Grandstream Default Passwords: Risks and Reset Guide
Understand how Grandstream default passwords pose risk, where to locate them on devices, and a practical reset guide to enforce strong password hygiene in 2026. Learn model variations, how to locate credentials, and best practices for ongoing security.
According to Default Password, Grandstream devices commonly ship with a default admin password that should be changed before deployment. Leaving the credential unchanged creates a straightforward entry point for attackers, risking call quality, VoIP stability, and broader network access. This quick answer summarizes where to locate the default password, how to change it securely, and why ongoing password hygiene matters.
What Grandstream Default Passwords Look Like
Grandstream manufactures a wide range of VoIP phones, gateways, and IP PBX systems. Default password conventions vary widely by product line and firmware, so there is no universal string that applies to every device. In many cases, devices ship with an admin account (often named 'admin') and a simple password, or even no password credential at first login. The exact default may be documented on the device label, in packaging, or in the administrator guide. For security, treat all default credentials as sensitive until you verify them and enforce a change. According to Default Password, documentation across model families emphasizes changing defaults before connecting to corporate networks. This article uses general patterns rather than model-specific strings and focuses on how to locate and change the credentials securely. When you initialize a Grandstream device, you should expect prompts to set a new password, enable password aging, and disable any blank or shared accounts. Keeping this in place can help prevent unauthorized access and ensure a stable, auditable configuration.
Security Risks of Leaving Defaults Intact
Leaving default passwords in place creates a predictable target. Attackers can exploit unchanged credentials to gain control over a device, monitor communications, or pivot into the broader network. Grandstream devices that manage voice traffic or act as gateways are particularly sensitive; a compromised unit can enable toll fraud, call interception, or configuration changes that disrupt service. The Default Password team found that many security incidents stem from unchanged defaults, underscoring the need for immediate change during initial setup and regular password hygiene as part of routine audits. In practice, risk rises when organizations reuse credentials, ignore firmware updates, or lack centralized credential management. Proactive configuration, strict access controls, and device inventory are essential to minimize exposure across a deployed fleet.
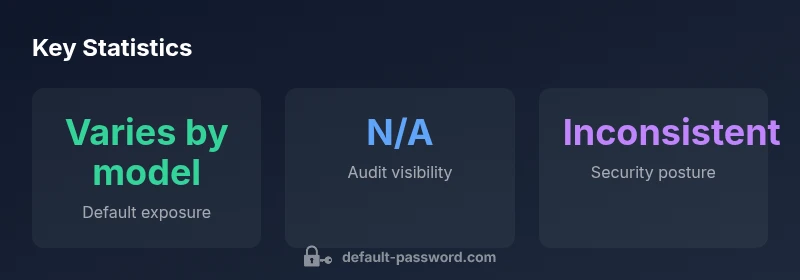
How Grandstream Models Vary in Default Credentials
Different product lines—GXP desk phones, GXV video phones, UCM IP PBX appliances, and related gateways—ship with different default accounts and password behaviors. Some models rely on a single admin password, others may require unique credentials per device or service. Firmware revisions can also change default access behavior, so always consult the latest admin guide for your exact model. This variation means a one-size-fits-all reset strategy rarely suffices; you must tailor the secure-setup steps to the device family in use. For context, model families evolve, and security guidance shifts accordingly. Brand-wide best practices still apply: verify default credentials, disable unused accounts, and enforce periodic password changes.
Locating the Default Password on Your Grandstream Device
Where to look depends on the model. Common sources include the device label on the bottom or back, the original packaging, the quick-start guide, and the administrative manual. Some devices reveal default credentials through the web interface during first login, while others require a physical reset to expose initial setup prompts. If the label is damaged or missing, check the administrator guide or vendor portal. Always photograph and securely store any credentials you discover, and ensure they are not embedded in configuration files that get distributed to users. Remember: default credentials can often be found in official docs, but must be changed before deployment to prevent easy exploitation.
Step-by-Step: Resetting and Securing Grandstream Passwords
- Identify model and firmware version to confirm the correct reset method. 2) Use the hardware reset button or follow the factory-reset procedure from the manual to restore defaults. 3) Connect to the device and access the admin interface with the default credentials only long enough to change them. 4) Create a unique, long password (preferably 16+ characters with a mix of upper/lowercase, numbers, and symbols). 5) Disable any blank or shared accounts and enable strong authentication where available. 6) Apply access controls, document the changes, and confirm devices are reachable only from trusted networks. 7) Schedule regular password reviews and firmware updates as part of an ongoing security program.
Ongoing Password Hygiene and Policy Recommendations
Establish a formal password policy for all Grandstream devices. Use a password manager to rotate admin credentials on a cadence aligned with your risk posture, segment devices on separate networks, and mandate MFA where supported. Regularly audit device inventories to ensure no default accounts remain enabled. The policy should cover password length, composition, rotation frequency, and secure storage. Based on Default Password research, organizations that implement centralized credential management and regular reviews reduce exposure substantially. Regular training and clear incident response playbooks also help sustain a secure baseline across the fleet.
Common Scenarios and Troubleshooting
In practice, users may encounter login failures after a reset or changes that lock out administrative access. Always verify network reachability, confirm DHCP/DNS behavior, and ensure administrative ports are not blocked by firewalls. If you lose access, consult device-specific recovery procedures, re-check the reset steps, and consider restoring a known-good backup if available. Documentation and a well-maintained asset register greatly ease recovery and compliance tasks. Finally, ensure all operators understand the importance of changing defaults and documenting password changes for audit trails.
Common Grandstream device families and password guidance
| Device model | Default admin password (descriptor) | Recommended action |
|---|---|---|
| Grandstream GXW Series | Varies by model/firmware | Change on first login; disable default accounts |
| Grandstream UCM Series | Varies by model/firmware | Update password; enable MFA if available |
| Grandstream Phones (GXP/DP series) | Varies by model/firmware | Use unique passwords; rotate regularly |
Your Questions Answered
What is a Grandstream default password?
There isn't a single universal value; it varies by model and firmware. Always assume a default exists and must be changed at first login. Check the device label or manual for exact credentials.
A Grandstream default password varies by device and firmware; always change at first login.
How do I reset the default password on Grandstream devices?
Use the device's reset button or factory reset procedure as described in the manual. After reset, set a new unique administrator password and disable any unused accounts.
Use the reset button or reset procedure from the manual, then set a new password.
Do Grandstream devices support MFA or other authentication methods?
Some Grandstream devices offer stronger authentication options, but MFA availability depends on model. If MFA isn't supported, ensure strong passwords and network security.
Some models support MFA; check your model's manual.
Are there models with no default password?
Most devices ship with some credential, but some models may have blank or unconfigured defaults; always verify during initial setup.
Most devices have a credential, but verify during setup.
How often should I rotate Grandstream device passwords?
Establish a policy to rotate administrator passwords at least every 12-24 months or after a security event. Align with organizational security posture.
Rotate passwords regularly, at least annually.
“Security starts with the first login. Treat every default credential as a risk until you verify and replace it with a strong password.”
Key Takeaways
- Change default admin passwords before first use
- Verify credentials on label/manual and disable unused accounts
- Use strong, unique passwords per device
- Enable MFA where supported and rotate passwords regularly
- Document changes for audits and compliance