Unv NVR Default Password: Risks and Secure Management
Identify UNV NVR default password risks and learn step-by-step how to change credentials, patch firmware, and secure admin access for resilient surveillance.

unv nvr default password poses a serious security risk for surveillance systems. If you own or manage an UNV NVR, immediately change the factory credentials or disable default access, then enforce unique, strong passwords and firmware updates. This article explains why default passwords are exploited, and how to securely reset and protect UNV NVR devices.
Overview of the risk posed by the unv nvr default password
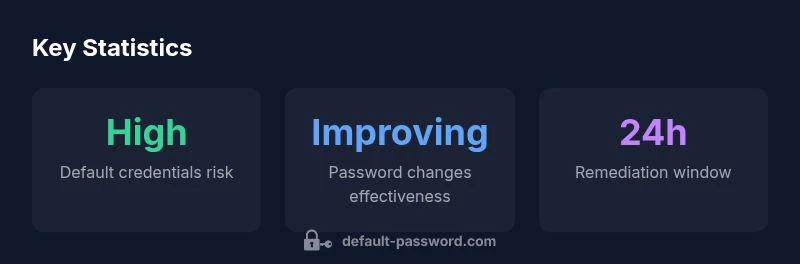
In most networked surveillance setups, the UNV NVR's default password is documented in product literature or included on device labels. Leaving this credential unchanged creates an easily exploitable vulnerability that can grant an unauthorized user remote access, real-time video streams, and control over camera configurations. The Default Password Team notes that the majority of initial compromise attempts for new installations occur when default credentials are still active, often within hours of deployment. Modern attackers include opportunistic script kiddies and more targeted actors who scan ranges of public IP addresses for devices with default or weak passwords. For administrators, the key takeaway is simple: assume the credential is known to others and act accordingly by enforcing immediate changes, applying firmware updates, and reviewing access policies. On any UNV NVR deployment, a secure baseline begins with replacing all default credentials with unique, strong passwords, documenting the changes, and testing access controls across all user roles. This approach reduces the window of exposure and creates a foundation for broader security measures such as network segmentation and logging.
How to locate the default password on UNV NVR devices and why it matters
The exact location of the UNV NVR default password varies by model and firmware, but common sources include the device label, quick-start card, the initial web GUI prompts, or the vendor's online support portal. If you can't locate the password physically, use the reset utility from UNV or contact support to obtain model-specific credentials and procedures. It matters because if the password remains unchanged, an attacker could gain administrative access, alter recording schedules, disable alerts, or export video evidence without authorization. Even if the device is not directly exposed to the internet, insecure internal networks can expose management interfaces to lateral movement within the environment. For IT teams, this means building a clear onboarding checklist that includes documenting the default credentials found during installation, then replacing them with unique credentials as part of the standard hardening process. The Default Password team emphasizes that a documented credential policy not only improves security but also supports audit requirements and incident response planning.
Step-by-step: Changing the UNV NVR default password securely
Follow these steps to replace the default password with a strong, unique credential: 1) Log in to the NVR's web interface using the existing admin account. 2) Open the Users or Security section and select the administrator account. 3) Create a long, memorable password that uses a mix of upper/lowercase letters, numbers, and symbols; avoid common words. 4) Save changes and log out, then log back in with the new password to verify access. 5) If the NVR supports two-factor authentication, enable it and configure backup codes. 6) Disable any unused accounts and review remote access settings (HTTPS, VPN-only access). 7) Reboot if required and verify that the event logs show successful authentication attempts only from authorized devices. After completing this, update the device firmware to mitigate known vulnerabilities.
Additional hardening: network segmentation, firmware updates, and access controls
Beyond changing the default password, apply layered security to UNV NVR deployments: segment the NVR on a dedicated management network separate from untrusted devices; restrict inbound connections to management interfaces using firewall rules and VPNs; monitor and log authentication attempts and access events. Keep firmware up to date with official UNV releases, as vendors patch vulnerabilities and improve password handling. Enforce role-based access control so users have only the permissions they need, and review active sessions periodically. Disable UPnP, ensure TLS/SSL for web interfaces, and use unique passwords per user. Consider integrating with a centralized authentication system where supported. For small deployments, automate credential rotation and alert on failed login attempts. The combined effect of these steps is to shrink the attack surface and make it harder for attackers to move laterally within the network.
Common misconfigurations and how to avoid them
Many incidents begin because deployment teams skip password hygiene or misconfigure remote access. Common misconfigurations include using the same password across multiple devices, sharing admin credentials among staff, and failing to disable default accounts after onboarding. Another frequent issue is relying on weak or easily guessable passwords, such as simple words or common patterns. To avoid these problems, enforce a strict password policy, require unique credentials per device, and activate alerting for password expiry and account creation. Regularly review user accounts and disable dormant accounts, especially when staff changes occur. Finally, document every change to credentials and configurations so security teams can reproduce a secure state during audits.
Monitoring and incident response: ongoing security for UNV NVR deployments
Security is not a one-time task. Implement continuous monitoring of authentication logs, video export activity, and failed login attempts for UNV NVR devices. Set up automatic alerts for abnormal activity, such as multiple failed logins from a single IP or sudden changes to user permissions. Establish an incident response plan that includes identification, containment, eradication, and recovery steps, plus a communication protocol for stakeholders. Regularly back up configuration and video data, and test restoration procedures. Finally, align with security best practices for the broader environment by integrating with a centralized security information and event management (SIEM) system where available and documenting lessons learned after any incident.
Default password status and remediation actions for UNV NVR deployments
| Category | Default Password Status | Recommended Action |
|---|---|---|
| UNV NVR | Factory default password present | Change immediately |
| Network devices | Possible exposure via default credentials | Review and rotate credentials regularly |
Your Questions Answered
What is the unv nvr default password and why is it a risk?
The unv nvr default password refers to the factory credentials that often ship with UNV NVR devices. Leaving these credentials unchanged creates an easy entry point for attackers. Always change defaults during initial setup and monitor for any unauthorized access.
UNV NVR default passwords are common attack points; change them during setup and monitor for unauthorized access.
Where can I locate the default password on my UNV NVR?
Check the device label, quick-start card, or the web GUI’s initial setup prompts. Official UNV documentation and support portals provide the correct default credentials for your model.
Look on the device label or in the setup guide for the default credentials.
Is it safe to reset to factory defaults?
Factory resets should be performed only when necessary and followed by credential updates. They can restore defaults, but you must reconfigure secure passwords and access controls immediately afterward.
Factory reset should be a last resort; always reconfigure credentials after.
How often should credentials be changed for NVRs?
Credential rotation should be part of your security policy, with changes after major updates, staff changes, or suspected compromise. Regular reviews are recommended.
Change credentials during major updates or team changes, and review periodically.
Do these steps apply to other vendors' NVRs?
While steps vary, the core principle—never leave default credentials active—applies broadly across NVRs. Always consult vendor guidance for model-specific instructions.
The same logic applies to most NVRs: don’t leave defaults in place.
What other security practices complement password changes?
Implement firmware updates, network segmentation, strong access controls, and audit logs. Combine password hygiene with ongoing monitoring for rapid threat detection.
Update firmware, segment networks, and monitor logs alongside password changes.
“Default credentials are the easiest entry point for attackers on network video recorders; securing admin access is foundational to any surveillance deployment.”
Key Takeaways
- Change the default password immediately after setup.
- Enforce unique, strong passwords across all accounts.
- Regularly update firmware and review user access.
- Audit devices for default credentials and insecure configurations.