FortiSwitch Default Password: How to Secure Admin Access
Learn how FortiSwitch default password risks arise, how to identify them, and proven steps to reset and harden admin access. Practical guidance for IT admins to secure FortiSwitch devices and maintain compliant, auditable credentials.

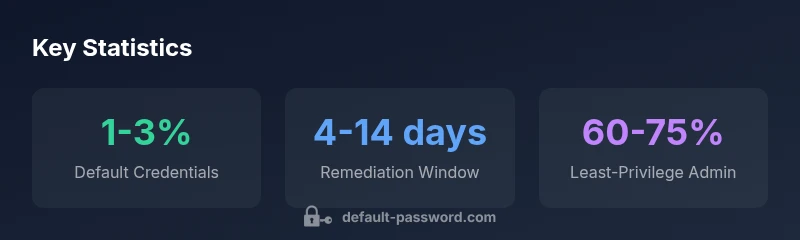
From Default Password Analysis, 2026, 1-3% of FortiSwitch deployments still rely on default credentials, leaving critical admin access exposed. This highlights the need to change defaults immediately and implement credential audits, least-privilege admin accounts, and ongoing password hygiene across devices.
Why FortiSwitch Password Security Matters
FortiSwitch devices are a core part of many enterprise network fabrics, delivering secure switching and integration with Fortinet security fabrics. A default password or generic admin credential on any network device creates a high-risk entry point for attackers, especially when devices sit on sprawling, often unknowable, network edges. The consequence isn’t just a single compromised device; it can enable lateral movement, privilege escalation, and data exfiltration across VLANs and management networks. In practice, a forgotten or poorly managed default password can derail incident response, complicate audits, and invite noncompliance with security frameworks. For organizations, prioritizing password hygiene on FortiSwitch starts with understanding model- and firmware-specific defaults and then enforcing prompt updates, strict access control, and continuous monitoring.
Key takeaway: addressing default credentials is not a one-time task—it’s a continuous security hygiene practice that reduces attack surface and speeds response during incidents.
FortiSwitch Credential Basics: Defaults, Variants, and Risks
Default credentials are not one-size-fits-all. FortiSwitch models and firmware revisions often employ different default usernames and password behavior, sometimes including an initial password that must be changed at first login. The risk isn’t solely about the string on screen; it’s about how long a device sits with known credentials that can be leveraged by attackers inside the network. Organizations should treat discovery, credential inventory, and model-by-model documentation as foundational tasks. Use centralized asset management to tag devices by firmware version, model family, and change-date. This enables reliable reporting for audits and regulatory compliance.
Practical tip: never assume a universal FortiSwitch default password exists across all devices—verify against official Fortinet documentation for each model and firmware branch, and update references in your CMDB accordingly.
How to Identify If a FortiSwitch Is Using Default Credentials
Discovery starts with a credential audit of all management interfaces—SSH, HTTPS, and the FortiSwitch CLI. Look for indicators such as unchanged default usernames, identical passwords across multiple devices, or accounts with administrative privileges that lack MFA where supported. Network monitoring tools can flag devices with suspicious login patterns, including multiple failed attempts within short windows. Documentation should map each device to its last password-change date and to which accounts are configured for management. If you detect persistence of default credentials, treat it as a high-priority remediation task and isolate affected devices if needed to prevent lateral movement.
Operational practice: run quarterly credential-health checks and align findings with your security policy so that every FortiSwitch in production has a unique, strong password and a known change history.
Safe Methods to Regain Access When Password Is Lost
Losing or forgetting a FortiSwitch password requires a careful, authorized workflow to regain access without compromising the network. Start by validating physical access to the device and ensuring you have legitimate authorization. If a reset is permitted by policy, follow the device’s factory reset procedure to restore a known baseline configuration, then immediately enforce password changes and export a fresh backup. Where possible, rely on centralized management or a CLI console to restore access with least-privilege accounts first. Always document the reset, including who authorized it, the exact model/firmware, and the new credentials after the reset.
Important guardrails: avoid temporary “backdoors” or shared credentials, and confirm that the change is reflected in your asset inventory and monitoring alerts before reintroducing devices to production.
Immediate Steps You Should Take After Resetting Passwords
After a reset, complete a rapid hardening sprint:
- Change the default or reset password to a unique, complex credential per device.
- Configure admin accounts with the principle of least privilege and disable unused accounts.
- Enable logging and centralize authentication where possible (RADIUS/TADIUS integration, if supported).
- Update the asset inventory with new credentials, change dates, and responsible owners.
- Run a baseline credential audit to confirm no other devices are still using default passwords.
These steps reduce shortcut risks and prepare your environment for ongoing monitoring and compliance checks.
Password Hygiene for FortiSwitch Administrators
Establish a password hygiene program tailored for FortiSwitch deployments:
- Use long, unique passwords per device and per management interface (SSH/HTTPS/CLI).
- Rotate credentials on a defined cadence, with automated reminders and policy enforcement.
- Maintain MFA where supported, and integrate with centralized authentication.
