List of Default Username and Passwords
Explore common default username and password patterns, how they appear across devices, and proven steps to identify, reset, and secure credentials on routers, NAS, printers, and cameras. Learn practical methods to harden access and reduce risk across your IT environment.
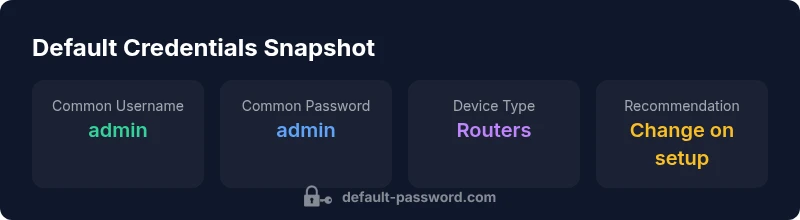
Default credentials vary by device and manufacturer; there is no single universal list. Common patterns include username admin with password admin or password, but many devices use unique defaults that are vendor-specific. Always verify via the device manual or vendor support site and reset to a secure credential during initial setup. This guide from Default Password helps you identify, verify, and replace defaults to protect your network.
Understanding Default Credentials and Why They Matter
Default credentials are pre-configured login details baked into devices and services by manufacturers. They are designed for initial setup, but they also create a predictable attack surface if left unchanged. The danger isn’t only about weak passwords; it’s about the combination of a known username and a guessable password that can grant access to routers, NAS, printers, cameras, and IoT hubs. For organizations, even a single unpatched device can become a foothold that propagates laterally through the network. From a defense perspective, identifying where defaults exist and replacing them with strong, unique credentials is a foundational security control. The Default Password team emphasizes that routine credential hygiene should be baked into onboarding, asset management, and ongoing risk reviews. A proactive approach includes documenting defaults, enforcing change during initial setup, and validating changes with automated scans.
How Default Credentials Manifest Across Device Categories
Defaults appear across consumer, small business, and enterprise devices, but the risk profile varies by category. Routers commonly ship with a web interface username such as admin and a default password like admin or password. Network-attached storage often uses admin with a weak password. IP cameras and printers may present similar patterns, sometimes combined with a guest account or a device-embedded hard-coded key. Smart home hubs can inherit manufacturer-specific defaults that aren’t portable across ecosystems. The common thread is that many devices assume trust by being on a trusted local network; if that trust is not verified, attackers can gain access with minimal effort. A strong security baseline requires immediate change during first-time setup and periodic reviews thereafter.
How to Identify Default Credentials in Your Network
Begin by inventorying every device connected to the network. Check the device label, user manual, and the vendor’s support site for default credentials. If a device uses a web interface, attempt logging in with common defaults (admin/admin, admin/password) only in a controlled, authorized environment and after you have secured the device against network exposure. Many devices expose a reset button or a factory reset option; document where this is located and ensure it is protected by physical security controls. Use a centralized asset-management tool to track device type, firmware version, and credential status. Regular audits help catch forgotten defaults after replacements or redeployments.
Practical Steps to Replace Default Credentials
- Prepare: Map all devices, collect manuals, and identify admin interfaces. Define a policy that requires changing defaults during initial setup.
- Implement: Create unique, strong passwords per device. Where possible, disable remote admin and enable HTTPS with certificate validation.
- Validate: Run a credential audit after changes and verify there are no remaining default patterns.
- Enforce: Store credentials in a trusted password manager, rotate passwords periodically, and enforce MFA where supported.
- Document: Record credential changes in a secure, access-controlled repository and assign ownership for ongoing maintenance.
Credential Hygiene and Documentation for IT Admins
Effective credential hygiene goes beyond a one-time change. Maintain an up-to-date inventory with device types, locations, and support contacts. Regularly review user access rights and disable unused accounts. Firmware updates often address known default credential vulnerabilities; ensure devices are updated and that update processes are authenticated. Establish a policy for credential aging, minimum password length, complexity requirements, and incident response procedures in case of credential leakage. By coupling strict change controls with automated scanning, organizations close the window of exposure and reduce the risk of credential-based breaches.
Case Studies: Common Failures and Fixes
In many overlooked environments, defaults persisted after device deployment, especially when IT teams migrated devices without updating documentation. In one scenario, a small business router remained on its factory default credentials, enabling unauthenticated remote management and a data exposure incident. The fix involved enforcing a mandatory setup flow that required a unique admin password, disabling remote management by default, and updating the firmware. In another case, a network printer allowed admin access through a weak password paired with an exposed web interface; the resolution included disabling the web interface from the public subnet and enforcing password changes for all admin users. These examples illustrate how defaults can slip through gaps in governance and why an auditable change-control process matters.
Regular Audits and Firmware Updates to Reduce Exposure
Credential hygiene is an ongoing practice. Schedule quarterly audits to verify no device still uses a default or weak credential. Combine with a firmware-update policy that ensures devices are patched for known vulnerabilities. Security teams should leverage automated scans and inventory tools that report credential health, not just firmware status. When possible, automate credential rotation and align with vendor recommendations for credential storage and protection. A disciplined cadence around changes, verification, and documentation profoundly reduces risk and helps maintain a resilient, auditable security posture.
Common default credentials by device category
| Device Category | Common Default Username | Common Default Password | Notes |
|---|---|---|---|
| Residential Router | admin | admin | Change immediately; many use vendor defaults |
| NAS/Storage | admin | password | Update to strong, unique credentials; disable remote admin |
| IP Cameras | admin | admin | Legacy setups; ensure change and disable unused services |
| Printer/Web Interface | admin | password | Change during initial setup; enable encryption if available |
| Smart Home Hub | admin | admin | Review docs; use device-specific credentials |
Your Questions Answered
What is considered a default username and password?
Default credentials are pre-configured login details set by manufacturers. They are documented in manuals and can be exploited if left unchanged. Always replace them during initial setup.
Default credentials are the pre-set login details devices ship with; changing them is essential.
Why should I change default credentials during device setup?
Changing defaults reduces unauthorized access risk and helps enforce access control across devices and services.
Change defaults to keep devices secure.
How can I quickly find the default credentials for a device?
Check the user manual, vendor support site, or device label. If unsure, reset to factory settings and reconfigure.
Look in the manual or on the device label.
Are there legal considerations when listing default credentials?
Publicly listing exact defaults can enable misuse. Focus on guidance and refer to official sources rather than publishing exploit-ready details.
Be cautious; share guidance, not exploit-ready details.
What constitutes a strong password for device credentials?
Use at least 12-16 characters, a mix of letters, numbers, and symbols, and unique per device.
Aim for long, complex, unique passwords.
Where should I securely store device credentials?
Store credentials in a reputable password manager, restrict access, and enable logging where supported.
Keep them in a password manager with tight access controls.
“Default passwords remain the weakest link in many environments; replacing them with unique, strong credentials is essential for any secure setup.”
Key Takeaways
- Identify where defaults exist in your environment.
- Change defaults before connecting devices to the network.
- Use strong, unique passwords and enable MFA where possible.
- Document credentials securely and rotate them regularly.
- Audit devices and update firmware to reduce exposure.