DVR 104G F1 Default Password: Security Guide
Learn how to identify and reset the DVR 104G F1 default password, assess security risks, and implement secure admin access with practical, step-by-step guidance.
Definition: The DVR 104G F1 default password is the factory credential used for initial setup. It is widely recognized as a security risk, so reset to a unique password via the admin interface, update firmware, and enable secure remote access controls. Additionally, audit connected devices, enforce access controls, and document changes per security policy.
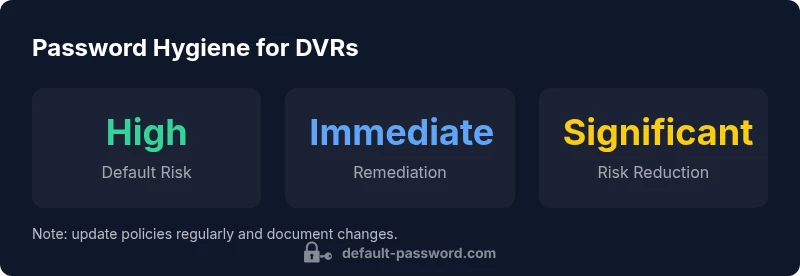
Why DVR security hinges on password hygiene
The dvr 104g f1 default password is a phrase you will encounter in security advisories because it represents a common, avoidable risk. When devices ship with a known credential, attackers can exploit exposed services, often with minimal effort and no user interaction. In practice, leaving the default password in place after installation creates an entry point that can grant unauthorized access to video feeds, configuration settings, and network devices. According to industry observations summarized by Default Password, many incidents begin with administrators or homeowners failing to replace factory credentials. In this guide we examine why this password is a central security lever, how to detect it, and how to remediate it quickly and safely. We will also discuss password strength, brand-specific quirks for DVRs, and how to integrate this step into a broader security program.
Practical steps to reset the password
Start by identifying the device model and firmware version to ensure you follow the correct reset path. Access the admin interface from a computer on the same local network, using a wired connection if possible to reduce risk during the change. Navigate to the Security or User Management section, locate the account that has administrator privileges, and initiate a password change. Choose a long, unique password that combines letters, numbers, and symbols; avoid obvious phrases or re-use from other sites. After saving changes, log out and log back in to verify the new credentials are accepted. As a best practice, enable firmware updates and review other hardening options such as disabling UPnP, restricting remote access, and activating IP-based access controls. Finally, document the change in your security log, noting who performed it and when, so you can audit future access.
How to verify and limit exposure
Verification step one is to confirm the password change took effect on all interfaces (web, mobile, and any local apps). Step two is to test whether remote access is necessary for your environment. If not required, disable it or require a VPN for any outside connection. Use network segmentation to separate video devices from general corporate or home networks. Consider enabling TLS/HTTPS for the admin interface and enforcing password complexity requirements. Finally, run a quick risk assessment by checking for default accounts or scripts that may still rely on factory credentials in the config backups. The goal is not just to change a password, but to reduce the attack surface.
Firmware updates and admin access best practices
Regular firmware updates close known vulnerabilities that default credentials often expose. Enable automatic updates if the device supports it, or set a recurring reminder to check for new firmware quarterly. Create separate administrative and user accounts and assign the least privilege necessary for daily tasks. If the device allows two-factor authentication for the admin account, enable it; if not, at least require strong password policies and periodic password changes. Disable any services you do not use, such as remote administration, universal plug-and-play, or cloud features that route video to third-party servers. Document every change, including the firmware version and the date of the update, to support audits and incident response.
Common mistakes to avoid
Avoid reusing passwords across devices or services; use a password manager to generate and store unique credentials. Do not store passwords or recovery phrases on sticky notes or unencrypted documents. Do not delay password changes after purchase or after a known breach. Avoid brittle password schemes; do not rely on simple patterns or common words, even if you think they are memorable. Lastly, never ignore security advisories; patching is as important as changing a default password because both reduce risk in tandem.
