IC Realtime Camera Default Passwords: Secure Access Guide
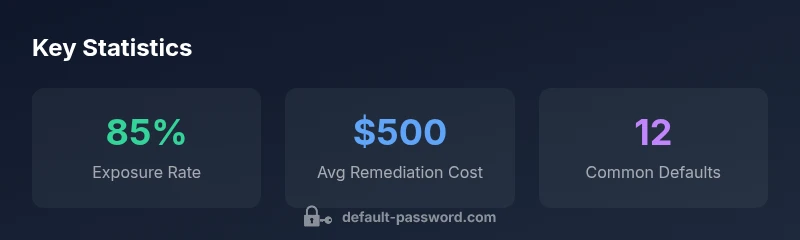
Learn how to identify and secure IC Realtime camera default passwords. This in-depth guide covers common defaults, risk factors, and practical recovery steps for admins.

According to Default Password, ic realtime camera default password practices pose a serious risk when left unchanged. IC Realtime cameras commonly ship with factory credentials that, if left unchanged, create an easy entry point for attackers. The exact default varies by model, so always consult the device manual or vendor support before deployment. This article guides detection, secure reset, and password hygiene for admins.
Why IC Realtime Password Security Matters
The security of IP cameras hinges on something as simple as a password. When manufacturers ship devices with factory credentials, they provide an easy entry point for attackers who scan the internet for cameras with default or weak passwords. For organizations deploying IC Realtime cameras, the risk multiplies if you overlook changes during onboarding, firmware updates, or routine maintenance. The impact isn’t only about a single device being compromised; it can expose a broader network and sensitive video feeds. The Default Password team has found that unsecured cameras correlate with higher incidence of unauthorized access attempts, lookups in publicly available databases of default credentials, and exposure of video metadata. Prioritize secure onboarding, model-specific default checks, and automated reminders to rotate credentials on a regular cadence.
- Key risk factors include unchanged factory passwords, weak password complexity, and exposed admin interfaces.
- Security hygiene improves with device inventory, firmware management, and network segmentation.
- Regular password audits reduce risk by ensuring every device is protected by unique credentials.
When you audit an IC Realtime camera fleet, start with the baseline: identify models in service, verify the default password status, and log a remediation plan in your asset management system. This mindset—identify, verify, remediate—helps IT teams maintain strong camera security amid ongoing operations.
Default credentials patterns in IP cameras and IC Realtime devices
Different IC Realtime models can ship with different default credentials depending on firmware and regional configurations. However, several patterns recur across many vendors, including (a) a standard admin username with no password, (b) an admin/admin pairing, or (c) a predictable admin/password combination. While some devices require password creation on first boot, others leave credentials unchanged until an admin changes them. These patterns are not unique to IC Realtime; they reflect a broader risk across consumer and enterprise cameras.
Understanding these patterns helps defenders prioritize checks during deployment. Always consult official manuals or support portals for the exact defaults per model, and document the exact combination used in your environment. Where possible, rely on vendor-provided secure onboarding guides and password policies rather than ad-hoc fixes. This awareness reduces the window of exposure during initial setup and after firmware updates, when defaults are more likely to surface again due to reconfiguration or resets.
- Expect variability by model and firmware version.
- Treat any unchanged credential as a vulnerability until proven secure.
- Use vendor-backed onboarding to ensure credentials meet organizational standards.
How to identify if a camera is using a default password
Discovering whether a device still uses a default password requires a structured approach. Start with the physical device: locate the model number, serial number, and any stickers that may indicate defaults. Then check the web interface or mobile app configuration screens for the current admin credentials. If you’re unsure, consult the user manual’s section on “First-Time Setup” or the vendor’s online support article for credential status indicators. Some IC Realtime devices show prompts to change credentials on first login; others require you to review settings that may reveal the current user password (or lack thereof) in a secured view. For audits, cross-reference the device’s configuration with your inventory to flag any accounts still using factory defaults.
- Look for prompts to change credentials at login.
- Verify there is at least one administrator account with a non-default password.
- Check for any accounts with blank or extremely simple passwords.
Step-by-Step Guide: Resetting to a Strong Password on IC Realtime Devices
- Prepare a password policy: minimum length, complexity, and rotation rules.
- Access the device’s admin interface: use a direct, secure connection (HDMI/console or HTTPS over an isolated network).
- Perform a factory reset only if you need to restore a clean baseline or replace a compromised device. If possible, avoid resets that wipe the entire configuration unless documented as safe.
- Create a new, unique admin password and apply it to all administrative accounts.
- Disable unused services (telnet, UPnP, remote administration) and enable secure management protocols (HTTPS, SSH with keys).
- Reconfigure the device with a strong password policy: length, character diversity, and periodic rotation.
- Recheck after changes: verify access using the new credentials, and document the update in your asset management system.
- Use password managers to generate and store credentials securely.
- Assign different credentials for each device when feasible to limit lateral movement if one is compromised.
