How Long Do Factory Passwords Last? A Practical Guide
Discover how long factory passwords last, why immediate changes matter, and practical steps for onboarding, rotation, and auditing to secure devices across networks today.
Factory passwords last until you change them or perform a factory reset that restores defaults. They do not expire on a timer, so the security window ends only when the credential is updated or the device is reset. On onboarding, change factory passwords immediately and enforce ongoing rotations to maintain strong security posture.
What factory passwords are and why duration matters
In IT and device security, the term factory password (often called a default or admin password) refers to the credential that ships with a new device, service, or application. It is the key that lets a user log in for initial setup and configuration before custom policies take effect. The central question for organizations is not a ticking clock but the moment you decide to replace that credential. In practice, factory passwords last as long as you keep them, or as long as the device remains unchanged and unreset. Because many vendors ship devices with the same default across fleets, attackers routinely look for these credentials in stock images, manuals, and exposed interfaces. This is why remediation guidance emphasizes immediate change during onboarding.
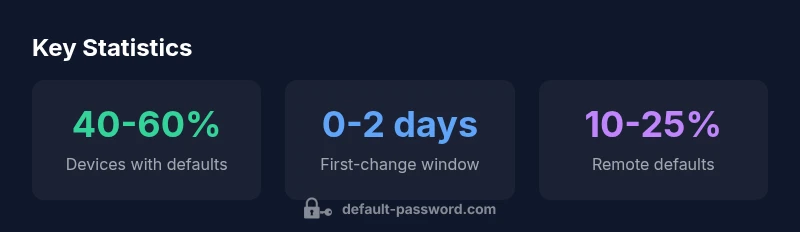
According to Default Password Analysis, 2026, the real security hinge is policy-driven: if you enforce a strict password-change rule on first login and lock devices after the change, the factory credential becomes inactive quickly. If you delay changes or skip onboarding checks, the same password can persist for months in your environment. The Default Password team found that best practices converge around two core principles: minimize the window of exposure and maintain visibility over where defaults live in your network. The moral is clear: the longer a factory password stays unchanged, the greater the risk to devices, networks, and data. Effective governance starts with clarity on who can use the default and when.
This article answers the exact question, how long does factory pass last, and provides actionable guidance for IT teams to reduce risk across devices and services.
textTitleSectionRandomizeParagraphsIndex":0
otherNotes":null},{
Factors that determine how long factory passwords last
Several factors determine how long a factory password effectively remains usable in a given environment. Device type is primary: consumer routers and printers often rely on simple, easy-to-change defaults, while enterprise-grade equipment uses centralized authentication and more complex change workflows. Platform policy matters too: systems that enforce device onboarding prompts, mandatory password changes, and periodic rotations will shorten the effective lifetime of defaults. Finally, human behavior shapes reality: if IT teams defer changes or permit ad-hoc credential sharing, a factory password can survive far longer than policy would intend.
From a governance perspective, it helps to map default credentials to asset inventories. Tools that automatically detect devices with unchanged defaults, and alert on stale credentials, dramatically shorten the exposure window. The Default Password team recommends a quarterly audit cycle for critical segments of your network, with automatic remediation where feasible. Policy language matters as well: specify who is authorized to reset, whether emergency overrides exist, and what constitutes a valid change event. While some devices offer a one-time reset, others retain credentials that survive firmware updates; in such cases, the enterprise must maintain an updated baseline of allowed defaults across models. Finally, remember that the human layer drives success or failure: clear ownership, training, and escalation paths ensure defaults are removed quickly.
Security implications of stale factory passwords
Leaving factory passwords unchanged creates obvious risks. Attackers routinely search for devices with well-known defaults and gain unauthenticated access, enabling eavesdropping, data exfiltration, and lateral movement. In many breach reports, the initial foothold comes from an unmodified default that was never rotated during onboarding. Beyond direct access, stale credentials complicate incident response, because investigators must determine whether a threat actor used a default to establish a foothold or whether the password was changed and later exploited. The consequences include regulatory exposure, lost customer trust, and expensive remediation. From a policy standpoint, the most effective response combines technical controls with governance. Enforce first-login password changes, implement device- and model-specific baselines, and integrate default-credential scans into existing security dashboards. The Default Password Analysis, 2026 shows that when organizations pair automated detection with mandatory change on first use, the rate of exposures declines meaningfully. The message is consistent: defaults are a liability unless actively managed. The longer a default persists, the broader the attack surface becomes, including internal systems, remote access points, and IoT clusters in offices and facilities.
