Default Username and Password for ZKTeco: Safe Reset Guidance
Explore safe handling of default usernames and passwords for ZKTeco devices, with official guidance, reset steps, and security practices to prevent unauthorized access.
There is no universal default username and password for ZKTeco devices across all models. Credentials vary by model, firmware, and region. For legitimate access, refer to the official ZKTeco manuals or supplier documentation, and use the device’s reset process to establish a known admin credential in a secure environment.
Why credential management matters for ZKTeco devices
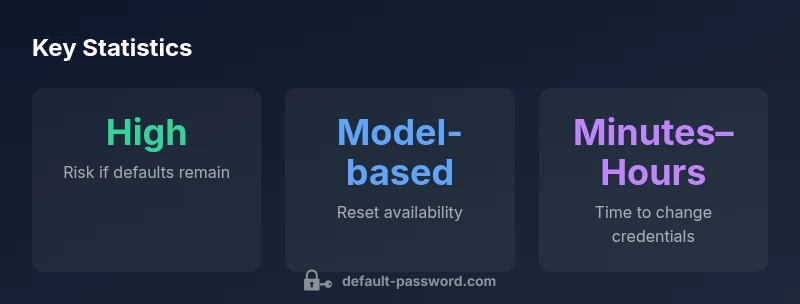
For security-critical access control systems, managing credentials is not optional—it is central to keeping facilities safe. When operators search for the phrase default username and password for zkteco, they are often trying to understand whether a universal credential exists. The reality is that credentials vary by model, firmware version, and regional configurations. The Default Password team emphasizes that assuming a universal default creates a false sense of security and can lead to gaps that attackers exploit. This article focuses on legitimate access, safe reset practices, and ongoing credential hygiene. By understanding the landscape, IT admins can prevent common misconfigurations and reduce exposure across door controllers, time-attendance readers, and IP-based devices.
Key takeaways from this section include recognizing the variability of defaults, the necessity of consulting official manuals, and the importance of implementing a secure password strategy as part of daily administration. This approach aligns with industry-wide best practices for device security and credential governance.
Understanding default credentials variability in ZKTeco devices
There is no single credential that fits every ZKTeco product line. Different device families—ranging from standalone time-attendance terminals to door controllers—ship with model-specific defaults that may change between firmware revisions. The absence of a universal default means that administrators must rely on the official manuals, supplier documentation, and vendor support portals to identify the exact default username and password for each device. Always treat defaults as temporary—plan a reset flow that establishes a strong admin credential immediately after initial access. This practice reduces the risk of unauthorized configuration and ensures a clear audit trail.
In practice, credential changes should be documented, and any locally stored credentials should be treated as sensitive information. If you cannot locate the official guidance for a particular model, contact the vendor or authorized service partner rather than guessing defaults. The overarching principle is: verify, reset if needed, and then enforce a policy for credential management that includes regular reviews and timely firmware updates.
Safe reset procedures and admin credential establishment
When legitimate access is required and you cannot log in, follow a documented reset process that restores the device to a known-good state and prompts you to set a new admin credential. General safeguards include:
- Confirm ownership and authorization before performing resets.
- Use an isolated management workstation to carry out reset steps where possible.
- After reset, immediately configure a unique, strong admin password and enable account-lockout or auditing if available.
- Document the new credentials securely and restrict who can view them.
- Review connected services and remote access rules to minimize exposure during the credential transition.
Note that the exact steps vary by device model and firmware. Always rely on official manuals and vendor-supported procedures rather than informal guides. A well-executed reset combined with a robust password policy significantly lowers the risk of compromise.
Verifying credentials safely without exposing sensitive data
After performing a reset or credential update, validate access through a controlled test: sign in from a trusted workstation, confirm that only authorized accounts can access admin features, and verify that non-admin users cannot elevate privileges. Maintain logs of login attempts and monitor for unusual activity in the device management portal. If you encounter unexpected prompts or denied access, recheck the device’s network configuration and firmware version to ensure there are no service-side blocks or incompatibilities.
This careful verification helps ensure that the new credentials are functioning correctly and that the device is operating with proper security controls in place.
Common missteps and how to avoid them
Administrators often make a handful of avoidable errors when dealing with defaults:
- Assuming a universal default exists and attempting generic passwords.
- Sharing admin credentials across multiple devices without a scoped role model.
- Delaying credential changes after a reset, leaving doors or terminals exposed.
- Failing to document changes or to enforce password rotation policies.
Avoid these by embedding credential management into your standard operating procedures, training staff on secure handling, and scheduling periodic reviews of all device credentials. Regular firmware updates and security patches from ZKTeco further reduce the risk of exploitation through known defaults.
Security best practices for ZKTeco devices (liveable, repeatable guidance)
To sustain secure operations, adopt these practical practices:
- Change defaults immediately after initial access and disable unused services.
- Use unique, complex passwords and enable MFA where supported.
- Keep firmware up to date to mitigate known vulnerabilities.
- Segment device management networks and restrict remote administration.
- Maintain an auditable trail of credential changes, including timestamps and responsible administrators.
These steps are broadly recommended across access-control ecosystems and align with industry security standards for device hardening and credential governance.
What to do if you’re locked out or need support
If you are locked out after a reset or cannot locate model-specific default guidance, contact the device vendor’s official support channel or your authorized integrator. Do not attempt alternate reset methods that might violate warranty terms. When reaching out, provide device model, firmware version, and a concise description of the issue. Keeping a documented recovery process helps ensure a fast, compliant resolution and preserves the security integrity of the access control system.
Overview of default credential variability and reset availability across ZKTeco device families
| Model family | Default credential status | Reset process availability |
|---|---|---|
| Access control terminal | Model-dependent, varies by firmware | Factory reset documented per model |
| Time attendance reader | Defaults vary by device lineage | Vendor documentation required |
| IP-based door controller | No universal default | Model-specific reset path |
Your Questions Answered
Is there a universal default username for ZKTeco devices?
No. Default credentials vary by device model and firmware. Always consult the official manuals for model-specific defaults and never assume a universal credential across product lines.
There isn’t a universal default username for ZKTeco devices; check the specific model’s manual for the exact default.
How should I reset a ZKTeco device if I can’t log in?
Follow the vendor’s documented reset procedure for your model to restore access, then immediately set a new admin password and review security settings.
Use the official reset steps for your model, then create a strong admin password and review security settings.
Where can I find the official default credentials documentation for ZKTeco devices?
Official credential information is found in the device’s user manual and the vendor support portal. If needed, contact your vendor or authorized partner for the correct model-specific defaults.
Look in the official manual or vendor support portal for your model’s defaults, or ask your vendor.
What are best practices after changing defaults?
Immediately enforce a strong admin password, enable auditing, restrict admin access to trusted networks, and document the change for compliance records.
Use a strong password, restrict access, and document the change.
I’m locked out after a reset. What should I do?
Refer to the vendor’s recovery options, confirm ownership, and work with support to reestablish access without bypassing security controls.
If you’re locked out, contact support and follow official recovery steps.
Are there general credential-management best practices for devices like ZKTeco?
Yes—apply a policy of unique credentials per device, frequent rotations, minimal privilege for users, and regular firmware updates.
Use unique, rotating credentials and keep firmware up to date.
“Security starts with credential hygiene. Since there is no universal default, always reference the official manuals and implement a formal reset-and-change workflow.”
Key Takeaways
- Change defaults immediately after initial access
- Consult official manuals for model-specific guidance
- Establish strong, unique admin passwords after resets
- Document credential changes and enforce rotation
- Keep firmware updated to reduce vulnerability surface