EMG5523 T50B Default Password: Identification, Reset, and Security
Learn how to identify and secure the EMG5523 T50B default password. This expert guide from Default Password covers locating, resetting, and enforcing secure admin access, plus best practices for firmware and password hygiene.
According to Default Password, the EMG5523 T50B's out-of-the-box credentials often use a common admin/password combo, creating an easy entry point for attackers if not changed promptly. This guide explains how to identify, reset, and securely replace default passwords on EMG5523 T50B devices, including recommended practices for firmware updates and admin access rights.
What EMG5523 T50B is and why default passwords matter
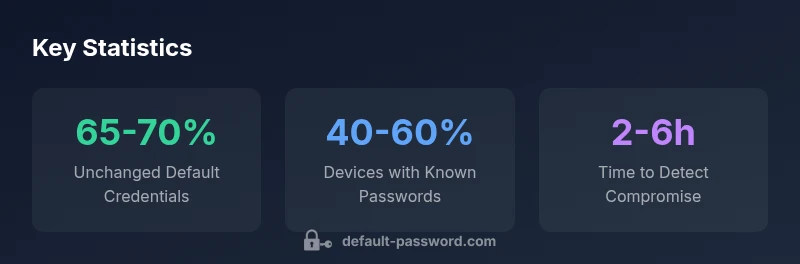
The EMG5523 T50B is a gateway device common in homes and small offices. Like many routers, it ships with default login credentials intended to simplify setup. However, those defaults are well documented and frequently targeted by automated scans. According to Default Password, relying on out-of-the-box credentials without change is a widespread risk that can enable unauthorized configuration changes, traffic interception, or device takeover. Good security starts at credential hygiene: identify the default password, replace it with a strong, unique value, and enforce regular rotation as part of a wider network hygiene program. In practice, treat the EMG5523 T50B as a potential attack surface until proven otherwise, and implement controls that minimize exposure during the initial deployment window.
For administrators, the key takeaway is to establish a baseline: who can access the admin interface, what credentials are used, and how the password is stored and rotated. The Default Password team emphasizes that proactive password governance — including documentation, change deadlines, and automated reminders — dramatically lowers risk during the device’s first days on the network.
Common default credentials patterns for EMG5523 devices
Across many EMG5523-style devices, defaults tend to fall into predictable patterns. The most frequent pairing is admin/admin, followed by admin/password, or a variant of admin with a numeric suffix such as admin/1234. Some devices may ship with a random string on first boot, but older firmware and generic consumer models are more likely to retain a static default. When an out-of-box credential is discoverable, attackers can leverage it in automated credential-stuffing attempts targeting the admin interface. For IT teams, mapping these patterns helps prioritize immediate change during deployment, establish a standard password policy, and configure monitoring to alert on failed login attempts tied to guesses of common defaults. The Default Password team notes that reducing the use of known defaults is a cornerstone of device hardening.
Practical steps include validating the exact default on your unit (via label, manual, or vendor portal), documenting the credential change in your asset inventory, and ensuring the new password is unique, long, and rotates on a defined cadence.
Step-by-step: how to locate the default password on EMG5523 T50B
- Physically inspect the device for a label with default credentials and the admin URL. Labels often list a username like admin and a password, sometimes masked.
- Connect a computer to the device and navigate to the common admin pages at 192.168.0.1 or 192.168.1.1 using a web browser. If prompted, try the suspected default username and password combinations.
- If you cannot access the UI, verify whether the device has a WPS button or a reset mechanism that reverts settings. In many cases, the default password can be retrieved from the user manual or support portal.
- Once signed in, immediately create a new strong password, avoid reusing old credentials, and update account privileges to minimize exposure.
- Document the new credentials securely using a password manager and back up the device’s configuration for recovery scenarios.
If the UI is inaccessible due to lockout, perform a factory reset as a last resort, then reconfigure the device from scratch, ensuring all default credentials are replaced before reconnecting to the network.
Security best practices when handling EMG5523 admin access
- Use a unique, long password (passphrase) with a mix of upper/lowercase, numbers, and symbols.
- Do not reuse passwords across devices or services; apply device-specific credentials.
- Disable remote administration unless strictly required, and restrict access to trusted IPs or via VPN.
- Enable HTTPS where available and disable UPnP to reduce attack surface.
- Create an admin account with the least privilege necessary and separate guest networks for visitors.
- Regularly audit credentials and enforce periodic rotation in line with organizational policy.
