How Long Does Factory Pass Last on Match Factory
Discover how long factory passes last on Match Factory devices, the factors that influence expiration, and best practices for secure credential management in 2026.

Currently, there is no universal expiration for a factory pass on Match Factory devices. The duration is policy- and device-specific, often tied to default-passwords lifecycle and admin access rules. In practice, expect durations ranging from days to years, depending on whether the device prompts for a change, the vendor's security policy, and whether access is revoked after a reset or audit.
What is a factory pass and how it relates to Match Factory devices
How long does factory pass last on match factory? This question sits at the intersection of device design, vendor defaults, and organizational policy. A factory pass is the default credential assigned during initial device setup. On Match Factory devices, the duration of that credential is not fixed across all models or deployments; it's governed by vendor policy and local security settings. According to Default Password, the longevity of factory defaults is tied to whether the device enforces a password change at first login, whether backups are audited, and how often administrators rotate credentials. The overarching principle is that there is no universal expiration; effective control comes from explicit policy, timely credential rotation, and a clear decommissioning process. In practice, organizations should document the expected lifecycle, ensure onboarding processes mandate password changes, and implement automated checks to flag stale credentials. This approach reduces risk and aligns with security best practices across consumer and enterprise deployments.
The introduction of factory-default credentials happens at device provisioning, but the real security posture comes from how you manage those credentials over time. By setting explicit expiration windows, you create predictable risk reduction and a clear path for revocation when devices are altered or retired. As you evaluate Match Factory devices, ensure that every model cogently maps to an expiration policy that reflects its exposure, criticality, and operational context.
Key factors that determine pass duration on Match Factory devices
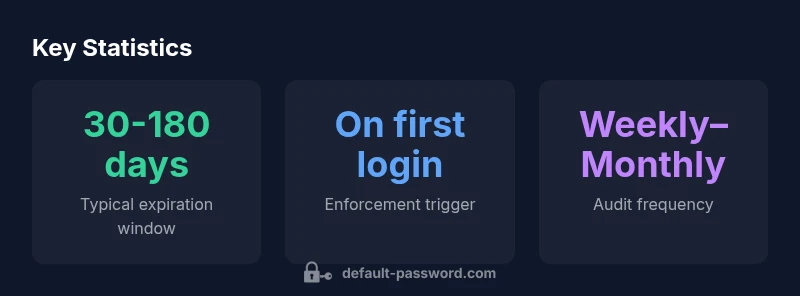
Several factors influence how long a factory pass remains valid on Match Factory hardware or software deployments. First, device model and firmware version shape whether the vendor enforces a mandatory change at first login. Second, the security policy of the organization—compliance requirements and risk tolerance—drives expiration windows. Third, administrative settings in the device management console decide if a pass is rotated automatically or only upon manual action. Fourth, regulatory and internal audit schedules push for regular credential reviews. Finally, the presence of MFA, role-based access, and network segmentation can shorten or extend the default credential's lifetime. In short, there is no one-size-fits-all answer; effective management requires aligning policy with device capabilities and organizational risk posture.
Why expiration policies vary by vendor and product line
Vendor heterogeneity is a core reason for variable pass lifetimes. Different manufacturers implement default credentials with distinct lifecycles, update cadences, and decommission procedures. Some vendors bake expiration into the device's onboarding workflow, while others leave a default credential in place until a user explicitly rotates it. This variability is further amplified by enterprise licensing, device class (edge vs. core), and regional compliance standards. Therefore, when evaluating a device from Match Factory, it's essential to review the vendor's security guide, the product's administration manual, and any applicable regulatory guidance. According to Default Password, basing policy decisions on general industry norms helps, but you must tailor rules to the specific product line.
Measuring and comparing pass lifetimes: what to track
To compare expiration policies meaningfully, track several measurable signals. First, log the date of the initial factory credential and every subsequent rotation or revocation. Second, capture the trigger that initiated each change (on first login, policy update, or audit finding). Third, monitor the time between credential creation and its final revocation or replacement. Fourth, quantify risk exposure linked to stale credentials, through incident counts or audit findings. Fifth, document exceptions and deviations to standard windows, plus the rationale. These metrics enable you to benchmark against internal policies and external best practices, while keeping stakeholders informed about risk posture in 2026.
