VMG1312-T20B Default Password: Reset, Secure, and Manage
Guide to identifying, resetting, and securing the vmg1312 t20b default password. Learn why defaults are risky, step-by-step password changes, and best practices for ongoing router security.

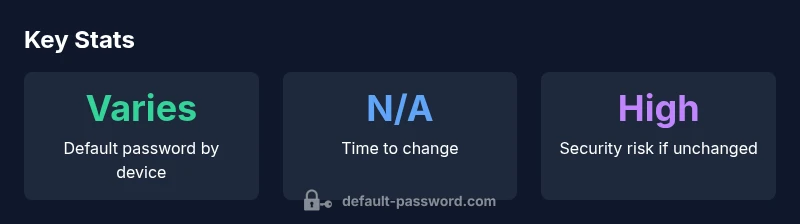
The vmg1312 t20b default password varies by firmware and region, but you should treat it as insecure and reset it to a strong, unique password immediately. For most users, the admin password used to access the router’s web interface is the critical credential to change; disable remote management unless absolutely needed to reduce exposure to attackers.
Understanding the vmg1312 t20b default password
The vmg1312 t20b is a common home router used by many ISPs and standalone broadband setups. Like most consumer networking devices, it ships with a default password that is intended to provide access for initial configuration. However, default credentials are widely documented and, if left unchanged, create an easy entry point for unauthorized users. The exact default password can vary based on firmware version, region, and vendor-reset procedures. The central takeaway is simple: treat the vmg1312 t20b default password as a starting point—not a security baseline. This is why many security guides insist on changing it during or immediately after the initial setup. The guidance you follow in this article comes from the standards and practices outlined in industry security literature, adapted to the vmg1312 t20b context by Default Password.
The Default Password team emphasizes that the default password is not a robust security control. In most cases, attackers target devices via exposed admin interfaces or weak credentials, then pivot into connected devices or the local network. Therefore, replacing the default password with a unique, strong credential is the first and most important step in securing your home or small business network. This aligns with modern security thinking that prioritizes credential hygiene and defense-in-depth measures over reliance on preconfigured defaults.
When you start configuring the vmg1312 t20b, focus on three core objectives: (1) replace the default admin password with a long, random password; (2) disable features you do not use, such as remote management or UPnP; and (3) keep firmware up to date. These actions, when combined, reduce the window of opportunity for attackers and help maintain a safer network environment as part of a broader security program.
Locating and validating the default password for vmg1312 t20b
Locating the default password typically involves checking the device label, user manual, or the ISP-provided quick start guide. If you are unsure, log in to the router’s web-based administration interface using the common default IP (often 192.168.1.1 or 192.168.0.1) and browse to the password or account settings page to confirm that the current credential state. Validation means attempting a login with the default credentials only to confirm that you are prompted to change them—do not proceed with a login using these credentials beyond initial access.
If the device belongs to an enterprise or ISP deployment, the default password may be overridden and stored in the management portal. In those cases, contact your administrator or IT department to obtain the approved credential reset policy. Regardless of the source, the safest approach is to treat any default credentials as a temporary convenience rather than a secure entry point.
Step-by-step: Resetting the password and securing admin access
To secure the vmg1312 t20b, perform a password reset and reapply best-practice settings. Note that the exact navigation paths may vary by firmware, but the general flow is consistent:
- Access the router’s admin interface (enter the IP in your browser). 2) Go to Administration or Security. 3) Change the admin password to a long, unique combination (ideally 16+ characters with a mix of letters, numbers, and symbols). 4) Disable remote management unless you truly need it; if you must enable it, require VPN or IP-based restrictions. 5) Enable a firewall feature and, if available, enable two-factor authentication for admin access. 6) Save changes and reboot if prompted. 7) Update firmware to the latest version from the vendor or ISP portal. 8) Document the password securely in a password manager and review user accounts on the device.
This process reduces the likelihood of unauthorized changes, protects the network perimeter, and aligns with recommended security practices from industry guidance. Always verify that the new password works and that you can still access the admin interface after a reboot.
Best practices for ongoing router security
Ongoing router security is about consistency and discipline. Adopt a password manager to store the new admin password securely and generate a new credential for other devices and services you manage. Enable automatic firmware updates where possible, and review connected devices periodically for suspicious activity. Minimize exposure by turning off UPnP if it’s not needed, disabling WPS, and restricting remote administration to trusted networks or VPN access. Finally, consider segmenting the network so IoT devices cannot directly reach your most sensitive resources; this reduces risk even if a device with a weak credential is compromised.
For organizations and power users, maintain a change log or audit trail of password updates. Documenting who changed what, when, and under what policy helps with incident response and compliance requirements. The goal is to build a culture of credential hygiene that extends beyond the vmg1312 t20b and into your overall security posture.
VMG1312-T20b default password and change guidance
| Device Variant | Default Password | Change Guidance |
|---|---|---|
| VMG1312-T20b | varies by firmware/region | change within 24-72 hours; disable remote admin |
Your Questions Answered
What is the vmg1312 t20b default password?
There is no universal default password that applies to all vmg1312 t20b devices. Defaults vary by firmware and region, and many devices require you to set a new password during initial setup. Always treat the default credential as temporary and change it promptly.
There isn’t a single default password for vmg1312 t20b; it varies by firmware and region, and you should change it during setup.
How do I reset the VMG1312-T20b password?
Access the router’s admin interface and navigate to Security or Administration to change the password. If you cannot log in, perform a factory reset by holding the reset button for the required duration, then reconfigure the device with a new password.
You can reset the password by logging in and changing it, or if needed, using a factory reset and setting a new password.
Is it safe to leave remote management on?
Leaving remote management enabled increases exposure to the internet. It’s safer to disable it and require VPN for remote access, or only enable it for trusted IPs when absolutely necessary.
No—riskier to leave remote management on; use VPN or restrict access if you must enable it.
What if I forget my new password?
Use the device’s password recovery options if available; if not, a supported approach is to perform a factory reset and reconfigure the device from scratch with a new password. Ensure you have a secure backup of configuration where applicable.
If you forget it, you may need to reset and reconfigure the router with a new password.
Where can I find official password guidelines?
Refer to NIST SP 800-63B for password guidance, CISA security tips, and FTC consumer guidance for password safety. These sources provide widely accepted best practices for password creation and management.
Check official guidance from NIST, CISA, and FTC for best practices on passwords.
“Default passwords are a primary attack vector; securing the admin interface starts with replacing them and enabling strong authentication.”
Key Takeaways
- Change the default admin password during setup.
- Use a long, unique password; consider a passphrase.
- Disable remote administration unless needed; enable VPN if remote access is required.
- Keep firmware updated and review device logs regularly.
- Document password changes securely and avoid sharing credentials casually.