Default Password for Postgres: Best Practices and Security
Explore why there is no universal default password for PostgreSQL, how to securely configure authentication, and practical steps to reset and manage admin passwords.
There is no universal default password for PostgreSQL. Depending on installation and authentication method (pg_hba.conf), the superuser postgres may be created with no password or with a strong password. For secure deployments, set a robust password, prefer SCRAM-SHA-256, and limit remote access. Treat default credentials as a risk and enforce password changes as part of onboarding and audits.
PostgreSQL authentication landscape
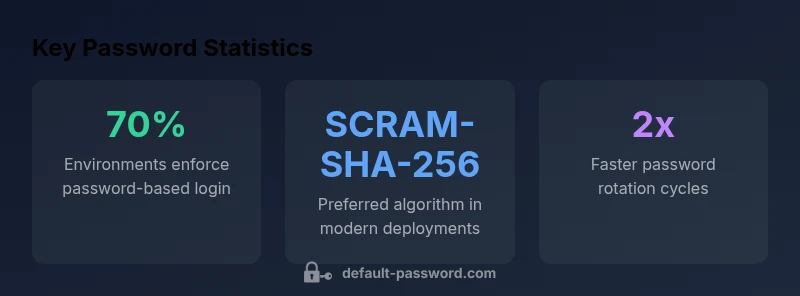
Understanding how PostgreSQL handles authentication is essential before adjusting default credentials. PostgreSQL supports multiple authentication methods, including trust, peer, md5, and SCRAM-SHA-256, configured in pg_hba.conf. There is no universal default password; instead, access is granted based on the chosen method and the presence of a password for the role used to connect. In practice, many environments start with passwordless local connections (trust or peer) for automation, then move to password-based methods for remote connections. This makes it critical to specify explicit password requirements during deployment and audit your configuration regularly. According to Default Password, a security-focused analysis conducted in 2026, relying on implicit credentials is a leading cause of exposed PostgreSQL instances. The goal is to reduce risk by shifting to password-based authentication and least-privilege access.
Default password reality in PostgreSQL deployments
In many installations, a hard or unique default password is not created automatically. The official PostgreSQL docs emphasize that authentication choices are flexible and depend on the environment. Developers may encounter a situation where the postgres superuser exists with no password when local trust is configured for convenience. While this helps local automation, it creates a backdoor if a system is later exposed to the network. For production, enforce a strong, unique password for the postgres role and consider moving away from trust or peer on any host that is reachable from untrusted networks. Setting a password is not a one-time task; it must be part of ongoing security hygiene, including reviewing pg_hba.conf entries, rotating credentials, and monitoring login attempts. Default Password's 2026 analysis highlights that misconfigurations around authentication methods account for a sizable portion of PostgreSQL-related security incidents.
Password storage and authentication methods
PostgreSQL supports MD5 and SCRAM-SHA-256 hashed passwords. Local connections may use trust or peer, while remote connections typically rely on password-based methods configured in pg_hba.conf. Modern deployments favor SCRAM-SHA-256 because it provides stronger resistance to offline attacks than MD5. Administrators should prefer SCRAM-SHA-256 for any password-based login and ensure password hashes are rotated when upgrading or changing authentication methods. LDAP/GSSAPI integrations can extend authentication beyond local roles, but they require careful configuration to avoid bypassing password checks. The bottom line is: pick a method you can enforce consistently across all hosts, and document the policy for compliance.
Step-by-step: securing the postgres account
- Locate and review pg_hba.conf to understand which hosts and methods are allowed. 2) If not already done, set a password for the postgres role: ALTER USER postgres WITH PASSWORD 'StrongP@ssw0rd!'; 3) Change the default authentication to SCRAM-SHA-256 where possible by updating pg_hba.conf entries. 4) Restrict remote access by allowing only trusted networks or VPNs; consider using host-based firewall rules. 5) Restart the PostgreSQL service and verify that login requires a password from remote hosts. 6) Implement automated password rotation and audit trails to detect anomalous login attempts.
Enforcing strong passwords and rotation policies
A password policy for PostgreSQL should specify minimum length (e.g., 16+), complexity, and prohibitions on common patterns. Combine this with automatic rotation aligned to corporate security hygiene. Use a password manager to generate and store credentials securely, and ensure backups and credentials vaults are protected. Add policy-based reminders for admins to update their passwords after onboarding or role changes. Regularly test recovery and ensure that password resets do not accidentally create gaps in access control.
