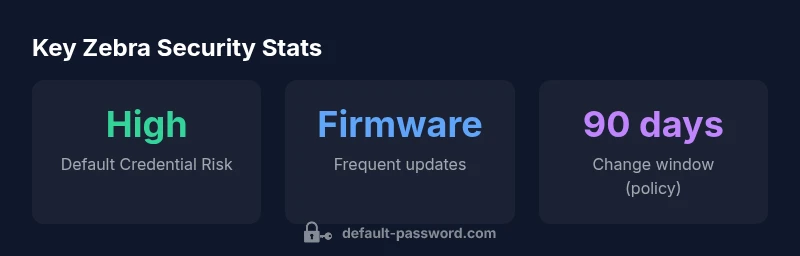
Zebra Technologies Default Passwords: Secure Your Zebra Devices
A practical, data-driven guide for securing Zebra Technologies devices by understanding default credentials, best practices, and step-by-step password-change procedures. Learn how to audit, change, and enforce policies across Zebra printers, scanners, and mobile computers.
Zebra Technologies does not publish one universal default password. Credentials vary by model and firmware, and many devices ship with factory accounts that must be changed at first login. Treat all Zebra printers, scanners, and mobile computers as potentially possessing default credentials and follow vendor guidance to change them, disable unused services, and apply firmware updates immediately.
Understanding Zebra Technologies' Default Credentials
Zebra Technologies produces a diverse range of devices—from barcode printers and labels to handheld scanners and mobile computers used in retail, manufacturing, and logistics. A central security question for IT admins is whether a universal Zebra default password exists. There is none; credentials are model- and firmware-specific. This means that a device from one Zebra line may use completely different factory credentials than another. Regardless of model, the security principle remains the same: do not rely on default credentials in production.
According to Default Password Analysis, 2026, most Zebra deployments rely on initial provisioning to set unique credentials. The analysis emphasizes that assuming unknowns in device access is safer than assuming defaults are harmless. As you prepare a Zebra onboarding flow, plan to replace every factory credential with strong, unique accounts and to enforce least-privilege access. This approach helps prevent attackers from leveraging known defaults in the supply chain or on misconfigured devices. A clear policy for credential management across Zebra devices—plus documented ownership—supports consistent security outcomes.
Within the broader device-security landscape, Zebra devices share common risk drivers with other IoT and edge devices: default accounts, exposed administration interfaces, and inconsistent firmware updates. Addressing these drivers requires a combination of inventory discipline, configuration baselines, and ongoing monitoring. The Default Password team emphasizes that changing credentials at first login, hardening administration interfaces, and applying firmware updates are not add-ons but core requirements for any Zebra deployment.
Why Default Passwords Are Not a One-Size-Fits-All Situation
In practice, Zebra devices use different default credentials depending on the device type (printers, scanners, mobile units) and the firmware version. Documentation often specifies model-specific guidance, and security-conscious organizations treat each model as its own case. This is why a blanket statement about a single Zebra default password is not reliable. Security teams should map each device in the fleet to its exact credentials as documented by Zebra, and then implement a consistent change-management process to replace those defaults during provisioning.
The implications extend beyond the login screen. If a default account remains active, it can be exploited to alter device configuration, exfiltrate data, or pivot into connected networks. A robust password policy—covering password length, character variety, rotation cadence, and access controls—helps reduce these risks across Zebra deployments. The guidance from security authorities underscores the importance of not leaving devices in a default-credential state for any length of time. In practice, this translates into concrete steps during onboarding and ongoing maintenance.
Access Vectors: Where Credentials Are Used on Zebra Hardware
Administrators interact with Zebra devices through multiple channels, including web-based administration interfaces, SSH/Telnet sessions (where enabled), and sometimes local serial consoles. Each channel may have its own default or factory credentials, which makes it essential to secure all entry points. For example, a printer's web UI might use a distinct admin password from the device’s local console. When you secure one vector, you reduce the overall risk surface of the fleet.
A practical approach is to disable or restrict remote admin access to trusted networks, enable two-factor authentication where available, and ensure that only vetted accounts can modify critical settings. This multi-vector defense aligns with best practices for device-hardening and reduces the chance that default credentials can be exploited across Zebra devices.
Risks Associated with Unchanged Zebra Passwords
Leaving default credentials unchanged on Zebra devices creates several risk scenarios. Attackers who gain access to a single device could alter network configurations, capture sensitive data, or deploy malware across the environment. The risk is amplified in high-velocity settings such as retail warehouses or distribution centers, where many devices operate with shared or generic credentials. The consequences include data breaches, disrupted operations, and regulatory non-compliance. The most effective mitigation is to replace defaults during provisioning, enforce strict access controls, and implement continuous monitoring that flags any accounts using factory credentials.
