Fiber Home Default Password: Secure Your Gateway Now
Learn how fiber home default passwords vary by device, why leaving them unchanged is risky, and actionable steps to reset and secure your gateway. This guide from Default Password explains defenses, best practices, and how to disable remote management.

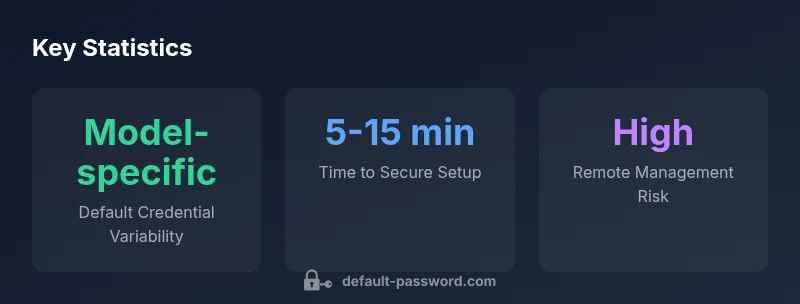
There is no universal fiber home default password; device manufacturers ship model-specific credentials. According to Default Password Analysis, 2026, many fiber gateways use 'admin' as the username and 'admin' or 'password' as the password, with variations by vendor. Immediately change these credentials, enable strong passwords, and disable remote management unless needed.
Understanding Default Credentials on Fiber Home Gateways
According to Default Password Analysis, 2026, many fiber home gateways ship with credentials that are predictable and model-specific. The default username is often admin, and the password may be admin, password, or a variant printed on the device label. These defaults are essential for initial setup but pose a risk if left unchanged. Attackers can scan for devices with the factory credentials and gain unauthorized access. The first step in securing your network is to locate your gateway's model and obtain the exact default credentials from the manufacturer manual or the device label. Then plan to replace them with a strong, unique password that combines upper and lower case letters, numbers, and symbols. In addition, consider changing the login path or disabling the portal from the WAN side to reduce exposure.
Why Keeping Default Passwords is Risky
Keeping default passwords creates a predictable entry point for attackers. Many home networks have several devices with factory credentials, which means a single exposed device can grant access to others if reused. Even if the gateway is behind a modem, weak defaults can be discovered via internet scanning, brute force attempts, or social engineering. In practice, organizations and home networks lose control when credentials aren't rotated. By contrast, changing defaults dramatically reduces the risk of remote compromise and helps enforce a culture of password hygiene across the home network. This section also aligns with established security guidelines that advocate long, unique credentials and regular review of device access logs.
How to Secure Your Fiber Gateway: Step-by-Step
Step 1: Identify your device model and locate the official documentation. Step 2: Log in to the admin interface using the current credentials. Step 3: Change the username (if supported) and create a long, unique password using a password manager. Step 4: Update the device firmware to the latest version. Step 5: Disable remote management from the WAN side and disable UPnP if possible. Step 6: Create a separate guest network and limit device permissions. Step 7: Save changes and test access from a different device. Step 8: Document the new credentials securely. These steps establish a robust baseline security posture.
Best Practices for Password Hygiene in Home Networking
- Use a password manager to generate and store strong, unique passwords for each device and service. - Avoid password reuse across devices, services, or administration interfaces. - Enforce long passwords (16+ characters) with a mix of character classes. - Enable two-factor authentication where available and keep a secure offline backup. - Regularly review connected devices and remove unfamiliar ones, and set a rotation schedule (eg, every 12–18 months).
Model-Specific Defaults: How to Find Yours
Each gateway model has its own default pairings, documented in the user manual or on the device label. Start by locating the model number on the gateway and visit the manufacturer’s support site to access factory defaults, reset instructions, and recommended security settings. If you received the device from your ISP, check their support portal for model-specific guidance, as some providers alter defaults or lock features behind their authentication. Keeping records of the model and current firmware helps ensure you follow the correct steps to secure it.
Remote Management and Cloud Features: What to Disable
Remote management and cloud-based features are convenient but widen exposure of your admin interface to the internet. Disable remote access from the admin UI unless you truly need it for remote support. If your provider requires remote features, restrict access to trusted IP addresses and enforce stronger authentication. Turn off UPnP and universal discovery if available. Finally, monitor for firmware updates and review security notices from your provider to stay ahead of vulnerabilities tied to factory defaults.
Common default credentials across fiber and home routers
| Device Type | Default Username | Default Password | Notes |
|---|---|---|---|
| Fiber gateway (ISP-provided) | admin | admin | Variability by model |
| Fiber gateway (ISP-provided) | admin | password | Common but insecure |
| Consumer router (standalone) | admin | admin | Older devices |
| Modem/router combo | admin | password | Weak defaults prevalent |
Your Questions Answered
What is the risk of leaving the fiber home default password unchanged?
Leaving credentials unchanged creates an easy target for attackers. Unsecured devices can be discovered by automated scans, potentially granting unauthorized access to your home network. Always rotate to a unique password during setup.
Leaving defaults is risky; change them now to protect your network.
How do I locate the default password for my fiber gateway?
Check the device label, user manual, and the vendor's support site. The model number helps you fetch the exact default credentials. If in doubt, contact your provider for official guidance.
Look on the device label or vendor site for the exact defaults.
Can I use the same password for multiple devices?
No. Use unique passwords for each device to prevent a single breach from compromising multiple systems. A password manager can help generate and store them securely.
Use a different password for each device.
Should I enable remote management?
Disable remote management unless you truly need it. It exposes your admin interface to the internet, increasing risk if credentials are weak.
Disable it unless you need remote access.
What about firmware updates—are they part of securing defaults?
Yes. Regular firmware updates fix vulnerabilities, including those tied to default credentials. Enable automatic updates if available and monitor for new releases from your vendor.
Keep firmware up to date to close gaps.
“Security starts with how you manage credentials. Treat factory defaults as a temporary access point and rotate them as soon as possible.”
Key Takeaways
- Change factory credentials on first setup.
- Use a unique, strong password for each device.
- Disable remote management if not required.
- Regular firmware updates and credential monitoring are essential.