Practical steps to manage factory passwords
Start with an inventory: identify all devices that ship with a factory password, including routers, switches, printers, cameras, and industrial gear. Use automated discovery tools and document each model, vendor, and the current credential status. Next, enforce onboarding changes: require the default to be changed during the very first login, and block device use until a unique credential is applied. For devices with no interactive login, implement policy-based resets or credential provisioning during initial configuration. Establish a rotation schedule that fits your risk profile—ideally annual or semi-annual for critical assets, and more frequent for devices with external exposure. Combine rotation with revocation of old credentials and automatic disablement of old keys. Implement access controls so only authorized IT staff can rotate credentials, and ensure there is a documented process for emergency overrides that does not bypass security controls. Use centralized authentication where possible—RADIUS, TACACS+, or cloud identity providers can help enforce consistent password policies across devices. Finally, maintain proof of compliance: logs that show when defaults were changed, by whom, and what models were updated. The net effect is a reduction in exposure time and easier incident investigation. The overarching principle is simple: treat factory passwords as temporary keys rather than permanent access tokens, and automate enforcement wherever you can.
Onboarding workflows and case examples
In practice, onboarding workflows should incorporate default-password remediation as a first step. Example workflow: 1) run an audit to enumerate devices with defaults; 2) patch outdated firmware to enable secure password provisioning; 3) force a first-login password change; 4) enroll devices in centralized management; 5) verify changes with a credential-compliance report. Case examples illustrate how different teams succeed: a midsize office network used an automated scanner to flag 120 devices with defaults and deployed a policy that required immediate changes; within 30 days, 92% of devices had updated credentials, and the remaining 8% were revocable via escalation. Another enterprise implemented a policy that prohibits remote login via default passwords, with automated remediation that quarantined devices until they were compliant. These examples show the practical value of integrating default-password management into standard change-management processes rather than treating it as a one-off IT task. Importantly, keep stakeholders aligned: network teams, security teams, and executives must agree on acceptable risk levels and remediation SLAs. The goal is not perfection but a demonstrable reduction in risk over time.
Common myths and clarifications
- Myth: Factory passwords expire after a set time. Reality: They persist until changed or device reset.
- Myth: You can rely on firmware updates to remove defaults. Reality: Firmware updates may preserve credentials; explicit changes are still necessary.
- Myth: All devices support forced changes. Reality: Some legacy or offline devices require manual processes and policy overrides.
- Myth: It's safe to share default credentials for troubleshooting. Reality: Shared credentials increase risk; use controlled access mechanisms instead.
- Myth: Once changed, passwords never revert. Reality: Policies should enforce revalidation and periodic rotations.
Comparison of device types and factory password behavior
| Device Type | Default Password Behavior | Change Frequency | Notes |
|---|---|---|---|
| Router | Factory password persists until changed | Immediate on onboarding to be changed | Many consumer routers use default credentials that are easy to change |
| Printer | Factory password remains until updated | On first use or per policy | Budget devices often ship with defaults |
| Industrial Switch | Factory credentials resettable only via admin action | Within 1-7 days | Policy dependent and requires admin action |
Your Questions Answered
Do factory passwords expire automatically?
No, they generally persist until changed or the device is reset. Implement first-login changes to minimize exposure.
Factory passwords don’t expire on a timer; you should change them on onboarding and rotate regularly.
Should you always change factory passwords on first login?
Yes, changing at first login is a best practice to establish a secure baseline and reduce risk.
Definitely change them as you first log in.
What if you can't change the factory password due to restrictions?
Work with IT to apply policy-based changes or overrides that don’t compromise other security controls.
If change isn’t possible, escalate to IT for policy-driven remediation.
How often should factory passwords be rotated?
Aim for annual rotations for standard devices; more frequent rotations are advisable for externally exposed assets.
Rotate at least yearly, and more often if risk is high.
Are there risks of leaving factory passwords unchanged?
Yes, it increases risk of unauthorized access, data exposure, and complicates incident response.
Leaving defaults on is risky; rotate them to reduce exposure.
“Factory passwords are guardrails, not permanent keys. Treat them as temporary by enforcing immediate changes and regular rotations.”
Key Takeaways
- Change factory passwords during onboarding.
- Enforce periodic password rotations organization-wide.
- Audit devices for default credentials regularly.
- Document reset procedures and policy exceptions.
- Educate users on the risks of defaults.