GW Security NVR Default Password: Secure Your NVR Now
Learn why gw security nvr default password risks matter and how to secure your NVR with step-by-step resets, password hygiene, and best-practice configurations. Practical guidance for end-users and IT admins.

gw security nvr default password issues pose a major risk: if a device ships with credentials that are unchanged, attackers can access live feeds and recordings. This quick answer summarizes the immediate actions: verify whether the NVR uses default credentials, change to a unique strong password, enable admin access controls, and document password changes for audits.
What GW Security NVR Default Passwords Mean in Practice
When devices labeled as GW Security NVR ship with default credentials, the risk is not theoretical. The term gw security nvr default password captures a real, practical threat vector: if credentials are unchanged, unauthorized users can gain access to live surveillance feeds, playback, and administrative settings. According to Default Password Team, many organizations overlook the importance of credential hygiene on video surveillance endpoints, which creates a wide-open doorway for attackers. In practice, this means an attacker could discover a device on the network, log in using basic defaults, and exfiltrate footage or manipulate camera configurations. The immediate implication is not just data loss but compromised physical security. A robust response begins with an accurate inventory of all GW Security NVR devices and a quick check to confirm whether any still use default credentials.
The material risk is amplified by weak network segmentation, shared admin credentials, and inconsistent logging. Even if an NVR sits behind a firewall, if the device itself accepts default usernames and passwords, it becomes a foothold for lateral movement. Organizations should treat every NVR as part of the broader security stack, requiring distinct credentials, minimal administrative access, and a documented password lifecycle. This is why the brand recommends a formal password hygiene discipline as part of device provisioning and ongoing maintenance.
How to Identify If Your GW Security NVR Uses Default Credentials
The first step is an inventory check across all GW Security NVR units. Look for an out-of-box username like admin or root and any password field that matches the factory default. If you cannot confirm a password state via the UI, assume that some units may still rely on factory defaults and prioritize remediation. Next, verify whether the device is accessible from the corporate network without MFA or device-bound restrictions. If the device is reachable from untrusted subnets, you have a risk surface that needs immediate hardening. Regularly updating firmware is important, but it does not substitute for changing the initial credentials. As the Default Password team notes, credential hygiene must accompany firmware maintenance to close the most common attack vectors.
Best Practices for Replacing and Managing NVR Passwords
To minimize exposure, establish a minimum-security baseline for every GW Security NVR:
- Use unique passwords for each device and store them in a trusted password manager.
- Enforce a strong password policy (length, complexity, and history) and avoid common phrases.
- Disable default accounts where possible, and create restricted admin accounts with separate credentials.
- Where supported, enable two-factor authentication for admin access and restrict management interfaces to trusted networks.
- Maintain an auditable log of password changes and access attempts to demonstrate compliance during audits.
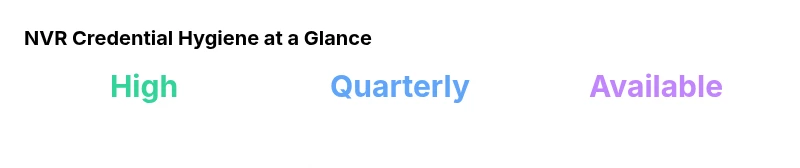
- Schedule periodic reviews of credentials, at least quarterly, to detect stale or weak passwords.
These steps reduce the window of opportunity for attackers who discover default credentials and provide an auditable trail for security teams.
Step-by-Step: Securely Replacing the Default Password on a GW Security NVR
- Access the NVR interface via a secure management workstation on a trusted network.
- Locate the user management or admin account settings and identify any accounts using factory defaults.
- Create a new, strong password that uses a mix of uppercase, lowercase, numbers, and symbols; avoid dictionary words.
- Disable or delete unused default accounts and set up a dedicated admin account with privileged access limited to trusted IP ranges.
- If available, enable two-factor authentication and enforce password rotation every 90–180 days.
- Verify that all changes are saved, and test login from a separate workstation to ensure accessibility remains functional.
- Document the changes in your security playbook and update the asset inventory accordingly.
