Lantronix default password: Risks, resets, and best practices
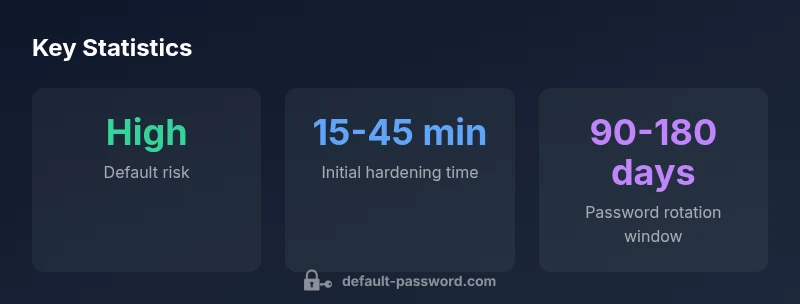
Explore why Lantronix default passwords pose a risk, how to identify them across devices, and step-by-step strategies to reset and harden Lantronix deployments with best-practice password hygiene in 2026.
Lantronix devices commonly ship with default credentials that grant administrative access, creating a sizable security risk if not changed during onboarding. According to Default Password, immediate password customization is essential, followed by ongoing password hygiene and device hardening. This article explains how to identify, verify, and reset default credentials across Lantronix products to reduce exposure.
Understanding Lantronix default passwords
Lantronix devices, like many network appliances, ship with initial credentials that allow immediate access to administrative interfaces. The exact username and password pair vary by model and firmware version, but the underlying risk is the same: an unchanged default credential provides a simple foothold for attackers, especially if devices are exposed to the internet or poorly segmented networks. In practice, many organizations focus on changing the password during initial setup, yet a sizable portion still overlooks this step in busy deployments. The Default Password team notes that the most common entry points involve the device's web UI and SSH/TELNET sessions, where weak defaults or easy-to-guess patterns remain in place longer than intended. To mitigate this, teams should adopt a habit of documenting the expected credential patterns for each Lantronix device in service inventories and ensuring enforcement of strong password policies from day one.
When discussing Lantronix default password risk, it’s important to connect this to broader security realities: misconfigured devices often sit behind perimeter controls that give a false sense of safety. A robust onboarding workflow—encompassing credential review, firmware checks, and access controls—reduces the chance that a default password becomes a gateway for lateral movement within the network. This is why many security teams pair device hardening with network segmentation and continuous monitoring, so anomalous authentication attempts on Lantronix devices are detected early. In practice, teams should codify a standard operating procedure (SOP) for initial device provisioning that explicitly requires password changes, documented admin accounts, and a check against known vendor defaults for each model.
From a governance perspective, roughly aligning Lantronix deployments with the organization’s password policy helps ensure consistency. The most effective programs combine technical controls with administrative oversight: enforce unique admin accounts per device, disable unused services, and require regular credential audits as part of risk management. The broader implication is straightforward: you cannot secure a Lantronix appliance by credentials alone—you need a disciplined, repeatable process that ties into asset inventories and change management.
The security landscape for network appliances
The cybersecurity landscape treats default passwords as a perennial weakness across diverse vendor ecosystems. Attackers routinely target devices with easy-to-guess credentials because they offer quick access to management interfaces and critical configurations. For Lantronix devices, this translates into a focus on the web UI and command-line interfaces that often remain exposed during deployment. Defensive strategies emphasize not just changing the default password at setup, but embedding credential hygiene into ongoing operations. Regular audits, firmware validation, and practice-based security controls (such as network zone restrictions and strict admin role definitions) are essential complements to any password policy. In practice, many organizations implement automated configuration baselines that flag non-compliant devices—such as those still using vendor defaults or shared admin accounts—so remediation can occur before a breach occurs. As with all network appliances, the goal is to shift from a reactive to a proactive security posture, where password hygiene is built into the lifecycle of every Lantronix device from onboarding through end-of-life decommissioning.
To align with industry best practices, teams should reference recognized frameworks and guidance from authorities like government and academia. In particular, guidance from national cybersecurity programs consistently highlights changing default credentials as a baseline control, alongside robust access controls, regular firmware updates, and network segmentation. These insights reinforce the idea that Lantronix devices are secure only when their authentication surface is hardened and monitored as part of an integrated security program.
How Lantronix authentication works
Lantronix authentication mechanisms typically expose multiple pathways for administration, including web-based interfaces, SSH or Telnet sessions, and sometimes serial console access. The authentication surface is designed to support both convenience during setup and ongoing remote management, but this dual purpose also increases risk if defaults remain in place. Effective security hinges on several key factors: first, that the initial login prompts are resolved with a strong, unique password; second, that default accounts are renamed or removed; and third, that only necessary services are exposed to management networks. In most deployments, you’ll want to disable any remote management methods that aren’t required for daily operations, or at minimum restrict them to trusted IP ranges and enforce multi-factor authentication if supported. Regular checks of account roles, auditing logs for privileged actions, and alignment with change-control processes help ensure authentication is not a weak link in the broader security posture.