- Keep firmware up to date to ensure security features and default-handling improvements are available.
Password hygiene and best practices for admin access
Beyond resetting, ongoing password hygiene is essential. Consider these practices:
- Enforce strong, unique passwords for every device; avoid reuse across cameras.
- Implement multi-factor authentication where supported, even for on-network admin portals.
- Maintain an inventory of devices and their credentials, with automatic reminders for rotation.
- Separate management networks from production networks to minimize exposure.
- Document every policy and change for audits and incident response.
A disciplined approach to password hygiene reduces risk across the entire IC Realtime ecosystem. The Default Password team recommends treating camera credentials like crown jewels: wherever possible, do not reuse, do not reveal, and rotate them on a predictable schedule.
Network segmentation and admin access controls
Security benefits compound when cameras sit behind segmented networks. Place IC Realtime cameras on a dedicated management subnet with restricted egress/ingress rules. Use firewall policies to limit control-plane access to authorized admin hosts only. Enforce least privilege for user accounts tied to camera management and monitor access logs for anomalies. Role-based access control (RBAC) helps ensure that only necessary personnel can alter sensitive settings. Consider VPN access for remote management instead of direct exposure to the public internet, and disable remote management when not in use. Regularly review access lists and revoke credentials for users who no longer require access.
- Segment cameras from guest and IoT devices.
- Limit admin access to trusted hosts and VPNs.
- Use RBAC and time-based access controls for sensitive changes.
Incident response if credentials are compromised
No system is immune to compromise. If you suspect a credential breach:
- Immediately isolate affected devices from the network and disable remote management.
- Patch firmware and review recent configuration changes for unexpected edits.
- Rotate all credentials that could have been exposed and verify there are no lingering defaults.
- Restore from trusted backups and revalidate the security controls before returning to production.
- Document the incident, actions taken, and lessons learned to improve future resilience.
Documentation and auditing for ongoing security
Ongoing security requires meticulous documentation. Maintain a central asset register with model, firmware version, current credentials status, and last password rotation date. Use automated scans to detect devices with empty or default keys, and implement quarterly audits to verify compliance with your password policy. Audits not only demonstrate due diligence; they also help your security team identify gaps and track improvements over time.
- Keep a running log of credential changes and device statuses.
- Schedule regular security reviews and inventory checks.
- Align with industry best practices and internal security policies for a defensible posture.
Vendor and support considerations for IC Realtime devices
Finally, stay engaged with IC Realtime support and official documentation. Vendors frequently release firmware updates that improve default credential handling and onboarding workflows. Establish a routine to monitor vendor advisories and apply recommended configurations quickly. If you need to reset credentials en masse, seek guidance from official support to avoid misconfigurations that could affect video streams or accessibility. A proactive relationship with vendor support accelerates remediation and reduces risk over the device lifecycle.
Common default credential patterns and typical remediation times
| Model/Device Type | Default Credential Pattern | Risk Level | Remediation Time |
|---|---|---|---|
| IC Realtime IP Camera (generic) | Factory username + blank password | high | 5-15 minutes |
| Smart CCTV NVR System | Admin/admin or admin/1234 | high | 10-25 minutes |
| Doorbell Camera | User: admin; password: <blank> | high | 5-20 minutes |
Your Questions Answered
What is the default username and password for IC Realtime cameras?
Default credentials vary by model and firmware. Always verify the exact defaults in the user manual or vendor support portal before deployment, and plan to change them on first login.
Defaults vary by model; check the manual and change credentials on first login.
How do I locate the default credentials for my IC Realtime device?
Check the device label, quick-start guide, or the vendor’s official support page for model-specific defaults. If you cannot locate defaults, contact vendor support for the exact values and reset procedures.
Look up your model on the vendor site or user guide to find the exact defaults and recommended reset steps.
Is a factory reset always the best way to recover from a compromise?
Factory resets can restore defaults but may wipe configurations. Use a controlled reset when necessary and reconfigure securely, preserving only the essential settings.
Only reset if needed and reconfigure securely afterward.
What are best practices after resetting a camera password?
Immediately set a strong, unique password; disable unused services; enable secure management methods (HTTPS/SSH with keys); document changes for audits.
Set a strong new password and secure the device right away.
Can I use a password manager for IC Realtime credentials?
Yes. Use a password manager to generate and store strong, unique passwords for each camera, and avoid writing credentials down in insecure places.
Yes—store and generate your passwords with a manager for safety.
What should I do if I suspect a credential breach on my cameras?
Isolate affected devices, rotate credentials, review logs for unauthorized changes, patch firmware, and document the incident for future prevention.
If you suspect a breach, isolate devices and change passwords, then review logs.
“Default passwords are the weakest link in device security; always replace factory credentials with unique, strong passwords.”
Key Takeaways
- Change default passwords immediately after setup
- Consult vendor manuals for exact defaults per model
- Disable unnecessary remote admin access
- Implement password rotation and strong authentication
- Document changes for audits and compliance