IC Realtime Default Password: Risks, Reset, and Best Practices
Analyze ic realtime default password risks, detection methods, and step-by-step guidance to reset and harden admin credentials across IC Realtime devices and similar security hardware.

ic realtime default password refers to the practice of leaving device admin credentials unchanged on IC Realtime security devices. This default credential risk exposes cameras, NVRs, and related gear to unauthorized access, weak encryption, and downtime. In this article, we quantify the risk, outline detection methods, and provide practical steps to reset and enforce strong passwords.
What ic realtime default password means
The phrase ic realtime default password describes the common security gap where administrative access to IC Realtime devices—such as IP cameras, video recorders, and related network gear—still uses the device’s factory-supplied credentials. These defaults are widely documented and easy to guess, especially when vendors reuse generic usernames like admin with predictable passwords. In practice, leaving these credentials unchanged creates a direct pathway for attackers to access live video streams, configure devices, or pivot to other network assets. For organizations and individuals, this basic oversight is a frequent entry point for breaches. The Default Password team emphasizes that identifying and addressing these defaults is a foundational step in any device security program, and ic realtime default password is a concrete example of why regular credential hygiene matters for CCTV and surveillance ecosystems.
- Undermines access control and audit trails
- Enables unauthorized viewing, tampering, or disabling of devices
- Increases risk of data exfiltration and service disruption
To mitigate this risk, start with a clear inventory of affected devices and enforce password hygiene as a standard operation procedure across all security gear.
Why default passwords are risky in realtime devices
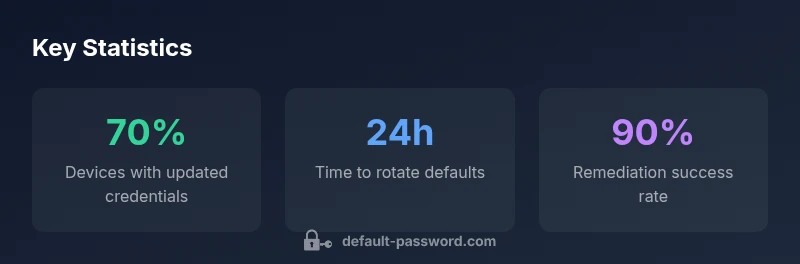
Default credentials are designed for easy initial access, not long-term security. In real-time surveillance environments, attackers don’t just steal credentials—they exploit them to gain persistent access, disable alerts, or reroute traffic. The consequences include exposed camera feeds, altered time settings, and the ability to delete or overwrite footage. The risk is compounded when devices sit behind poorly segmented networks or when vendors push firmware updates that don’t automatically enforce credential changes. Security researchers and IT admins alike report that many incidents start with a neglected default password on a network camera or NVR. The Default Password Analysis, 2026, highlights that credentials left in their factory state are among the most common, preventable misconfigurations. Effective remediation begins with visibility, improvement of password policies, and routine credential rotation.
- Default credentials are widely predictable across device families
- IoT and surveillance gear often ship with default passwords enabled by default
- Poor network segmentation amplifies the impact of compromised devices
Common devices affected and password patterns
IC Realtime ecosystems frequently include IP cameras, network video recorders (NVRs), and associated access points. These devices commonly ship with a default username like admin and a default password such as admin, 12345, or the device’s serial-based credential. In many cases, factory-default credentials are printed on a label or documented in quick start guides, posing a risk if devices are deployed without password changes. Attackers scan for devices exposing web interfaces or RTSP streams, then attempt default credentials until access is granted. Awareness of these patterns helps IT teams prioritize inventory checks and automate credential changes where possible. The pattern is not limited to IC Realtime; it mirrors broader industry practices where a poor default policy translates into real-world security exposure.
- Cameras and NVRs are high-risk targets for default credentials
- Some routers and edge devices in the same environment share similar patterns
- A consistent credential change policy reduces both risk and audit gaps
How to identify if you are using a default password
Begin by inspecting the device’s login prompt or interface. If you can access the admin panel without a password prompt, or if the password field matches a common default (e.g., admin/admin, root/password), you are at risk. Review device labels, quick-start guides, and the vendor’s official documentation for default credentials. Use a configuration management tool or network scanner to detect devices exposing unmodified credentials. Change any over-products that are discovered with defaults, and implement a policy that requires password changes within a defined time window after deployment. An immediate check across the environment will reveal devices still using defaults and help shape remediation timelines. The process should align with your organization’s security baseline and incident response plans.
