GitLab Default Login: Secure Admin Access Guide
Learn how to manage gitlab default login, reset admin credentials, and enforce strong authentication to protect GitLab instances. This guide from Default Password explains practical steps and best practices.
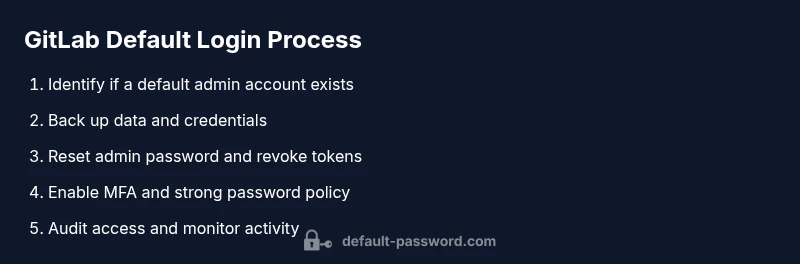
In this guide, you'll learn how to manage gitlab default login safely: identify whether a default admin account exists, securely reset credentials, and enforce password and access controls. According to Default Password, weak or unchanged default logins are a common entry point for attackers, so acting quickly matters for GitLab instances and admin access.
What gitlab default login means in practice
GitLab default login is not a fixed credential across all deployments. In most official GitLab installations, there is no universal preset user/password pair waiting to be discovered. The real risk arises when administrators or vendors ship images with credentials pre-populated, or when someone forgets to change an initial admin password after setup. For end-users and IT admins, understanding the difference between a prepared setup and a stale, unchanged credential is essential. Throughout this guide, the primary concern is preventing unauthorized access through weak or unchanged defaults and establishing a repeatable process to verify and reset credentials when needed. The phrase 'gitlab default login' is often used to describe scenarios where a pre-configured account is still in place in a running instance, or where access has become easier due to misconfiguration, poor password hygiene, or insecure tokens. The Default Password team emphasizes that any instance with unchanged default credentials should be treated as high-risk until it is remediated. In practice, you should always assume that default login details exist nowhere in your environment unless proven otherwise, and you should implement controls that prevent their exploitation.
How GitLab handles authentication during installation
GitLab's authentication flow is designed to require explicit administrator setup during installation. The recommended practice is to create or claim the admin account and assign a strong password, then enable or enforce multi-factor authentication (MFA) where possible. Some prepackaged images or vendor deployments may carry preconfigured credentials; this is discouraged and should be considered a temporary bridge only. Always audit the initial setup steps in your deployment guide and verify that no default passwords are left roaming in environment files, container images, or vault configurations. The key point is to separate the concepts of 'initial setup' from 'default login', and to implement controls that prevent exploitation if a credential is inadvertently reused. For those managing multiple GitLab instances, establish a standardized onboarding flow that requires users to set admin credentials on first login and to rotate them on a defined schedule.
Risks of leaving default credentials unchecked
Leaving default credentials unchecked creates high-risk scenarios, including unauthorized admin access, data exfiltration, and service disruption. Attackers often target misconfigured GitLab instances with weak passwords, stale sessions, or long-lived tokens. The most common vectors include exploiting forgotten admin passwords, abusing compromised personal access tokens, and leveraging unmonitored API keys. In practice, a lack of credential hygiene can enable attackers to pivot from a compromised account to the entire GitLab environment, potentially affecting repositories, pipelines, and CI/CD configurations. Organizations should treat any hint of a default login as a critical incident and initiate an immediate containment plan: revoke tokens, rotate keys, and review access controls. Regular security reviews and automated checks can help identify dormant accounts, dormant credentials, and insecure backup locations before they become a problem.
Recovery and reset workflow: getting back into GitLab
If you suspect you or an administrator has lost access due to a default login or forgotten password, follow a structured recovery workflow. Start by validating access to the GitLab host (SSH or console) and locating any admin accounts that could be used for recovery. Next, reference the official GitLab recovery documentation and perform a password reset for the admin user or, if needed, reset via the supported Rails console method described in the docs. After resetting, immediately revoke active sessions and review all API tokens and deploy keys. If more than one admin exists, use the recovery accounts to preserve access while reducing blast radius. Finally, reconfigure authentication: enable MFA, enforce password complexity, and apply the latest patches. Document every action for audits and rollback.