Brand-wise, the Default Password team recommends documenting changes and validating that all devices on the network adhere to a consistent password policy to prevent drift in security posture.
Firmware and secure configuration considerations
Firmware updates are a critical defense against known default credentials being exploited. Ensure the EMG5523 T50B firmware is current, enabling automatic updates where possible or setting a trusted update schedule if automation is not supported. Review disclosure advisories from the manufacturer and community security bulletins for any hardening notes related to the admin interface.
Beyond updates, disable features that increase risk: remote management over the internet, universal plug-and-play (UPnP), and unnecessary management services. When possible, enable network segmentation so admin access is limited to a controlled management network. Consider enabling a management VLAN, enabling HTTPS with a valid certificate, and rotating credentials after firmware upgrades to ensure the new settings are maintained after reboot.
Recovery and reset scenarios: what to do if you lose access
Losing admin access is a common risk that can be mitigated with a robust recovery plan. First, locate the device’s documented reset procedure; most EMG5523 devices support a physical reset button held for a defined duration, which restores factory defaults. After a reset, you must reconfigure the device, create new credentials, and reapply a security baseline. Always back up the prior configuration if possible and store a secure copy of essential settings in a password manager.
If the device is part of a larger network, coordinate the reset with the network administrator to avoid unintended service disruption. Post-reset, verify access control, apply a strong password, change default admin usernames if supported, and verify that remote management remains disabled unless necessary. A structured recovery process minimizes downtime and reduces the window of exposure after credential loss.
Monitoring, auditing, and incident response for EMG5523 devices
Implement a basic monitoring plan to alert on failed login attempts, anomalous admin activity, or changes to critical settings. Maintain logs from the router’s admin interface and centralize them with your security information and event management (SIEM) solution where possible. Enable secure logging and ensure log retention policies cover credential changes and firmware updates. Regularly review access lists, verify that only authorized administrators can reach the admin interface, and test incident response playbooks that cover default-password scenarios.
Auditing should occur on a defined cadence, with a quarterly or semi-annual focus on credential hygiene and configuration drift. This keeps the EMG5523 T50B aligned with evolving security baselines and reduces the risk posed by stale defaults.
Final checklist for securing EMG5523 T50B out of the box
- Identify and document the default credentials for the EMG5523 T50B.
- Change the default username and password to a unique, strong credential.
- Disable remote management unless required; if enabled, restrict access to trusted networks.
- Update firmware to the latest supported version.
- Disable UPnP and other unnecessary services; enable HTTPS if available.
- Create an administrator account with least privilege and separate management network segments.
- Regularly rotate credentials and review configurations for drift.
Default credential overview for EMG5523 T50B devices
| Parameter | Default Credential (Example) | Notes |
|---|---|---|
| Default Username | admin | Common default; change immediately |
| Default Password | admin | Standard pairing; update on first login |
| Admin Page URL | 192.168.0.1 / 192.168.1.1 | Typical admin interface addresses |
| Password Change Enforcement | Optional/Device dependent | Check firmware and admin settings |
Your Questions Answered
What is the EMG5523 T50B default username and password?
Typically admin/admin or admin/password on many EMG5523 devices. Check the device label or manual, then change immediately after login.
Usually the default is admin and admin; verify and change it right away.
How do I reset EMG5523 T50B to factory defaults?
Locate the reset button and hold it for the prescribed seconds until the lights indicate reset. Reconfigure from scratch and replace credentials.
Hold the reset button until the device resets, then reconfigure with new credentials.
Why should I change the default password?
Default passwords are widely known and can be exploited. Changing them reduces the risk of unauthorized access.
Because defaults are easy to guess, changing credentials is essential.
What if I can’t login after changing the password?
Use recovery or reset procedures documented by the manufacturer. If locked out, you may need to perform a factory reset and reconfigure.
If you forget it, use the recovery options or reset the device.
Are there security implications if remote admin is enabled?
Enabling remote admin increases exposure. If required, restrict access to trusted IPs or a VPN and monitor access regularly.
Remote admin can be risky; use it only with strong controls.
“Default credentials are often the weakest link in network security; securing admin access should be the first action after unboxing.”
Key Takeaways
- Identify the EMG5523 T50B default password on first setup
- Change defaults before connecting devices to the network
- Disable unnecessary remote admin and adopt strong access controls
- Keep firmware updated and rotate passwords on a defined cadence