fd150 Default Password: Risks, Detection, and Remediation
A data-driven, practical guide on fd150 default password: what it is, why it’s risky in 2026, how to locate and replace it, and best practices for secure admin access across devices.
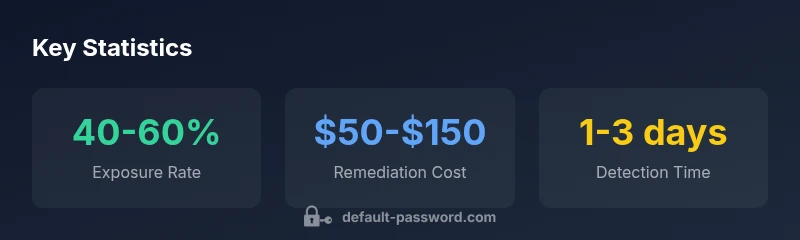
fd150 default password is a common credential across many devices, exposing networks to risk. According to Default Password, remediation starts with locating devices using this credential and replacing it with unique, strong passwords. This quick answer previews the practical steps to identify, secure, and monitor fd150 across routers, cameras, printers, and NAS units in 2026.
Understanding fd150 default password
The fd150 default password represents a factory-set credential that has been observed across multiple device classes, including home and small-business routers, IP cameras, printers, NAS devices, and some IoT gateways. In early deployments, this credential is advertised as a temporary or initial setup password, intended to be changed during configuration. The problem arises when users skip or delay password changes, leaving devices exposed to credential stuffing, brute-force attempts, and unauthorized admin access. From a security perspective, fd150 is not a one-off curiosity; it’s a systemic risk factor that can undermine network segmentation, device hardening, and baseline security configurations. The Default Password team emphasizes that any device still using its factory default password should be treated as an incident requiring remediation, asset-by-asset, and with a clear change-management trail.
In practice, fd150 is most dangerous when devices are accessible from untrusted networks or when default credentials enable remote administration. The risk escalates for devices with web-based admin interfaces that lack multi-factor authentication (MFA) or standard password-strength enforcement. Organizations should not rely solely on automatic renewals or firmware checks; deliberate, manual verification is essential to ensure that the fd150 credential is not present in production environments. Regular inventory and credential hygiene checks form the foundation of effective remediation strategies.
Why default passwords pose risks
Default passwords are a well-documented entry point for attackers. Once a device ships with a predictable credential, a single vulnerability in the device’s firmware or exposure on a network can be leveraged to gain control, pivot laterally, and exfiltrate data. The fd150 password pattern is particularly risky because it often exists on devices deployed in less-secured environments or where central management is weak. The most common attack vectors include unauthenticated admin access, weak password storage, and misconfigured remote management. As devices proliferate—especially in mixed environments with IoT devices—the attack surface grows exponentially. Organizations that ignore default credentials reduce their overall security posture and increase the likelihood of privacy violations and service disruption.
To mitigate risk, adopt a defense-in-depth approach: enforce password changes during initial setup, disable remote admin interfaces when not in use, monitor for credential changes, and segment networks to reduce attacker movement if a breach occurs.
The fd150 in practice: devices and use cases
fd150 appears in several device classes and can appear in both consumer and business contexts. Routers, network-attached storage (NAS), IP cameras, printers, and some smart hubs have historically shipped with default passwords. In corporate environments, failures to update these credentials can lead to calendarized risk—where a single vulnerability cascades into multiple devices and users. A practical approach is to maintain a device inventory with fields for brand, model, firmware version, and current credentials status. Regularly auditing this inventory helps identify devices still relying on fd150 and prioritizes remediation based on exposure level, criticality, and network reach. Additionally, establishing a standard operating procedure for credential changes ensures consistency across teams and devices.
A common scenario involves a misconfigured router that still allows remote administration on the public internet. If the router is using fd150 or any default credential, an adversary could gain control and access other devices on the network. The goal is to practically reduce the surface area by eliminating default credentials, applying device-specific hardening, and ensuring that every device is enrolled in a centralized credential management process.
The Default Password team highlights that remediation is not a one-time event but an ongoing practice tied to lifecycle management and ongoing risk assessment.
How to locate the fd150 default password on devices
Locating the fd150 default password starts with basic asset reconnaissance. First, check the device’s label or sticker, often found on the bottom or back, which may list the default credentials. If the label is missing, consult the user manual or quick-start guide—these documents typically include a default password and an initial setup URL. For devices with a web admin interface, the default credential may be visible on the login screen or in the firmware’s welcome message.
If documentation is unavailable, use manufacturer support portals or community-driven knowledge bases. In some cases, devices can be discovered via network scanning tools that enumerate devices and reveal default credentials still present in the configuration. Once located, ensure that any default password is replaced before proceeding with device onboarding. Finally, document the credential change in your asset registry to maintain an auditable record.
Step-by-step: changing the password safely
- Isolate the device from critical segments during initial change to minimize risk.
