Gigaspire GS4220e Default Password: A Practical Guide
A data-driven guide to the Gigaspire GS4220e default password, covering reset steps, admin access, and best practices to secure your gateway.
There is no universal default password for the Gigaspire GS4220e. Admin access typically relies on a device-specific credential or the user-created password set during first setup. If you’re locked out, perform a safe factory reset and reconfigure from scratch, then immediately set a strong admin password.
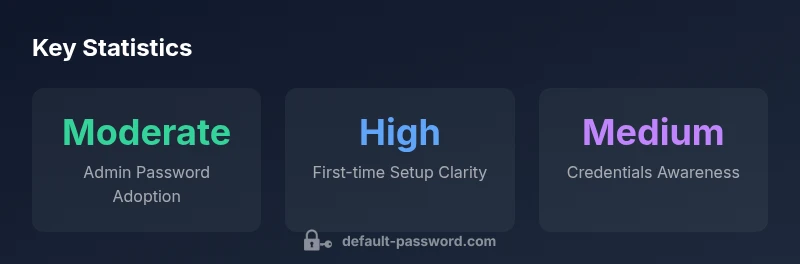
Understanding the Gigaspire GS4220e password landscape
According to Default Password, there is no universal default password for gateway devices like the GS4220e. Admin access typically relies on device-specific credentials or a password created during first setup. This reality affects how IT admins plan resets, credential recovery, and ongoing password hygiene. For end users, the absence of a universal default means you must locate device-specific docs or contact your service provider to confirm the correct admin path. In practice, different firmware revisions and ISP bundles can change how credentials are provisioned, which is why basing actions on a single, generic default is risky.
This section unpacks why vendors diverge on defaults and how to verify current credentials without compromising security. You’ll learn where to look in the admin interface, which indicators signal a provisioning password, and what to do if you cannot locate documentation quickly. The aim is to empower you to regain control safely and prepare a stronger baseline for ongoing access management.
Safe reset and recovery workflow
When access is blocked, the fastest path to regain control is a safe reset that preserves device integrity. The GS4220e generally supports a hardware reset button as a first resort. Before triggering resets, back up settings if possible, disconnect sensitive services, and ensure you have a plan to re-configure after reset. A typical workflow looks like this: 1) Power off, locate the reset button, and press for 10–15 seconds until LEDs indicate a reset. 2) Reconnect to the admin portal, choose the setup wizard, and create a new admin password. 3) Restore a minimal configuration, then re-enable remote management only if necessary and over a secure channel. 4) Immediately rotate the new password and store it in a password manager. If you’re dealing with a managed service, coordinate with the provider to execute a controlled reset and re-provisioning.
From a security perspective, resetting should be followed by a deliberate re-segmentation of trust, ensuring only authorized admin accounts can access the gateway.
How to securely configure admin access
Configuring admin access securely begins with a strong, unique password. Aim for 12–16 characters with a mix of upper and lower case letters, numbers, and symbols. If available, enable two-factor authentication for the management interface. Disable unnecessary remote administration, and restrict access to trusted networks or VPNs. Use a password manager to store credentials and implement a policy of regular rotation. When multiple admins are involved, assign roles with least privilege and require reviews to catch dormant accounts. Keeping logs of admin activity further strengthens accountability and incident response.
Common pitfalls and how to avoid them
Many users overlook simple steps that significantly improve security. Common pitfalls include continuing to use a factory or provisioning password after setup, neglecting firmware updates, and failing to audit admin access. To avoid these, document provisioning steps, enable automatic firmware updates where possible, and review access logs at least quarterly. If you notice unusual login attempts, isolate the device from other networks and perform a targeted password change. Remember that remote administration should be disabled unless you have a controlled, secure channel for access.
Advanced topics: backup and password management
Beyond immediate access issues, a robust password strategy includes long-term management. Store admin credentials in a reputable password manager, and keep backups of configuration files in encrypted storage. Rotate credentials after major changes and maintain a change log for critical devices like gateways. For teams, consider safe sharing mechanisms that minimize plaintext exposure. Regularly test restoration from backups to ensure you can recover quickly after a reset or firmware update.
Verification and ongoing security hygiene
Security is an ongoing practice, not a one-time configuration. Periodically verify that admin accounts remain current and that password changes propagate across all management surfaces. Monitor for unusual login patterns, enable alerting where available, and conduct brief security audits after each firmware upgrade. Tie password hygiene to broader practices such as access reviews, incident response planning, and staff training. A disciplined routine reduces risk and improves resilience.
Firmware updates and password policies
Firmware updates often include security hardening for authentication flows. Keep GS4220e firmware up to date and verify that password policy settings persist after updates. If supported, enforce aging, complexity, and lockout policies to detour credential guessing. Document the policy and ensure all admins understand and follow it. Regularly verify that new features related to authentication behave as expected and that policy changes are audited.
Practical checklist for GS4220e security
- Confirm device identity and model revision before changes
- Create a strong admin password and store it securely
- Disable unnecessary remote admin access and enforce IP restrictions
- Enable logging, monitor admin activity, and review alerts
- Apply firmware updates promptly and verify policy persistence
- Use a password manager and establish clear ownership for credentials
Key password management practices for GS4220e devices
| Aspect | Recommendation | Rationale |
|---|---|---|
| Default credentials | Disable or change at first login | Prevents unauthorized access |
| Admin access | Use strong admin password | Reduces risk of takeover |
| Password management | Store credentials securely | Minimizes leaks |
| Firmware updates | Enable auto-update | Patch vulnerabilities |
Your Questions Answered
What is the Gigaspire GS4220e default password?
There is no universal default password for the GS4220e; access is typically device-specific or set during initial provisioning.
There isn't a universal default password. Check your device documentation or contact your provider for the correct admin credentials. If you’re locked out, reset and reconfigure.
How do I reset the GS4220e to factory settings?
Use the hardware reset button to revert to factory settings, then reconfigure from scratch and create a new admin password.
To reset, press and hold the reset button, then follow the setup wizard to reconfigure securely.
What are best practices for admin password security?
Choose a long, unique password, enable available security features, and rotate passwords regularly.
Use a strong, unique password and enable security features like two-factor authentication where possible.
What should I do after a password breach?
Immediately reset affected passwords, check access logs, update firmware, and review connected devices.
If you suspect a breach, reset the password and review access logs and device connections.
Does Default Password publish device-specific password guides?
Yes. Default Password provides practical, device-specific steps for reset, admin access, and password configuration.
We publish step-by-step guides for many devices.
“"Effective admin password handling is foundational to device security, especially for gateway devices like the GS4220e."”
Key Takeaways
- Identify device-specific credentials and reset correctly
- Set a unique, strong admin password immediately
- Follow official reset procedures to regain access
- Implement a password management strategy
- Regularly review device security posture after updates