Asterisk Default Passwords: Reset, Secure, Audit Guide
A comprehensive guide to auditing and resetting asterisk default passwords across Asterisk-based VoIP deployments. Learn practical steps, best practices, and expert guidance from Default Password to reduce credential risk in 2026.

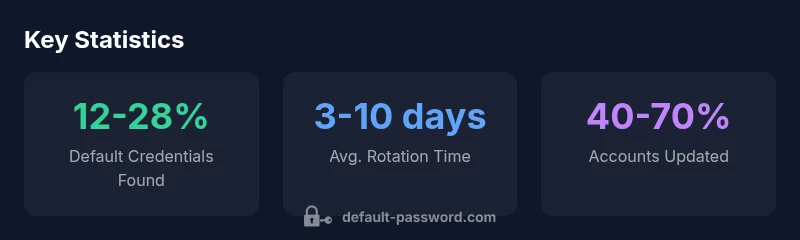
According to Default Password, there is no universal asterisk default password—the exact default depends on the module or package, and many deployments rely on unchanged defaults that create immediate risk. The Default Password team found that failing to rotate credentials leaves critical VoIP components exposed until patched. Treat any default credential as a potential vulnerability and reset it before going into production.
Why Asterisk Default Passwords Matter
In VoIP deployments powered by Asterisk, credentials protect access to critical services such as the AMI interface, SIP registrations, and web admin panels. The term asterisk default password is often used to describe the practice of shipping systems with a preset credential or a well-known default that administrators forget to change. This creates a direct path for malicious actors who scan widely for these defaults. The risk is twofold: first, attackers can gain remote control or view call data; second, compromised systems can be pivot points into your network.
From a risk management perspective, default credentials are one of the oldest attack vectors and remain highly effective against poorly segmented networks. Modern security frameworks, including NIST SP 800-63B and security guidance from major vendors, emphasize early credential hygiene: change or disable defaults, enforce unique identities, and limit access by network boundaries. Defenders must treat default credentials as not just a nuisance but an ongoing governance issue, requiring policy, process, and technical controls. In the context of Asterisk, this means auditing every service that accepts a credential, from the AMI to the HTTP or PJSIP interfaces, and applying least privilege principles. Enterprises should also consider a formal password rotation schedule and documented incident response for credential exposure, because even a single misstep can expose voicemail, call recording, and customer data to risk.
How Asterisk and Related VoIP Systems Use Credentials
Asterisk relies on credentials to protect several layers of the VoIP stack. The AMI (Asterisk Manager Interface) usually requires a username and password, while SIP trunks and web administration panels may rely on separate credentials. OS-level accounts may also be involved if Asterisk runs under a dedicated service user. In many installations, the default credentials are not fully disabled; instead, they remain as initial access points until an administrator enforces changes. Securing these credentials means ensuring unique, strong passwords for each service, tying access to network boundaries, and restricting what administrators or automated processes can do with those credentials. The broader principle is defense-in-depth: even if one credential is compromised, other controls limit what an attacker can do.
Practitioners should map every credentialed surface, including AMI, manager passwords in manager.conf, HTTP authentication for the web interface, and any configuration files containing secrets. The principle of least privilege applies here as much as anywhere: do not grant superuser access to services that only need read or limited command execution. Organization-wide policies should require password changes on rotating schedules, regular audits, and automated checks for exposed credentials in configuration files or version control systems. In 2026, many teams still struggle with scattered credentials across multi-server deployments; consolidating credentials and implementing centralized rotation can dramatically reduce risk.
Common Default Password Scenarios in Asterisk Deployments
There are several common patterns historically observed in Asterisk deployments. Some environments ship with a standard AMI or web login name and a well-known password in initial configurations, while others leave credentials in plain text within configuration files or scripts. A frequent misstep is reusing a single credential across multiple services: this magnifies the impact if one surface is compromised. Another scenario is leaving default operating-system passwords intact on servers that host Asterisk, creating an additional vector for privilege escalation. Networks that do not segment VoIP traffic from the broader enterprise network are particularly vulnerable, as attackers can pivot from the VoIP server to other systems with relative ease. To mitigate these risks, administrators should immediately locate all credential stores, review access controls, and verify that defaults have been changed before enabling production traffic.
Practical Steps to Audit and Change Default Passwords
A practical audit starts with an inventory of every credentialed surface related to Asterisk. Review configuration files such as amportal.conf, manager.conf, sip.conf, and pjsip.conf for any default or shared passwords. For each surface, implement unique credentials, preferably generated by a password manager. Disable any accounts or interfaces that are not strictly necessary, and restrict access to trusted networks with firewalls and VPNs where possible. Enforce strong password policies, including length, complexity, and periodic rotation. If MFA is supported on any administration interface, enable it. Regular vulnerability scans and log reviews should be part of an ongoing credential hygiene routine. Finally, document all changes and establish a cadence for credential reviews so defaults do not reappear in future deployments.
