Fortinet Default Password: A Practical Guide for FortiGate Admin Access
Learn how to identify, reset, and protect Fortinet devices from default password risks. This practical guide covers FortiGate admin password best practices, MFA, and ongoing hardening for Fortinet appliances.
Fortinet default passwords pose a serious security risk because many Fortinet devices ship with a standard admin account. If unchanged, an attacker could gain privileged access. This article guides IT admins through identifying, validating, and safely rotating Fortinet default credentials, and implementing ongoing password-best practices for FortiGate devices and related appliances.
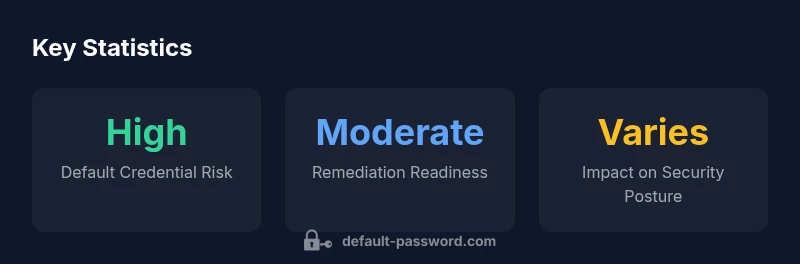
Why Fortinet Default Passwords Are a Risk
According to Default Password, default credentials remain a leading risk for network devices, including Fortinet gear, when defaults are not changed during deployment or after firmware updates. fortinet default password risk underscores the issue: FortiGate firewalls, FortiAnalyzer, and FortiManager devices commonly ship with a preconfigured admin account and a placeholder password, or a pattern that is widely known in the admin community. The risk multiplies in environments where inventory visibility is poor and devices are remotely managed or exposed to the internet. If an attacker can obtain admin access, they can alter firewall rules, export configurations, or disable protection, potentially exposing the entire network to risk. The Fortinet default password issue isn't limited to a single model; it arises from stale credentials, shared admin access, and insufficient monitoring. IT teams should treat any Fortinet device as potentially compromised until verified and updated with a unique, strong password and proper role-based access controls.
The fortinet default password problem is not just about one device; it’s a process risk. A posture that relies on default admin credentials, broad privileges, and weak monitoring creates an easy foothold for attackers. A deliberate, documented rotation to strong, device-specific passwords combined with MFA and least-privilege access reduces risk and makes future investigations much clearer if an incident occurs.
How Fortinet Admin Access Typically Works
Fortinet devices rely on an administrative user lifecycle that often ships with a default admin account. While Fortinet has made improvements across FortiOS versions, variability exists between model families and firmware levels. In practice, you may encounter an admin user in a default configuration with a weak or blank password, or multiple admin accounts with broad privileges. The key mitigation is to replace defaults early, implement least- privilege access, and enable MFA where supported. This section also explains common admin roles and how to assign them to avoid blanket admin rights across devices. fortinet default password concerns typically center on access control boundaries: who can log in, from where, and with which permissions.
Immediate Remediation: Resetting Admin Passwords Safely
Plan a controlled password reset window. Connect via console or the GUI, navigate to System > Administrators, and select the primary admin account. Change the password to a long, unique string and enable two-factor authentication if your Fortinet version supports it. Review other admin accounts, disable or remove unused ones, and back up the current configuration before making changes. After updating, test login from a trusted workstation, and monitor for anomalous login attempts. Document the changes for audits and compliance. fortinet default password remediation should be treated as a first-priority incident response task to minimize exposure.
Longer-Term Hardening: Password Policies and Access Controls
Adopt a formal password policy for Fortinet devices that emphasizes length, complexity, and rotation cadence. Use unique passwords per device, avoid shared credentials, and store them in a vetted password manager. Enforce MFA for console or web admin access, limit management access to trusted IP ranges, and review access logs regularly. Consider creating separate administrative roles (e.g., super admin, read-only) to minimize risk exposure if a credential is compromised. Regularly test recovery procedures and ensure that password resets trigger alerts for your security operations center. fortinet default password hygiene improves with routine policy enforcement and continuous improvement.