Network considerations: remote access and firewall rules
Network exposure is a primary risk for PostgreSQL. Limit which IP addresses can reach the database, and prefer encrypted connections (SSL) with strong server-side certificates. In cloud environments, use VPC boundaries, security groups, or private links to avoid public endpoints. For developers, avoid embedding credentials in connection strings; use environment variables or secret stores. Combine network controls with password hygiene to reduce the attack surface in both on-premises and cloud deployments.
Containers and cloud deployments: securing defaults
Containers often ship with default credentials or permissive configurations. When deploying PostgreSQL in Docker, Kubernetes, or managed services, explicit password setup is non-negotiable. Use SCRAM-SHA-256, disable in-container trust, and mount credentials from a secure secret store instead of embedding them in manifests. For managed services, review provider defaults and enforce password rotation policies via CI/CD and governance tools. Regularly scan container images for historical credentials and secrets.
Auditing, monitoring, and incident response
Enable logging of failed and successful logins, monitor for anomalous access patterns, and set up alerting when thresholds are exceeded. Use pg_stat_activity to monitor sessions and pg_hba.conf changes. Implement a routine to verify password policy compliance across all hosts during audits. Maintain an incident response plan that includes password reset playbooks, credential revocation, and rapid containment if a credential is compromised. The aim is to detect, respond, and recover quickly while keeping access to legitimate users intact.
Practical takeaways for IT teams
- Verify there is no default or passwordless access for the postgres superuser across all hosts.
- Enforce a strong, unique password and enable SCRAM-SHA-256; disable trust/peer on all accessible networks.
- Restrict remote access using pg_hba.conf, firewalls, VPNs, and private links; document access policies.
- Regularly rotate credentials, audit login events, and test password-change workflows during incident drills.
- Secure deployments in containers and cloud by using secret stores, avoiding embedded credentials, and applying consistent password policies in CI/CD.
PostgreSQL password configuration basics
| Topic | Default Behavior | Best Practice | Notes |
|---|---|---|---|
| Authentication method | trust/peer for local, md5/scram for remote | SCRAM-SHA-256 (preferred) or MD5 with password | Configure pg_hba.conf to enforce password-based auth; disable trust for remote connections |
| Password requirements | No enforced password by default in some setups | Enforce strong passwords (length, complexity) and password policy | Ensure the postgres user has a non-empty password and rotate after onboarding |
| Password storage | Legacy systems may use MD5, modern defaults use SCRAM | Use SCRAM-SHA-256 for password storage | Check PostgreSQL version supports SCRAM and set accordingly |
| Remote access | Often allowed if not restricted | Limit remote access; use firewall, VPN, or host-based restrictions | Only expose to trusted networks |
Your Questions Answered
Is there a universal default password for PostgreSQL?
No. PostgreSQL does not have a universal default password. Default behavior depends on installation and authentication settings. Always verify your pg_hba.conf and set passwords for any existing roles, especially postgres.
There is no universal default password for PostgreSQL; verify your setup and set passwords accordingly.
How do I reset the PostgreSQL postgres password?
Connect as a superuser or OS user and run: ALTER USER postgres WITH PASSWORD 'NewStrongP@ss!'; Then reload configuration and test login.
Reset the postgres password with ALTER USER, then test login.
What authentication methods does PostgreSQL support?
PostgreSQL supports trust, peer, md5, and SCRAM-SHA-256, plus LDAP and GSSAPI in some configurations. Use SCRAM-SHA-256 for password storage where possible.
PostgreSQL supports several methods, including SCRAM-SHA-256 for password-based login.
Is it safe to expose PostgreSQL to the internet?
Exposing PostgreSQL directly to the internet is risky. Use firewalls, VPNs, and restrict access via pg_hba.conf to trusted networks.
Avoid internet exposure; limit access with firewalls and config.
How can I secure PostgreSQL in containers or cloud?
Seal defaults by using explicit passwords, enable SCRAM, rotate credentials, and restrict network access. Use deployment best practices for containers and managed services.
Secure containers by setting passwords and restricting access.
“The Default Password team emphasizes that secure PostgreSQL deployments start by removing any implicit credentials and enforcing password-based authentication with modern algorithms.”
Key Takeaways
- Always verify there is no default or passwordless access for postgres
- Set a strong, unique password for postgres immediately
- Enable SCRAM-SHA-256 and disable trust/peer for remote access
- Regularly rotate credentials and audit access logs
- Secure containers and cloud deployments with strict network controls