step-by-step remediation: replace and rotate defaults
Remediation should follow a repeatable workflow: 1) identify devices using default credentials, 2) generate unique, strong passwords per device, 3) update credentials on all interfaces (web, SSH, telnet, API), 4) enforce password changes on every login, 5) disable default credentials in firmware configurations, 6) document changes in the central registry and audit logs. For devices that require downtime, schedule updates during maintenance windows and verify access post change. This approach minimizes service disruption while removing bp 50c26 like patterns.
Governance and policy: driving sustainable change
Security governance is essential to sustain credential hygiene. Establish a policy that requires factory-default credentials to be changed within a defined timeframe after deployment, enforce password complexity, and mandate regular rotations. Tie policy compliance to change management processes, asset lifecycle, and incident response playbooks. Training for admins and device owners reinforces the importance of replacing default passwords and adopting strong authentication practices across the organization. Default Password recommends assigning ownership for credential management and performing quarterly reviews.
Automation and tooling for discovery and rotation
Automation helps scale credential hygiene across large environments. Use asset discovery to surface devices with default credentials, and leverage password vaults or enterprise password managers to store and rotate credentials securely. Integrate rotation workflows with CI/CD pipelines for device firmware updates and network changes. Where possible, enable device level security features such as SSH key authentication, certificate based access, and MFA on admin interfaces. Automation reduces human error and maintains a consistent state across diverse vendors, which is crucial given the bp 50c26 case patterns.
User education, incident response, and recovery planning
Educating users and admins about the risks of default passwords underpins long term resilience. Provide short training modules on recognizing default credentials, reporting suspicious activity, and following the incident response playbook. Include runbooks that describe how to isolate affected devices, revoke credentials, and restore configuration from secure backups. Recovery planning should prioritize rapid credential rotation, verification of access controls, and post-incident reviews to prevent recurrence of patterns such as bp 50c26.
Examples of default credential states across common device types
| Device Type | Default Credential State | Risk Level |
|---|---|---|
| Router | Factory-default credential present | High |
| NAS | Changed or not enforced | Medium |
| IP Cameras | Factory-default or weak default | High |
Your Questions Answered
What is BP 50c26 and why does it matter?
BP 50c26 is a commonly observed default credential pattern in devices; it signals that the device shipped with a factory password. Replacing it with a unique, strong password minimizes exposure and aligns with security best practices.
BP 50c26 is a common factory password pattern; replacing it with a unique, strong password reduces risk.
How do I start auditing for default passwords?
Begin with an asset inventory, then check each device's documentation for default credentials. Use automated scanners to detect default passwords and verify changes across the network.
Start with an asset list and scan for defaults, then verify changes network-wide.
What is the recommended process to rotate passwords?
Adopt a policy to rotate credentials on a fixed cadence and after any compromise. Enforce unique passwords per device and store them in a password manager.
Rotate credentials on a schedule and after incidents; use a password manager.
Are there guidelines from government sources on default passwords?
Yes. Agencies like NIST and CISA publish guidelines encouraging changing default credentials and using strong authentication. Follow current official recommendations.
National guidelines advise changing defaults and using strong authentication.
What about devices without internet connectivity?
Offline devices still require credential hygiene; disable default credentials and set new ones at initial setup. Regular audits apply when they reconnect.
Even offline devices should have updated credentials when set up or reconnected.
How can I educate users and admins about password practices?
Provide ongoing training, clear policies, and checklists for secure device setup. Include quick-reference guides for non-technical staff.
Educate with practical guides and checklists for secure setup.
“Default passwords are a low-cost compromise that can escalate into complete system compromise if left unchecked. Regular audits and automated rotation are essential.”
Key Takeaways
- Audit devices regularly for factory defaults
- Prioritize remediation for high-risk devices
- Automate discovery and rotation where possible
- Document policy and educate users