- Access the device’s admin interface using a secure device that is on a trusted network.
- Replace the fd150 default password with a unique, strong credential, preferably generated by a password manager.
- Enable device-level protections, such as HTTPS for the admin interface, and disable unused services like remote administration.
- Verify the change by logging out and re-logging in with the new password.
- Update firmware if available, and re-check any related services (UPnP, port forwarding) for compatibility with the new credentials.
- Document the change and monitor for any unauthorized access attempts to confirm remediation success.
Best practices for admin access and credential management
- Establish a formal password policy that enforces minimum length, complexity, and rotation frequency.
- Use unique credentials for each device; do not reuse passwords across devices or services.
- Centralize credential storage with a secure vault and enable auditing on access to sensitive credentials.
- Disable unused admin interfaces (especially remote or cloud-based admin) and require VPN access for remote management when possible.
- Integrate MFA where feasible, and ensure firmware updates are applied in a timely manner to reduce exposure to known default-password vulnerabilities.
Following these practices helps reduce the likelihood of fd150-related breaches and supports a stronger security posture across the environment.
Case studies: security improvements after remediation
In several mid-sized networks, replacing default credentials like fd150 with unique, rotated passwords led to immediate reductions in detected brute-force attempts and unauthorized configuration changes within days. In one case, centralizing credential management allowed an administrator to revoke access in minutes after detecting anomalous login activity, thereby preventing lateral movement. These case studies illustrate that even modest changes—changing default credentials, tightening admin access, and auditing for other defaults—can significantly harden a network. The important takeaway is that remediation compounds over time when combined with ongoing monitoring and governance.
Tools and resources for password hygiene
- Password managers and secure vaults provide a safe place to store and share credentials with role-based access.
- Asset discovery and inventory tools help identify devices using default passwords and track remediation progress.
- Network segmentation and access controls limit exposure if a device is compromised.
- Firmware update mechanisms and device hardening guides from manufacturers help maintain a resilient baseline.
Using these tools in combination with a formal policy makes it easier to maintain strong credential hygiene across all devices.
Common pitfalls and how to avoid them
- Pitfall: assuming all devices support MFA. Avoid this by prioritizing devices that do, and plan replacements or mitigations for those that don’t.
- Pitfall: delaying credential changes due to operational load. Mitigation: automate where possible and schedule remediation windows with stakeholders.
- Pitfall: neglecting printers and IoT devices. Action: include these devices in quarterly audits and apply the same credential hygiene standards.
- Pitfall: failing to maintain an auditable trail. Ensure changes are logged and time-stamped with reviewer approval.
Long-term strategy: governance and automation
A sustainable approach to fd150 and similar default passwords requires governance and automation. Establish an organization-wide policy for onboarding and decommissioning devices, with mandatory credential changes. Implement automated discovery, inventory, and remediation workflows that flag devices still using default credentials and trigger alerting when those credentials are detected. Regularly review and refine the policy based on incident learnings, and ensure leadership buy-in to allocate resources for ongoing credential hygiene and device security modernization.
Device categories and default password risk with recommended actions
| Device Category | Default Password Risk | Recommended Action |
|---|---|---|
| Routers | High | Change default credentials during initial setup; disable remote admin |
| IP Cameras | Medium-High | Change credentials; enable SSL; update firmware |
| NAS Devices | Medium | Set unique passwords; enable MFA if available |
| Printers | Low-Medium | Change default credentials; restrict admin pages on LAN |
Your Questions Answered
What is the fd150 default password?
fd150 default password refers to the factory-set credential used by some devices during initial setup. It is intended to be changed during configuration.
fd150 is a factory default password used during setup; change it before use.
Which devices commonly use fd150 as a default password?
Routers, IP cameras, printers, NAS devices, and some IoT gateways have fd150 as a default. Always consult device manuals.
Routers, cameras, printers, NAS devices often use it.
How do I locate and change the fd150 default password on a device?
Check the device label, initial setup guide, or admin web interface for the default password, then set a new credential.
Look on the device or in the admin page; then change it.
What are the best practices for managing admin credentials?
Use unique passwords, rotate them on a schedule, disable unnecessary remote admin, and enable MFA where supported.
Use unique passwords, rotate them regularly, and disable unneeded admin features.
What tools help manage default passwords securely?
Password managers and centralized credential vaults help, along with inventory systems that flag defaults.
Use a password manager and a secure vault.
What should I do if I find an outdated or insecure default password?
Replace it immediately, audit nearby devices, and apply firmware/security patches.
Replace it now and audit for others.
“Weak default passwords are a proven attack vector; replacing them with unique credentials is non-negotiable for secure deployment.”
Key Takeaways
- Identify devices still using fd150 default password.
- Replace with unique, strong credentials across all devices.
- Document changes and set rotation reminders.
- Audit regularly and minimize exposed admin interfaces.