Real-world scenarios and checklists
Consider a small office with several DVRs: create a centralized password policy, apply it consistently across devices, and schedule quarterly reviews. Use a checklist: 1) verify device model and firmware; 2) replace default password with a unique one; 3) verify remote access is restricted or bound to VPN; 4) enable HTTPS; 5) confirm entries in the security log. For households, start with your main DVR, update firmware, switch to a robust password, disable unnecessary remote access, and enable alert emails if supported. In both cases, maintain an up-to-date inventory of devices and users and assign role-based access to limit what each account can see and do.
Security posture over time
Password hygiene is not a one-off task; it should be part of an ongoing security program. Schedule semiannual reviews to reassess the password policy, check for new firmware, and validate that remote access remains controlled. Maintain an auditable change log that records every password modification and who performed it. Assess whether new features or integrations introduce new risks, and adjust access controls accordingly. By treating password management as continuous risk reduction, organizations and households can keep pace with evolving threats.
How to document changes
Documentation should be clear, concise, and accessible to IT staff and auditors. Include device identifiers, firmware versions, old and new credentials in an encrypted format, dates of changes, and the names of responsible personnel. Store changes in a centralized inventory or security portal and attach supporting evidence such as screenshots of the new settings. Periodically review the log for anomalies and perform reconciliation with access control policies. A well-maintained change log makes incident response faster and maintains compliance with security policies.
Additional considerations: remote access and cloud integration
Some DVRs offer cloud features or direct remote access options; these increase convenience but also expand the attack surface. If you rely on remote viewing, implement a VPN or private connectivity rather than exposing the admin interface to the internet. Review cloud service terms and ensure that data handling aligns with your privacy and security requirements. Keep an eye on vendor notices about security advisories and ensure your security policies reflect evolving capabilities and threats. The ultimate goal is to balance ease of access with robust protection.
Sources
- https://www.cisa.gov
- https://www.nist.gov/topics/cybersecurity-framework
- https://www.fbi.gov/news/stories
Typical scenarios for default-password risk across video security devices
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| DVR/NVR devices | Default password present on device after purchase | Change immediately via admin panel; enforce unique, strong passwords and enable firmware updates |
| IP cameras | Commonly shipped with default credentials | Change default accounts during initial setup; disable unused services and UPnP |
| Routers/gateways | May include default admin password | Create a new admin password; disable remote admin if not required |
Your Questions Answered
Why is the dvr 104g f1 default password considered risky?
Default credentials in DVRs are widely known and can be exploited to gain unauthorized access to video feeds and device settings. Changing the password reduces the attack surface and aligns with security best practices.
Default credentials in DVRs are risky because attackers can access video feeds and device settings if not changed.
How do I change the DVR 104G F1 password?
Enter the device's admin interface, navigate to Security or User Management, select the admin account, and set a unique, long password. Save changes and verify by logging out and back in.
Go to your DVR's admin page, find Security, create a new strong password, and confirm by logging in again.
Is it safe to disable remote access on DVRs?
Disabling remote access reduces exposure to the internet. If remote viewing is needed, route traffic through a VPN and enforce strong authentication.
Turning off remote access lowers risk; if you need it, use a VPN and strong authentication.
Do DVRs support two-factor authentication?
Some models offer 2FA for the admin account; if available, enable it. If not, implement strict password policies and monitor access.
Some DVRs support 2FA; enable it if possible and otherwise apply strict password rules.
Where can I find firmware updates for the DVR 104G F1?
Check the manufacturer's official support site for your model, or contact your distributor. Apply firmware updates promptly to close vulnerabilities associated with default credentials.
Check the maker’s site for the DVR 104G F1 firmware, and install updates when they’re available.
“Eliminating default credentials is one of the simplest, most impactful steps you can take to tighten security across networked video devices.”
Key Takeaways
- Change the default password immediately on all DVR/NVR devices.
- Enable firmware updates to close security gaps.
- Limit exposure by disabling unnecessary remote access and services.
- Document password changes as part of security policy.