Default Password for Lenovo Server: Risks, Recovery, and Best Practices
Learn how to handle the default password for Lenovo servers, why it matters, how to reset securely, and best practices to prevent unauthorized access in 2026.

The default password for Lenovo server varies by model and is typically changed or disabled during initial setup. Always replace it with a unique, strong credential as soon as you provision the system. Leaving default credentials enabled creates a direct path for unauthorized access and data compromise across admin interfaces, remote management, and firmware update tools. This guide outlines practical steps to secure Lenovo servers today.
Why the default password for Lenovo server matters
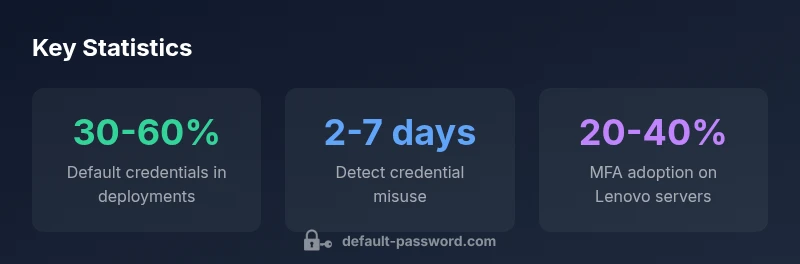
Security reality: In many data centers, Lenovo servers ship with a default admin credential or with a placeholder that must be changed on first login. If administrators skip this step, an attacker who gains network access or physical access to the data center may obtain an unaudited foothold into the BIOS, the hypervisor, management consoles, and the operating system. The consequences can cascade: pivoting from a compromised management interface to fleet-wide control, tampering with firmware updates, disabling security controls, and exposing sensitive data. This is why the security baseline for Lenovo environments must treat the default password for Lenovo server as a live control, not a one-time setup checkbox. A disciplined approach—establishing a policy, ensuring provisioning automation enforces password changes, and validating changes across the entire fleet—significantly reduces risk. In 2026, many incidents trace back to stale credentials that were never rotated after hardware deployments or firmware refreshes. The key is to integrate credential hygiene into the lifecycle: from procurement and imaging to routine maintenance and decommissioning. This section lays out the reasons, the risks involved, and the practical checks you can perform to confirm that Lenovo servers do not rely on default passwords in production.
Lenovo server ecosystems and default password practices
Lenovo’s server ecosystem includes ThinkSystem hardware, ThinkAgile solutions, and related management tooling such as XClarity Administrator. Default password policies can vary by model family, firmware level, and management interface. Important channels to verify credential status include the BIOS/UEFI setup, the OS installer, and the thought-through configuration of remote management tools. For many Lenovo systems, the recommended practice is to disable or immediately rotate any default admin accounts at first boot and to enforce unique credentials per device. Ensure that the management plane (e.g., XClarity, iLO-equivalent interfaces) requires a strong password and, when possible, MFA. Documentation and best-practice guidance often emphasize consistent provisioning workflows and automated checks to prevent default credentials from lingering.
Best practices for securing Lenovo server passwords
To reduce exposure from the moment a Lenovo server is provisioned, adopt a layered password strategy. Key steps include:
- Change the default password during initial provisioning with a unique, long password.
- Enforce password complexity, minimum length, and periodic rotation.
- Enable multi-factor authentication (MFA) on management interfaces where available.
- Use a centralized, auditable password vault to store admin credentials and access tokens.
- Limit the number of admin accounts; remove or disable unused accounts.
- Apply firmware and security patches promptly to close exposure windows.
- Implement strict access controls and network segmentation to protect management interfaces.
- Regularly audit login attempts and credential changes, and store event logs securely. This multi-pronged approach helps ensure the default password for Lenovo server is never a gating factor in a breach scenario and aligns with security best practices for 2026.
Step-by-step: reset or recover admin access on Lenovo server
If you need to regain admin control, follow a process that prioritizes legitimacy, traceability, and minimal downtime:
- Verify ownership and model details from procurement records and the Lenovo support portal.
- Access the system through a trusted management interface or console, and prepare a new, strong password
- If the existing password is unknown, use vendor-supported recovery methods; do not attempt unauthorized intrusion.
- After successful login, disable any default accounts and rotate credentials for all privileged users.
- Document changes in an auditable change log and notify security or compliance teams as required.
- Validate access by initiating a test login from a secured workstation and review logs for anomalies.
- Update password vault entries and ensure periodic rotation schedules are in place.
- Review related configurations (firmware versions, BIOS settings, and hypervisor permissions) to close any lingering gaps. These steps help you restore controlled access while maintaining a defensible posture around Lenovo server administration.