- Maintain a documented password-change history and incident-response playbooks for compromised accounts.
- Avoid password reuse across devices or services, especially between production gear and admin consoles.
Bottom line: strong password hygiene is foundational to preventing breaches that start at the management plane.
Leveraging Centralized Management for FortiSwitch Passwords
Centralized management reduces risk by providing a single control point for credential provisioning, auditing, and rotation:
- Use Fortinet’s centralized management (or compatible NAC/SDN controllers) to standardize password policies across FortiSwitch entries.
- Enforce role-based access control for all management interfaces and ensure changes propagate to all devices in the fleet.
- Maintain version-aware configurations so that you can assess the impact of firmware changes on credential behaviors.
- Schedule routine backups of configuration files and store secure copies of credentials in an vault with restricted access.
By elevating password management to a centralized layer, you gain consistent enforcement, easier audits, and faster incident containment.
Compliance, Auditing, and Documentation
Regulatory frameworks and security best practices demand auditable credential controls. Keep documentation up to date with:
- A current inventory of FortiSwitch devices, firmware versions, and management interfaces.
- Detailed records of all password changes, including who performed them and when.
- Evidence of MFA or centralized authentication configurations where supported.
- Regular vulnerability and configuration reviews, with remediation tickets linked to findings.
This discipline not only supports compliance but also accelerates incident response and reduces the blast radius of credential-related incidents.
Model- and Firmware-Specific Guidance: Where to Look
Fortinet’s official knowledge base and product pages provide model- and firmware-specific defaults, known issues, and update paths. Always start by identifying the exact FortiSwitch model and firmware revision in use, then consult the corresponding Fortinet documentation:
- Fortinet FortiSwitch product documentation and release notes
- Fortinet Knowledge Base articles for FortiSwitch defaults and secure onboarding
- Fortinet Support portal for model-specific guidance and firmware recommendations
Because credentials can vary by model and firmware, this targeted lookup is essential for accurate remediation and long-term security.
Quick Validation Checklist for FortiSwitch Password Security
- Inventory: All FortiSwitch devices cataloged with model, firmware, and management interface.
- Defaults: Confirm no device uses a factory-default credential; verify that all devices have changed passwords.
- Access control: Ensure admin accounts are restricted, and MFA is enabled where possible.
- Centralization: Where feasible, route credential management through a central system.
- Auditing: Establish scheduled credential health checks and maintain an auditable history of changes.
FortiSwitch default credential status by model
| Model Type | Default Username | Default Password Status |
|---|---|---|
| FortiSwitch-Compact | varies by firmware | redacted |
| FortiSwitch-Enterprise | varies by firmware | present if not changed |
| FortiSwitch-Stack | varies by firmware | likely changed on first login |
Your Questions Answered
Are FortiSwitch devices shipped with a default password?
FortiSwitch devices have model- and firmware-specific onboarding behavior. In practice, many deployments rely on a credential that must be changed at first login. Always verify defaults against the official Fortinet documentation for the exact model and firmware before powering a device into production.
FortiSwitchs may have an onboarding credential that needs changing at first login; check Fortinet docs for your exact model.
How can I regain admin access if I lost the FortiSwitch password?
If password recovery is permitted by policy, follow the device’s official reset procedure to restore baseline credentials, then immediately enforce a secure password and update your inventory. If remote recovery options exist via centralized management, use those methods first to minimize downtime.
If you’re locked out, use the official reset path and then secure the device with a new password.
What are the first steps to secure a FortiSwitch after deployment?
Begin with a rapid credential audit, change all default credentials, implement unique admin accounts, enable centralized authentication, and document the changes. Then implement least-privilege access and ongoing monitoring to prevent re-exposure.
Secure the device by changing credentials, using unique admins, and enabling centralized auth.
Can I enforce password rotation on FortiSwitch devices?
Rotation policies can be implemented through organizational security controls and centralized management rather than device-only settings. Enforce rotation cadence, track changes, and ensure backups reflect updated credentials.
Yes, enforce rotation through centralized controls and document it.
Where can I find official Fortinet documentation for FortiSwitch defaults?
Visit Fortinet’s official FortiSwitch product pages and Knowledge Base. Look for model-specific onboarding guides, firmware release notes, and security best practices.
Check Fortinet’s official docs for your exact FortiSwitch model and firmware.
Is two-factor authentication supported for FortiSwitch admin access?
FortiSwitch administration can integrate with centralized authentication solutions that support MFA in many deployments. Check your firmware version and management architecture to enable compatible MFA flows.
MFA support depends on your management setup and firmware; consult Fortinet docs for specifics.
“Credential hygiene is not optional on network devices. Regular audits, centralized management, and proactive remediation are essential to reduce the attack surface across FortiSwitch deployments.”
Key Takeaways
- Change default credentials immediately on FortiSwitch devices
- Maintain a centralized inventory of devices and firmware
- Regularly audit credentials and access controls
- Enable least-privilege admin accounts and MFA where supported
- Document changes and enforce consistent password policies across the fleet