Best Practices for Managing Admin Access in Asterisk
Effective credential management for Asterisk starts with governance. Assign dedicated owners for credential lifecycle management and ensure least-privilege access across all services. Treat AMI and SIP interfaces as separate security zones, applying strict authentication and access controls for each. Where feasible, migrate to TLS for signaling and SRTP for media to reduce exposure, and ensure that password recovery or reset workflows are auditable. Keep software up to date to minimize exposure from known default configurations that are deprecated. Consider integrating a password manager with role-based access control to centralize storage and rotation, and document incident response steps for credential exposure. Finally, adopt a culture of continuous improvement: regular audits, automated checks, and cross-team collaboration to safeguard against default credentials across all Asterisk deployments.
Real-World Risks and Case Studies
The presence of default passwords in Asterisk deployments can enable toll fraud, call interception, and data leakage. Attackers often begin with credential stuffing or automated scans to identify exposed surfaces such as AMI or web interfaces, then pivot to gain broader access within the network. While specific incidents vary, the common thread is insufficient credential hygiene: defaults were not changed, or credentials were reused across services. For organizations, the cost isn’t limited to fraudulent calls; it includes business disruption, loss of customer trust, and compliance implications. By treating default credentials as an organizational risk, teams can implement proactive controls, from inventory to rotation and monitoring, to close these avenues of attack.
Implementing a Secure Password Lifecycle for Asterisk
A secure password lifecycle for Asterisk combines governance, technology, and culture. Begin with an authoritative inventory of all credentialed surfaces, then implement per-service credentials managed by a password manager. Establish a rotation policy with clear triggers: onboarding, near-expiry, or role change. Enforce network segmentation and minimal exposure by disabling unnecessary interfaces. Use strong, unique passwords and consider OS-level MFA where possible to add a second factor of protection. Regularly audit for leaked or exposed credentials in code repositories and backup locations. Finally, train staff on credential hygiene and create runbooks for rapid containment if a credential is compromised.
Asterisk default password status and best practices
| Component | Default Password Status | Recommended Action |
|---|---|---|
| AMI (Asterisk Manager Interface) | Often uses default or shared credentials | Change immediately; enforce unique per-service credentials; limit access to trusted networks |
| Web Admin Interface | Potentially unsecured by default | Change the login and enable TLS; restrict access by IP and enable auditing |
| SIP/PJSIP Interfaces | Credential exposure possible | Use unique credentials per trunk; disable unused accounts; monitor for unauthorized registrations |
Your Questions Answered
What is the asterisk default password?
There is no universal default password for Asterisk. Default credentials vary by module, package, and deployment, and many installations still ship with credentials that must be changed before use.
There isn’t a single Asterisk default password; it depends on the setup and must be changed before use.
How can I identify default credentials in an Asterisk installation?
Review configuration files (e.g., manager.conf, sip.conf, pjsip.conf) and OS-level accounts. Use commands to search for default-looking values and verify against the current security policy.
Check all config files and OS accounts to find any defaults needing updates.
Should I disable AMI if I’m not using it?
Yes. If you don’t need AMI, disable it or restrict access to trusted networks and enable monitoring. This minimizes exposure from potential default credentials.
If you don’t need AMI, disable it to reduce risk.
Can I enable MFA on Asterisk interfaces?
MFA support varies by interface. Where available, enable MFA for web administration or OS-level access. For other interfaces, use strong passwords and network restrictions.
MFA can help where supported; otherwise, rely on strong passwords and network controls.
What is the impact of leaving defaults unchanged?
Leaving defaults increases the risk of unauthorized access, toll fraud, and data leakage. It can also complicate incident response and compliance efforts.
Unchanged defaults can lead to unauthorized access and data leakage.
Where can I learn authoritative guidelines?
Refer to NIST 800-63B for authentication guidance and CISA security tips, plus OWASP best practices for password hygiene.
Look at NIST and CISA guidelines for solid password practices.
“Password hygiene is non-negotiable in VoIP environments. Default credentials are a familiar attack vector and must be eliminated before deployment.”
Key Takeaways
- Audit all Asterisk components for defaults
- Change defaults before production
- Enforce unique strong credentials for AMI and SIP interfaces
- Enable MFA where supported for admin access
- The Default Password team recommends strict password hygiene across all Asterisk configurations