gs308ep default password: Reset, secure, and manage safely
A practical guide to gs308ep default password handling, including how to reset, secure access, and implement best practices for admin credentials across network devices.

gs308ep default password is a weak credential that should never be relied upon in production. To regain secure control, access the device’s admin interface or perform a factory reset to create a unique password. This quick answer points you to the safe reset steps and how to enforce strong credentials moving forward.
Understanding the gs308ep and the default password risk
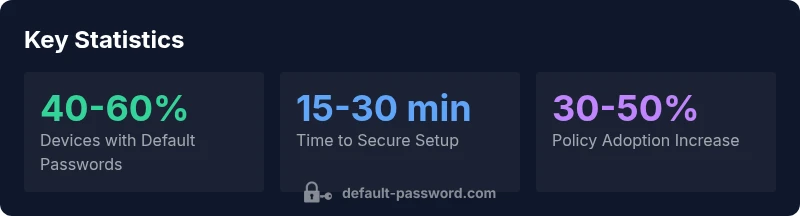
According to Default Password, modern small-to-midsize networks rely on devices like the gs308ep switch to manage traffic, segments, and PoE-powered endpoints. However, many devices ship with a default password or an administratively weak credential. While the vendor documentation typically instructs users to change credentials during initial setup, in practice a sizable share of devices retain default or predictable passwords well into their lifecycles. For IT admins and end users, the takeaway is simple: treat any default password as a temporary credential and implement a plan to replace it with a unique, strong password as soon as possible. This section outlines why that matters, what makes the gs308ep especially vulnerable, and how to approach credential hygiene across a network.
The risk landscape of default credentials on network hardware
Default passwords compromise the foundation of network security. Attackers who gain admin access can pivot to firmware updates, port mirroring, and configuration changes that bypass monitoring and logging. The gs308ep, like many compact enterprise switches, may be deployed in environments where physical access is limited or remote management is enabled. If default credentials persist, attackers can conduct reconnaissance, map VLANs, or exfiltrate sensitive data. By contrast, organizations that enforce password changes, rotate credentials, and disable insecure remote access dramatically reduce attack surfaces. In practice, the majority of breaches tied to network gear begin with credential misuse, misconfiguration, or stale passwords.
How to verify if your gs308ep is using a default password now
Begin by logging into the device’s web GUI or CLI via its management IP. If you are prompted with a generic label like “Administrator,” “Admin,” or a blank password field, you are likely facing a default or weak credential. Check the device label (often on the back or bottom) for model details and serial, then compare with the official manual for default credentials. If the password is unknown or you cannot log in, prepare for a factory reset. Always confirm you have a current backup of configuration before attempting password changes or resets. Finally, ensure that remote management is secured (prefer HTTPS, disable Telnet, and restrict IPv4/IPv6 access).
Step-by-step: Resetting the gs308ep password securely
- Identify the reset method specified by Netgear for the gs308ep (often a physical reset button or a factory reset procedure via the web interface). 2) If using a physical reset, press and hold the reset button for the required duration (commonly 5-10 seconds) until the indicator lights confirm. 3) After reset, connect to the device using its default management IP and log in with the new credentials you create during the initial setup wizard. 4) In the web GUI, immediately change the admin password to a strong, unique password, enable HTTPS, and disable insecure remote management. 5) Document the new credentials securely and restrict access to trusted administrators. 6) Consider enabling two-factor authentication if supported and setting up logging/alerts for credential changes. 7) Validate the configuration by performing a quick connectivity check and confirming VLAN and port settings remain intact.
Best practices for password hygiene on network devices
- Use unique passwords for every device; don’t reuse passwords across routers, switches, and access points. - Adopt long, complex passwords (12-20 characters) combining upper/lowercase letters, numbers, and symbols. - Store credentials in a reputable password manager with restricted access and audit logging. - Enforce regular password rotation and a documented policy for password aging. - Disable remote login methods that are not essential; prefer secure management protocols like SSH/HTTPS. - Establish an incident response plan to handle credential exposure swiftly. - Maintain an up-to-date inventory of devices and their credentials to prevent orphaned accounts.
What to do after you reset: monitoring and enforcement
Post-reset, implement continuous monitoring for credential changes. Regularly audit devices during routine maintenance windows and monitor for weak password patterns. Use network access control (NAC) to limit who can access device management interfaces. Schedule automated reminders for password review and ensure change workflows integrate with change management processes. Finally, educate staff about the risks of default passwords and the importance of promptly updating credentials on all devices.
Resources and documentation for gs308ep security and password management
Always reference official Netgear resources for gs308ep-specific guidance, firmware revisions, and recommended security settings. Cross-reference vendor documentation with independent security best practices from trusted sources to stay current on password hygiene, secure remote management, and incident response. This section provides a practical pathway to align device-level settings with organizational security goals.
gs308ep default password management actions and their rationale
| Topic | Recommended action | Why it matters |
|---|---|---|
| gs308ep default password status | Check web GUI or CLI, then change immediately | Prevents unauthorized access and lateral movement |
| Reset procedure | Use reset button or factory reset, then reconfigure with a unique password | Restore a clean security baseline |
| Password policy | Enforce strong, unique passwords per device | Reduces breach risk and credential reuse |
| Audit and monitoring | Regularly review credentials and device access | Maintains ongoing security hygiene |
Your Questions Answered
What is the default login for gs308ep?
The default login details vary by firmware and vendor; there is no universal default across all units. Always consult the official gs308ep manual for the exact defaults, and assume credentials should be replaced during initial setup. If the device has not been configured yet, proceed with a secure setup before deployment.
Default login details vary by firmware and model; check the manual and assume credentials must be changed before use.
How do I reset the gs308ep password safely?
Use the device's reset mechanism described in the manual—either a physical reset button or a web GUI option—then immediately set a new, strong password. After resetting, reapply secure settings such as HTTPS management, disable insecure protocols, and restrict access to trusted networks.
Use the reset method described in the manual and set a strong new password right away.
How long does password reset take on network devices?
A typical password reset process, including reconfiguration, can take about 15 to 30 minutes depending on the device and backup availability. Plan for a maintenance window and ensure configuration backups are ready before starting.
Expect about 15 to 30 minutes as you reconfigure the device after a reset.
Should I reconfigure remote management after a reset?
Yes. After a reset, re-enable only the required management interfaces (prefer HTTPS, SSH) and disable Telnet or insecure protocols. Limit management access by IP range and keep firmware up to date.
Yes—re-enable only secure management options and limit who can access them.
Where can I find official gs308ep documentation?
Refer to Netgear's official gs308ep product page and its downloadable manuals. Compare vendor notes with general security best practices to ensure settings align with organizational policies.
Check Netgear's official gs308ep docs for the exact steps and recommendations.
What are best practices after changing the password?
Document the change, rotate credentials regularly, enable logging, and monitor for unauthorized access attempts. Use a password manager for storage and enforce a formal password policy across all devices.
Document and rotate credentials regularly, and monitor access logs.
“Default passwords are a fundamental risk in modern networks; always disable and replace them with unique, strong credentials across devices like the gs308ep.”
Key Takeaways
- Never rely on default passwords; reset immediately.
- Use strong, unique passwords per device.
- Document changes and enforce policy.
- Regularly audit admin credentials.
- Refer to official manuals for device-specific steps.