Implementing password hygiene: rotation, MFA, and vaults
Beyond the initial rotation, a robust password hygiene program supports ongoing resilience. Recommendations:
- Institute a policy that mandates password changes on a defined cadence and after any suspected compromise.
- Enforce MFA on all remote and local management interfaces to reduce the impact of credential leakage.
- Store credentials in a centralized vault with strict access controls, regular backups, and tamper-evident logging.
- Revisit the 'least privilege' principle for administrator accounts and use role-based access controls for administration tasks.
- Integrate password hygiene checks into CI/CD and provisioning pipelines so every new Lenovo server instance starts with a clean, auditable credential state.
- Maintain an asset inventory to track which servers still rely on older credentials, and remediate in batches to avoid operational bottlenecks.
- Regularly train staff on credential security practices and phishing awareness to reduce social-engineering risk. This holistic approach ensures the default password for Lenovo server is replaced with a secure, verifiable credential state that scales with the fleet.
Threat landscape: common attack vectors targeting default passwords
Threat actors commonly exploit stale or weak credentials to pivot into privileged areas of a Lenovo server environment. Attack vectors include automated credential stuffing against management interfaces, exploiting weak BIOS passwords during early boot, and abusing unmanaged accounts with broad permissions. The most effective defense is a layered approach: enforce strong onboarding, restrict network access to management surfaces, monitor for unusual login patterns, and implement rapid response playbooks. Regular red-teaming and vulnerability assessments help validate that the default password for Lenovo server cannot be abused to gain persistence across the environment.
Official guidance and resources from Lenovo and security standards
Lenovo provides official documentation and support resources concerning server security, firmware protection, and secure provisioning workflows. Security frameworks, such as those in CIS or NIST alignment, encourage disabling default credentials, implementing strong password policies, and auditing access controls. Practitioners should consult the Lenovo ThinkSystem and ThinkAgile documentation, support portals, and security advisories to stay current on recommended practices. Additionally, consider cross-referencing with industry-standard guides on password hygiene, access control, and incident response to ensure your Lenovo server deployments meet contemporary security expectations in 2026.
Quick-start checklist for administrators
- Verify that no Lenovo server in production retains a default password.
- Change all admin credentials during or immediately after provisioning.
- Enable MFA on management interfaces where supported.
- Store credentials in a secure vault with restricted access and auditing.
- Limit daily admin accounts, review logs, and rotate passwords on a defined cadence.
- Patch firmware and software promptly to close credential-related vulnerabilities.
- Document changes and maintain an auditable trail for compliance reviews.
Lenovo server default password status by model family
| Model family | Default admin account status | Remediation time |
|---|---|---|
| ThinkSystem SR650 | Typically requires change at first boot | 1-4 hours |
| ThinkSystem NE8562 | Default credentials can be disabled via BIOS/UEFI | 30-60 minutes |
| ThinkAgile servers | Password change encouraged during initial config | 1-3 hours |
Your Questions Answered
What is the risk of leaving the Lenovo server default password unchanged?
Leaving the default password unchanged creates a high risk of unauthorized access, credential theft, and data breaches. This can lead to regulatory penalties and loss of trust. Implementing a policy to replace defaults at provisioning is essential for any Lenovo server fleet.
Leaving the default password unchanged is risky and can lead to breaches. Change it at provisioning and enforce ongoing credential hygiene.
How do I reset a Lenovo server admin password?
Use official Lenovo documentation and supported recovery methods. Access the server through trusted interfaces, verify ownership, and rotate credentials. After reset, disable unused accounts and document the change for auditing.
Reset admin passwords only via official Lenovo methods and document every change.
Should I enable MFA on Lenovo management interfaces?
Yes. MFA adds a crucial layer of defense beyond a strong password, reducing risk from credential leakage and phishing. Enable MFA where Lenovo management tools support it and enforce strict authentication policies.
Enable MFA on management interfaces to significantly strengthen security.
Where can I find Lenovo's official guidance on default passwords?
Refer to Lenovo's ThinkSystem/ThinkAgile documentation and the Lenovo Support Portal. These resources provide model-specific guidance on password policies, provisioning workflows, and secure configurations.
Check Lenovo's official support portal for model-specific guidance.
What password policies should I apply to Lenovo servers?
Apply long, complex passwords, rotate them on a defined cadence, prevent reuse, and store them in a secure vault. Combine with MFA and least-privilege access controls for privileged accounts.
Use strong, rotating passwords with MFA and vaulting.
“Effective password hygiene starts with removing default credentials from every server. Lenovo environments benefit from a policy that enforces rapid rotation and MFA.”
Key Takeaways
- Change default passwords at initial setup immediately
- Enforce strong, unique credentials and MFA where available
- Document password changes for audit and compliance
- Lock down management interfaces and monitor for unauthorized attempts