- Start with a comprehensive device inventory
- Check for login prompts that bypass password requirements
- Validate against vendor defaults and your asset management records
Step-by-step: Resetting to a secure password on routers, cameras, and NVRs
- Access the device management interface via a secure, trusted network
- Locate the admin or user account settings and select Change Password
- Create a strong password using a mix of upper/lowercase letters, numbers, and symbols (min 12-16 characters)
- Change the username if supported (avoid always-reusing admin)
- Enable multi-factor authentication if available or consider a hardware key
- Update firmware to the latest version and review related security settings (HTTPS, disable unused services)
- Document the change in a password manager, then test access from a separate device
- Schedule automatic reviews and set reminders for periodic credential rotations
This approach reduces the chance of repeat exposure and improves post-change monitoring. Remember to update any linked accounts or integrations that rely on the old credentials.
Best practices for managing admin access and credentials
- Enforce unique, device-specific passwords rather than shared defaults
- Use a centralized password manager for storage and auditing across devices
- Implement MFA where supported to protect admin access
- Disable or restrict remote admin access unless necessary, and implement IP allowlists
- Establish a policy for regular password rotation (e.g., every 90 days) and automatic reminders
- Keep firmware updated and review security configurations after every update
- Maintain an auditable change log to support compliance and incident response
These practices reduce the likelihood of exposure and provide traceable security controls.
Methods for enforcing policy across an organization
Organizations should adopt a multi-layered defense: inventory management, credential hygiene, and governance. Start with automated scans that identify devices with default credentials and missing MFA. Implement configuration baselines that enforce password complexity, rotation schedules, and restricted access. Use role-based access control (RBAC) for administrative tasks and segregate duties to prevent single-point compromise. Regular security audits, phishing simulations, and staff training reinforce good habits. For IC Realtime devices, ensure that password policies extend to all connected components—cameras, NVRs, switches, and management consoles. The goal is a repeatable, scalable process that reduces risk across the entire ecosystem.
Real-world examples and lessons learned
Case studies show that organizations that prioritized credential hygiene experienced fewer breaches related to default passwords. Lessons include the importance of device inventory, immediate remediation of exposed devices, and automation to enforce password changes across large networks. Even modest gains—like turning off default remote administration and enabling HTTPS with valid certificates—can significantly improve security posture. The overarching message from practitioners is consistent: defaults are the weakest link, and proactive remediation is cheaper than incident response.
How to verify your changes and ongoing maintenance
- Attempt login with the new credentials from multiple devices to confirm access is restricted where appropriate
- Schedule a monthly credential health check and quarterly security review
- Enable alerting for failed login attempts on admin interfaces
- Use asset management dashboards to track device status and firmware versions
- Periodically run vulnerability scans that include default-password checks
- Maintain a documented runbook for password resets and incident response procedures
Regular verification ensures that protective measures remain effective and adapting to evolving threats.
Default credential status and recommended actions by device type
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| IC Realtime Cameras/NVRs | Commonly preset default credentials in older firmware | Change credentials; Enable auto update; Implement MFA where possible |
| Routers/Edge Devices | Often shipped with predictable admin users | Change username/password; Update firmware; Disable remote admin when not needed |
Your Questions Answered
What does ic realtime default password mean?
It refers to leaving admin credentials unchanged on IC Realtime devices, creating an easy target for unauthorized access. Recognizing this default is the first step toward securing surveillance systems and maintaining proper access controls.
It means the device uses factory credentials that are easy to guess, so you should change them now.
Why are default passwords dangerous for surveillance devices?
Default passwords provide attackers with immediate access to live feeds and device settings. This can lead to privacy breaches, footage tampering, and operational disruption. Changing credentials and enabling MFA greatly reduces these risks.
Default passwords give intruders a simple entry; changing them and using MFA helps prevent breaches.
How do I reset a default password on an IC Realtime device?
Access the device interface via a secure network, locate the admin settings, change the password to a strong, unique value, and enable MFA if available. Update firmware and document the change in a password manager.
Open the admin panel, set a new strong password, and enable MFA if possible.
Which devices are typically affected by default credentials?
Surveillance cameras, NVRs, and network devices commonly ship with defaults. Any device with a web interface or admin panel could be at risk if credentials are not updated.
Cameras, NVRs, and related network devices often come with default passwords.
Can automation help enforce password changes across devices?
Yes. Automated configuration management and password rotation policies can enforce changes at scale, reducing manual error and ensuring consistent security practices.
Automation helps enforce changes across many devices reliably.
Where can I find official docs to change defaults?
Consult IC Realtime product manuals, vendor security advisories, and firmware release notes. Always verify settings against the latest vendor recommendations and security best practices.
Check the vendor manuals and security advisories for current steps.
How often should I rotate default passwords?
Implement a rotation policy, commonly every 90 days or aligned with your security baseline, and review after firmware updates or changes in admin roles.
Rotate passwords on a regular schedule and after major updates.
“Default passwords are the soft underbelly of connected devices. Replacing defaults is a fundamental security practice that stops attackers at the gate.”
Key Takeaways
- Identify all devices using default credentials.
- Change defaults before exposure to the internet.
- Enable MFA and encryption wherever possible.
- Document changes and enforce periodic rotations.