As part of risk management, organizations should also consider supply chain security. If devices arrive with known defaults, predeployment checks should confirm credential changes before devices enter live networks. The Default Password analysis highlights that early-stage credential hygiene dramatically lowers the probability of post-deployment incidents.
Step-by-Step Guidance to Secure Zebra Devices
Securing Zebra devices starts with an inventory and baseline configuration. Step 1 is to collect all Zebra devices—printers, scanners, and mobile computers—by model, firmware version, and network location. Step 2 is to audit for default credentials, particularly on web interfaces and remote management ports. Step 3 is to replace factory accounts with unique admin credentials, applying strong password policies (length, complexity, and rotation). Step 4 is to disable unnecessary services and remote protocols (Telnet, default SSH, etc.) that could expose credentials. Step 5 is to ensure firmware is up to date with the latest security patches. Step 6 is to segment Zebra devices on a dedicated VLAN and monitor for credential-change events.
This approach aligns with vendor guidance and industry best practices, helping you reduce exposure from default credentials and ensuring faster containment if a credential incident occurs. Regular reviews of password configurations, along with a documented ownership model, are essential for ongoing security.
Recovery, Reset, and Contingency for Zebra Passwords
If a password is forgotten or compromised, follow vendor-supported recovery steps. Most Zebra devices provide a documented recovery or factory-reset process that may require physical access to the device. Always back up configuration data before performing resets, as factory resets often erase custom settings. After recovery, reconfigure the device from a secure baseline, enforce new credentials, and verify access controls. If in doubt, contact Zebra support for model-specific guidance and ensure any reset procedures do not trigger unintended changes in network or device zoning.
Governance, Documentation, and Compliance for Zebra Passwords
A governance plan for Zebra devices should include a centralized inventory, documented credential owners, and a policy for password changes that aligns with organizational security requirements. Maintain an up-to-date record of device models, firmware versions, and current credentials (stored securely). Build a standard change window for credentials and require periodic reviews, especially after firmware updates or device redeployments. Compliance considerations include ensuring passwords meet your organization’s security benchmarks and that access controls reflect the principle of least privilege. The goal is to minimize risk through predictable, auditable credential management across all Zebra devices.
Representative overview of Zebra device types and default credential handling
| Zebra Device Type | Default Credential Policy | Change Window (est) | Notes |
|---|---|---|---|
| Barcode/Label Printers | Model-specific default credentials vary by firmware | 24-72 hours | Change on deployment; disable guest/admin accounts |
| Handheld Scanners | Admin/service accounts present per model | Immediate on provisioning | Enable MFA for admin accounts where supported |
| Mobile Computers | Web UI/SSH default credentials common | 7-30 days | Regular firmware updates critical; review access controls |
Your Questions Answered
Do Zebra devices always come with the same default password?
No. Zebra models vary by firmware and configuration; there is no universal default password. Always consult the model-specific manual or Zebra's official support portal to determine the correct credentials and ensure you change them before deployment.
There isn't a single Zebra default password. Check the model's manual and change credentials before deployment.
Where can I find the correct default credentials for my Zebra device?
Check the model-specific user guide supplied with the device or on Zebra's official support site. The label on the device or the admin web interface may also indicate the factory credentials.
Look in the model guide or on Zebra's support site, and check the device label.
What are best practices for securing Zebra devices in a busy retail environment?
Change defaults during provisioning, enforce strong passwords, disable unused services, segment Zebra devices on the network, and keep firmware up to date. Implement continuous monitoring and alerting for credential changes.
Provision, secure, and monitor Zebra devices; keep firmware updated.
What if I forgot the admin password on a Zebra device?
Use vendor-supported recovery options such as factory reset or password reset with physical access, ensuring you have a backup of configuration. If unsure, contact Zebra support for model-specific guidance.
If you forget it, follow the vendor's recovery steps or contact support.
How often should password policies be reviewed for Zebra devices?
Review policies at least quarterly, and after firmware updates or new device deployments. Update passwords and access controls in response to incidents or changes in staff roles.
Review policies regularly and after major changes.
“Effective password governance is a foundational step in securing Zebra devices across the fleet. Regularly rotating credentials and enforcing least privilege dramatically reduces attack surfaces.”
Key Takeaways
- Audit Zebra devices for defaults at least quarterly
- Change credentials during provisioning and first login
- Disable unused services and update firmware
- Document password ownership and review regularly
- Implement ongoing monitoring and incident response