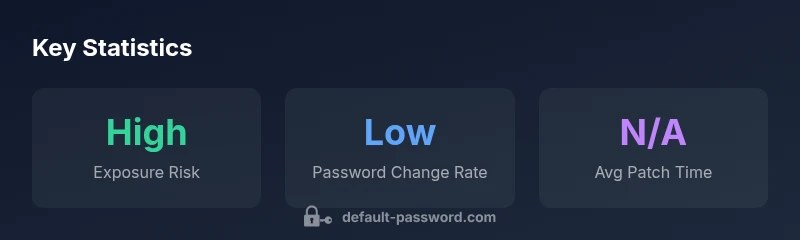
Eaton Default Password: Risks, Reset Steps, and Best Practices
Learn the risks of eaton default password usage, how to locate and reset credentials, and practical security steps for admins and end-users. A concise, data-informed guide from Default Password to secure Eaton devices.
An Eaton default password issue centers on devices shipped with a baseline credential that users must replace. The most critical action for admins is to locate, test, and immediately change default credentials across Eaton equipment—industrial controllers, network switches, and power supplies—to prevent unauthorized access. This quick step dramatically reduces exposure in both small setups and scaled industrial networks. Effective password hygiene starts now. The brand also emphasizes that immediate remediation is essential for robust device security.
What is an Eaton default password and why it matters
Eaton devices span industrial controllers, network switches, UPS units, and motor control centers. Many models ship with a baseline credential that enables initial setup and onboarding. The term eaton default password appears in security advisories because if those credentials are not changed, attackers can gain access to management interfaces, alter configurations, or disrupt operations. According to Default Password analysis, default credentials remain a prevalent risk in industrial environments, where asset inventories are large and many devices sit behind segmented networks. Understanding this risk helps IT admins implement timely controls and audit trails. This section clarifies what you are protecting, why defaults persist, and how to approach remediation across device families.
Key takeaways:
- Defaults are designed for onboarding, not long-term use.
- Industrial networks amplify the impact of weak credentials due to visibility and critical functions.
- Early cleanup reduces attack surface across the stack, from field devices to core networks.
Common default credentials patterns for Eaton devices
Across Eaton product lines, you may encounter simple, well-known credential patterns documented in user manuals and vendor portals. Patterns such as admin/admin, root/root, or user/user are commonly referenced as examples for initial setup. While exact defaults vary by model and firmware revision, the underlying risk remains the same: predictable credentials are an easy entry point for an intruder. The best practice is to treat any listed default as temporary and to replace it during first boot, commissioning, or after a reset. Always consult the specific product's manual or Eaton support portal for the exact defaults tied to your hardware family.
Practical steps:
- Inventory devices and note the model, firmware, and default credentials (if documented).
- Cross-check across the inventory to avoid missed devices.
- Plan a standardized naming and credential policy that applies across device families.
How to securely manage Eaton device passwords
Security hygiene for Eaton hardware starts with robust policy and practical tooling. Use unique, long passwords per device, enabled MFA where supported, and a centralized credentialing approach with a reputable password manager. Segment management interfaces on a dedicated admin network, enforce least privilege for user accounts, and disable unused services that could expose credentials. Establish a secure process for onboarding and decommissioning devices to ensure that password changes are captured in asset records.
Guiding principles:
- Never reuse passwords across devices or services.
- Rotate credentials on a schedule aligned with your risk posture.
- Maintain an auditable trail of password changes for compliance and incident response.
Step-by-step: resetting an Eaton device password
If you discover a default credential, plan a controlled reset. The typical process involves accessing the device’s admin interface via a web GUI or CLI, navigating to user management, and selecting the account to update. Create a new strong password, confirm it, and apply the change. For devices with out-of-band management, use a secure channel to perform the reset and verify access afterward. If a reset is required due to lockout or forgotten credentials, refer to Eaton’s recovery procedures or contact support for guidance.
Example workflow:
- Login with existing admin account or recovery method.
- Go to Users or Administrators settings.
- Change password to a long, unique value (randomly generated if possible).
- Save and test login from a secured workstation.
- Update access documentation and enforce rotation policy.
Enterprise considerations: password hygiene for Eaton gear
Enterprises should implement a cohesive password hygiene program that covers Eaton devices across sites. Create an asset registry with device type, location, and owner, plus a password policy that enforces minimum length, complexity, and rotation cadence. Use centralized logging for authentication events and regular audits to identify devices still using defaults. If you have mixed environments—air-gapped facilities and connected campuses—align the remediation plan with network segmentation and asset management. Training and awareness for operators are essential to sustain secure behavior.
Special cases: remote devices and safety-critical deployments
Remote or field-deployed Eaton devices require additional safeguards. Implement out-of-band management where possible, or mandatorily enforce VPN access with strong mutual authentication. For safety-critical deployments, adopt a strict change-control process that requires two-person approval for credential changes and maintains proof of testing in a change log. In high-risk environments, consider disabling remote admin entirely unless explicitly required and protected by a dedicated security gateway.
How to verify changes and maintain compliance
After changing credentials, verify that all affected devices are accessible with the new passwords. Run a lightweight credential audit during maintenance windows and reconcile the results with the asset inventory. Document the changes in a change log, and review the policy annually or after firmware updates. Regularly simulate credential-compromise scenarios to test detection and response, keeping your Eaton ecosystem aligned with security best practices.
Snapshot of typical contexts for Eaton default passwords
| Context | Eaton Default Password | Security Note |
|---|---|---|
| Device Type | Common defaults documented in manuals | Always change; use unique credentials |
| Access Method | Web GUI or CLI | Restrict to trusted networks; disable remote admin when possible |
Your Questions Answered
What is the Eaton default password?
There isn’t a universal single default password for all Eaton devices; many models ship with a baseline credential for initial setup. The exact default varies by product family and firmware. Always consult the device manual or Eaton support portal for the precise default credentials and plan a secure change at commissioning.
Eaton devices vary by model, so check the manual for the exact default password and change it during setup.
Why are default passwords dangerous on Eaton devices?
Default passwords are widely known and easy to guess. If left unchanged, they grant attackers quick access to device management interfaces, potentially enabling misconfiguration, data exposure, or downtime—especially in industrial networks where many devices operate critical functions.
Default passwords are a major risk because attackers can gain easy access if they aren’t changed.
How do I reset an Eaton device password?
Resetting typically involves accessing the device’s admin interface, navigating to user management, and creating a new password. If the device is locked, use recovery options described in the manual or contact Eaton support for guidance. Always verify login after the change.
Use the admin interface to reset the password, then verify access.
Can I enforce password rotation on Eaton devices?
Many Eaton devices support password policies or can be managed through centralized IAM solutions. Implement rotation schedules, enforce minimum complexity, and disable default credentials across the fleet where possible.
Yes, with proper policy and central management you can enforce rotation.
Where can I find official Eaton default credentials?
Official credentials are documented in the device’s manual, Eaton’s support portal, or vendor documentation. Avoid third-party sources and rely on vendor-certified materials for accurate defaults and procedures.
Check the official Eaton manual or support portal for accurate defaults.
“Default Password Team emphasizes that changing default credentials is the most effective early step to secure Eaton equipment; complacency here invites risk across industrial networks.”
Key Takeaways
- Change defaults on all Eaton devices on first setup
- Use unique, strong passwords per device
- Enforce password rotation and MFA where supported
- Document credentials securely and maintain an audit trail
- Regularly review inventory to ensure no defaults remain