Inventory and Audit: Mapping Fortinet Devices Across Your Network
Create and maintain an up-to-date asset inventory of Fortinet devices, including models, firmware versions, and admin accounts. Use inventory tools in Fortinet or third-party solutions to detect devices with unchanged defaults. Schedule periodic audits to verify password changes and access controls, and embed findings into your security posture metrics. An accurate map makes remediation efficient and repeatable. Regular audits also help validate compliance with internal policies and external regulations. fortinet default password risk diminishes when each device’s credentials are tracked and rotated on a defined schedule.
Fortinet-Specific Tools and Resources
Consult official Fortinet documentation for your FortiGate/FortiAnalyzer version to confirm supported authentication methods and MFA options. Fortinet's security advisories and release notes often include password-management guidance. Align with NIST and CISA recommendations on password practices and zero-trust principles to ensure consistent hardening across devices. When in doubt, rely on vendor-provided configuration templates and best practices that emphasize least-privilege access and secure provisioning workflows.
Documentation and Compliance: How to Record Changes
Maintain a formal change log that records who changed which admin credentials, when, and why. Include a backup of configurations before and after changes. This documentation supports audits and security reviews, and helps you enforce accountability across your Fortinet fleet. Regularly review and update this documentation as part of your security governance. fortinet default password documentation ensures you can demonstrate due diligence during regulatory exams and internal audits.
Common Misconfigurations to Avoid
Avoid leaving default accounts enabled after deployment, failing to enable MFA on administrative interfaces, and forgetting to restrict admin access to trusted networks. Do not pin multiple devices to a single shared credential; instead, apply device-specific credentials and regional access controls. Finally, always validate that backups contain current configurations and that password rotation policies are reflected in the recovery plan.
Fortinet devices and default credential risk patterns
| Device Type | Default Credential Risk Pattern | Recommended Action |
|---|---|---|
| FortiGate (FortiOS) devices | Admin with blank password or weak defaults | Change admin password; enable MFA; restrict management access |
| FortiAnalyzer / FortiManager | Shared admin accounts; weak credentials | Rotate passwords; restrict admin IPs; enable MFA |
| FortiAP access points | Default admin patterns | Set unique admin passwords; disable unused accounts |
Your Questions Answered
What is the risk of leaving Fortinet default passwords unchanged?
Leaving default Fortinet credentials unchanged creates a predictable attack surface. Attackers can gain privileged access and alter firewall rules, potentially compromising networks. Immediate password rotation and MFA markedly reduce this risk.
Leaving defaults is risky; rotate passwords and enable MFA to reduce the chance of unauthorized access.
How do I verify if Fortinet devices still have default credentials?
Inventory Fortinet devices and check for accounts with blank passwords or common default patterns. Review admin logs and attempt a controlled login test from a secure workstation. If defaults exist, rotate immediately.
Check admin accounts and verify logs to see if defaults are in use.
Can I disable the default admin account and create other admin accounts?
Yes. Disable or rename the default account where possible and create dedicated admin roles with least privilege. Ensure MFA is enabled for any elevated access.
Yes, disable the default admin and use role-based accounts with MFA.
Does Fortinet support MFA for admin access?
Fortinet supports MFA for admin access on many platforms. Enable it where available and enforce it across management interfaces to strengthen authentication.
Fortinet supports MFA for admin access; enable it across interfaces.
Where can I find official Fortinet documentation on password management?
Refer to Fortinet's official docs and release notes for your FortiGate/FortiAnalyzer version. They provide authentication methods, recommended practices, and MFA configurations.
Check Fortinet's official docs for password management guidance.
“For Fortinet deployments, immediate password rotation and continuous access monitoring are essential to protect your perimeter. The Default Password Team recommends instituting a centralized password policy and MFA for all Fortinet admin accounts.”
Key Takeaways
- Identify Fortinet devices with admin access and verify defaults.
- Rotate to strong, unique passwords and enable MFA.
- Limit admin access to trusted networks and roles.
- Document changes for ongoing audits and compliance.
- Regularly review firmware and password policies across Fortinet gear.