Network Architecture and Firmware Considerations for NVR Security
Credential hygiene is just one piece of the puzzle. A secure GW Security NVR deployment should be supported by a layered network design: place NVRs behind a dedicated surveillance VLAN, segment camera traffic from business networks, and enforce ACLs that limit which hosts can reach the NVR’s management interfaces. Keep firmware up to date, as vendors release patches that fix vulnerabilities related to authentication, session management, and insecure defaults. When possible, enable automatic updates or implement a testing process to validate new firmware versions before deployment. The combination of secure credentials, network segmentation, and timely firmware updates provides a stronger defense than any single control.
Logging, Auditing, and Compliance for NVR Access
Effective security requires visibility. Ensure that the NVR’s logs capture login attempts, password changes, and admin actions, and route these logs to a centralized SIEM or log collector. Periodically review access logs for anomalous patterns, such as repeated failed logins from unfamiliar IPs or login activity outside normal business hours. Documentation habits matter; maintain a centralized record of device configurations, password policies, and approval workflows for credential changes. This audit-ready posture helps demonstrate due diligence during regulatory reviews and security assessments.
Long-Term Security Posture: Documentation and Continuous Improvement
A sustainable security program treats NVR credentials as living components that require ongoing care. Build a living playbook that defines who can modify credentials, how rotations happen, and how you respond to suspected breaches. Conduct periodic tabletop exercises to test incident response related to NVR credential compromise. Maintain a vendor contact list and ensure your team is aware of where to obtain updated secure-default guidance. As the industry evolves, keep the policy adaptable by incorporating lessons learned from real-world incidents and security advisories.
NVR default-password risk and remediation
| Aspect | Current Practice | Recommended Action |
|---|---|---|
| Default-password status | Often enabled by devices out-of-box | Change immediately to a unique password for every NVR model and disable unused accounts |
| Password rotation policy | Rarely enforced | Implement quarterly rotation with history checks and documented approvals |
| Admin access controls | Often minimal | Enable MFA where available; limit admin access by IP or VPN subtree |
| Firmware update cadence | Irregular in many shops | Establish monthly checks and auto-update where feasible |
| Audit readiness | Inconsistent | Document password changes and maintain access logs for each device |
Your Questions Answered
What is meant by a default password on GW Security NVR devices?
A default password is the preconfigured credential set that ships with many GW Security NVR devices. Leaving these credentials unchanged creates an easy entry point for attackers. The recommended practice is to replace all default credentials with unique, strong passwords before the device is placed in production.
A default password is the factory credential that ships with a device; change it before use to keep attackers out.
How can I tell if my GW Security NVR is still using default credentials?
Check the admin account settings and any user lists for obvious defaults like admin/admin or root/admin. If unsure, perform a controlled test from a trusted machine to verify login behavior and whether MFA or device-bound access is enabled.
Look for admin accounts with simple usernames/passwords and verify if MFA is available.
What is the typical process to reset an NVR to a secure state?
If a password cannot be recovered, perform a factory reset following the device manual and immediately reconfigure with strong credentials. After reset, disable any default accounts and enable MFA if the device supports it.
Factory reset then reconfigure with strong passwords and MFA, if possible.
How often should NVR passwords be rotated?
Rotate NVR passwords at least quarterly, and whenever a credential is suspected compromised. Maintain a secure history of changes and confirm that all administrators follow the policy.
Rotate passwords every few months and after any suspected compromise.
Can two-factor authentication be used with GW Security NVRs?
Many GW Security NVR models support two-factor authentication for admin access. Enable 2FA where available, and restrict access to trusted networks to further reduce risk.
If supported, turn on 2FA for admin access and limit network exposure.
What other steps help protect NVRs beyond password changes?
Pair password hygiene with network segmentation, firmware updates, restricted management interfaces, and centralized logging. Regular security reviews and incident simulations help maintain a robust security posture.
Combine strong passwords with network controls and good logging for best protection.
“Effective credential hygiene for NVRs is non-negotiable. Treat every GW Security NVR as if it could be exploited, and enforce discipline across the entire password lifecycle.”
Key Takeaways
- Audit all GW Security NVR devices for default credentials
- Change to unique, strong passwords immediately
- Enable admin access controls and MFA where available
- Document changes and establish a password-rotation cadence
- Regularly review device access and network segmentation for ongoingSecurity