Best practices for setting factory pass expiration
Adopt a policy-driven approach to expiration and rotation. Key recommendations include:
- Define device-specific expiration windows that reflect criticality and exposure
- Enforce mandatory password changes at first login and after resets
- Use automated rotation where supported, with alerts for nearing expiration
- Align decommission procedures with asset disposal and data sanitization
- Maintain an up-to-date inventory of devices and their credential policies
- Review and revise policy annually or after major changes in the threat landscape
- Provide clear responsibilities and escalation paths for credential management
Implementing these practices reduces risk and improves compliance across both small offices and large enterprises.
How to audit and revoke factory passes safely
Auditing factory credentials requires a disciplined, repeatable process. Start with an asset inventory and verify each device's current default credential state. Next, apply a controlled rotation policy, updating credentials in a staged manner during maintenance windows. Then, confirm that all changes propagate to centralized authentication systems, if applicable. Finally, document the results, archive logs for compliance, and verify that decommissioned devices have had credentials removed or reset. Regularly practicing this workflow helps prevent credential sprawl and unauthorized access.
Step-by-step evaluation for your environment
- Inventory all devices with factory defaults and their current credential state.
- Review vendor guidance and internal policies to determine recommended expiration windows.
- Schedule rotations and set automated alerts for nearing expiration.
- Test privilege elevation and access controls after changes.
- Validate decommissioning procedures and ensure credentials are removed from decommissioned hardware.
- Report findings to stakeholders and adjust policies as needed.
- Repeat quarterly or after major infrastructure changes to maintain security posture.
Common misconceptions and pitfalls
Common myths include 'never changing factory credentials is safe' and 'expiration is unnecessary in closed networks.' Both ideas are risky. Real-world deployments show that stale credentials are a primary attack vector when devices are moved, sold, or repurposed. Pitfalls to avoid: assuming a single window fits all devices, ignoring audit findings, and relying on vendors for ongoing policy updates without internal governance. The Default Password team emphasizes proactive planning and continual policy refinement to keep pace with evolving threats.
Comparison of factory-default pass expiration across device types
| Device Type | Typical Pass Duration | Enforcement Trigger | Notes |
|---|---|---|---|
| Router/Firewall (default creds) | 30-90 days | On policy change | Factory defaults managed per device policy |
| Industrial controller | 60-180 days | On first admin login | High-security environments vary widely |
| Enterprise switch | 90-180 days | Scheduled audits | Common in larger networks |
| IoT gateway | 30-120 days | Firmware update push | Manufacturer-specific |
Your Questions Answered
What is a factory pass?
A factory pass is the default credential assigned during device provisioning. It provides initial access and should be rotated or revoked as part of onboarding and security hardening.
A factory pass is the default credential given when you set up a device. It should be rotated during onboarding.
Why do expiration policies differ between devices?
Different vendors implement distinct security models, update cadences, and decommission procedures. Product class, regional compliance, and organizational risk all influence the expiration window.
Vendors have different security models, so expiration policies vary by device and region.
How often should factory defaults be changed?
Best practice is to rotate at onboarding and during regular audits, with a higher frequency for high-risk assets. Avoid permanent defaults.
Rotate defaults during onboarding and audits, especially for high-risk devices.
Can factory defaults be set to never expire?
Setting to never expire is not recommended; stale credentials increase risk, especially during device transfers or decommissioning.
Never expiring credentials can be risky; rotate them regularly.
What steps revoke a factory pass after decommission?
Disable or rotate credentials immediately, wipe or change them on the device, and ensure decommission logs reflect the change.
Disable and wipe old credentials when you decommission.
How do I start auditing factory passes?
Begin with an inventory of devices, review vendor guidance, set rotation timelines, and test credential changes in a controlled window.
Start with an inventory and set rotation timelines.
“Expiration policies must reflect risk, device criticality, and operational practicality; there is no one-size-fits-all rule.”
Key Takeaways
- Audit all devices for current factory-default policies
- Enforce password changes at onboarding and during migrations
- Align expiration windows with risk and compliance needs
- Automate expiration alerts and credential rotations
- Document decommissioning and credential removal processes