Hardening your GitLab instance after reset
Hardening after the reset means instating stronger guardians against unauthorized access. Enable MFA for all administrators, require strong password policies, and rotate credentials on a defined cycle. Consider enabling IP allowlists or SSO so that the primary login mechanism isn't solely a local password. Review and prune any dormant user accounts, service accounts, and tokens. Revoke legacy tokens, keys, and CI/CD credentials that could be misused if left active. Backup and test your backup recovery process. Establish an alerting regime for unusual login patterns and failed authentication attempts. Finally, implement a policy framework that codifies password rotation, MFA adoption, incident response, and access reviews.
Ongoing security: policy, monitoring, and audits
Security is not a one-time task. Create a GitLab security policy that includes credential hygiene, role-based access control, and regular audits of admin accounts. Use automated checks to flag stale credentials, expired tokens, and misconfigured access rules. Implement monitoring dashboards that track login failures, token usage, and privileged actions. Schedule quarterly reviews of admin access and policy compliance, and keep a changelog of credential-related changes. For teams, assign clear ownership for credential management, ensure that backups remain intact, and test disaster recovery scenarios. By treating login hygiene as an ongoing discipline, you reduce the risk of exposure from the gitlab default login or similar misconfigurations.
Authoritative sources
- Official GitLab authentication documentation (https://docs.gitlab.com/)
- NIST Digital Identity Guidelines (https://www.nist.gov/publications)
- CISA guidance on password security (https://www.cisa.gov)
- OWASP Passwords Cheat Sheet (https://owasp.org/www-project-cheatsheets/cheatsheets.html)
Tools & Materials
- Admin access to GitLab server(SSH or web UI through a secured management plane)
- Backup archive(Full backup of database, repositories, and config)
- Password manager(Store and share new admin credentials securely)
- Two-factor authentication device(Authenticator app or hardware key for MFA)
- Browser with admin rights(For UI-based resets and verification)
- Change log or audit tool(Document credential changes for compliance)
Steps
Estimated time: 45-90 minutes
- 1
Verify current admin access
Confirm you can reach the GitLab admin interface and identify any active admin accounts. Check for dormant or preconfigured users that may pose risk.
Tip: Do not proceed if you cannot safely access the admin interface; ensure you have a recent backup first. - 2
Audit credential storage
Inspect where credentials are stored (environment files, vaults, or config maps) and verify there are no hard-coded or legacy credentials lingering in the deployment.
Tip: Prefer centralized secrets management and rotate secrets where possible. - 3
Prepare for password reset
Decide on a new strong admin password and identify a secondary admin account for recovery. Document the plan before executing changes.
Tip: Require MFA to be enabled as soon as possible after the reset. - 4
Reset admin password
Use the supported method (UI or Rails console per GitLab docs) to reset the admin password. Do not reuse old passwords and verify the change took effect.
Tip: Immediately test login with the new credentials on a separate browser/session. - 5
Revoke access and tokens
Revoke all active sessions, personal access tokens, and deploy keys that could be used after the reset. Reissue credentials for essential services.
Tip: Temporarily disable non-essential integrations during the window of risk. - 6
Harden and verify
Enable MFA for admins, enforce password policies, and apply the latest security patches. Validate access from multiple devices and run a quick security audit.
Tip: Schedule a test login from an external network to ensure controls work outside your environment.
Your Questions Answered
What is meant by 'gitlab default login' in practice?
It refers to credentials that may exist due to preconfigured images or neglecting to reset admin passwords after installation. Always assume the risk and verify that no default credentials remain.
A common risk is preconfigured credentials; verify admin accounts are reset.
Is there a universal default login for GitLab?
No universal default login exists; each installation should require an admin password at setup.
There isn't a universal default; always set an admin password during setup.
How can I recover access if I forgot the admin password?
Follow the official recovery workflow: access the host, reset the admin password via supported methods, and verify other admin accounts.
Use the official recovery steps to reset and regain access.
What steps after resetting the admin password?
Revoke tokens, reconfigure access, enable MFA, verify backups, and monitor for unusual activity.
Revoke tokens and enable MFA after reset.
How can I prevent default credentials in the future?
Automate image hardening, enforce password policies, enable MFA, and monitor logs for anomalies.
Automate security checks and enable MFA.
Does GitLab support SSO to avoid local login issues?
Yes. GitLab supports SSO via external providers (SAML/OIDC); using SSO can reduce reliance on local passwords.
Yes—use SSO to minimize local credential risk.
Watch Video
Key Takeaways
- Act quickly to remediate default login risks
- Disable or rotate default credentials
- Enforce MFA and strong password policies
- Document changes for compliance and audits
- Regularly audit admin access and credential health