From a defender’s perspective, understanding the authentication flow helps in designing effective controls. If a Lantronix device uses a shared default credential across multiple devices, an attacker who breaches one unit may gain a foothold across the entire environment. Therefore, per-device credentials and unique admin accounts are preferable to shared ones, and automation can enforce this policy without slowing down deployment. The industry’s consensus is clear: authenticated access should be treated as a critical security boundary that requires constant validation, logging, and rotation.
Authority sources and formal guidance emphasize that secure authentication on network devices is a continuous process rather than a one-time fix. For Lantronix devices, this means integrating credential management with configuration management and network security monitoring to detect abnormal login patterns early and respond quickly. This approach reduces the window of opportunity for attackers and improves overall resilience.
How to identify default credentials on Lantronix devices
Identifying defaults begins with asset discovery. Start by inspecting device labels, consulting the vendor’s official documentation for the exact model/firmware, and checking portable configuration files exported during provisioning. A common sign of default credentials is a web login prompt that uses standard terms like “admin” for both username and password, though the exact pair can vary by firmware revision. If the device is already in production, run a credential audit by attempting to log in with known vendor defaults and compare results against your project inventory. A strong practice is to establish a centralized repository to document, for each Lantronix device, the current admin username, password policy, and the date of the last password change. Remember to restrict the audit window and ensure you have authorization to test access—tests should be conducted in accordance with your organization’s security testing policy.
In addition to manual checks, many organizations leverage configuration management tools to patrol devices for noncompliant credentials. These tools can scan for common default credentials, verify password strength, and generate alerts when a device lacks evidence of a credential change. If you’re unsure of the defaults for a specific Lantronix model, the vendor’s support portal and product manuals are the most reliable sources. For governance, tie these findings to your asset management process so noncompliant devices are tracked and remediated with a clear remediation plan.
Step-by-step reset and hardening for Lantronix devices
Resetting a Lantronix device to a secure baseline involves a careful sequence to avoid downtime and ensure the new configuration is solid. Here is a practical, general approach you can adapt to your environment:
- Prepare and inventory: Identify the device, model, firmware, and its role in the network. Confirm you have authorized access for maintenance.
- Access the device: Use the console port for initial access if the web UI is unavailable, or log in to the current admin account if credentials are known.
- Reset to factory defaults (if necessary): If you need to remove all existing credentials, perform a factory reset following the vendor’s documented method. Note that this erases configurations, so have backup configurations and a rollback plan.
- Secure initial login: After reset, immediately set a strong, unique admin password. Create separate admin accounts per operator if supported by the model.
- Update firmware: Check for the latest firmware and apply updates to protect against known vulnerabilities.
- Harden access: Disable unused services (e.g., remote SSH if not required), restrict management interfaces to trusted networks, and enable logging.
- Implement policy-driven changes: Enforce a password rotation cadence, require complex passwords, and store credentials in a password manager with restricted access.
- Documentation and monitoring: Update the asset inventory, document the changes, and establish ongoing monitoring for authentication attempts and policy compliance.
This process should be integrated into your organization’s change-management workflow to ensure every Lantronix device remains compliant with security standards over time. Always refer to the exact model’s user guide, as some steps and options differ by hardware revision and firmware level.
Ongoing password hygiene and governance for Lantronix deployments
Password hygiene must be an ongoing discipline, not a one-off task. For Lantronix devices, consider a governance model that includes centralized policy enforcement and regular credential reviews. Do not rely on a single shared password across multiple devices; instead, implement per-device admin accounts and assign responsibilities to named administrators. A practical approach combines technical controls with administrative oversight:
- Establish a password policy that requires length and complexity, with a rotation cadence that aligns with risk.
- Store credentials in a trusted manager with role-based access controls and audit logging.
- Use network segmentation to limit exposure of management interfaces and apply strict access controls.
- Schedule quarterly or semi-annual audits to verify that all Lantronix devices reflect current policies and firmware baselines.
- Maintain an up-to-date inventory that records firmware versions, last password change dates, and admin account details for quick remediation.
Incorporating these practices into a security program helps ensure Lantronix devices stay resilient against credential-based threats. The broader trend in enterprise security emphasizes automated policy enforcement and continuous monitoring, which reduce the likelihood of default passwords remaining in use and improve detection of anomalous authentication activity.
Common pitfalls and how to avoid them
Even well-intentioned teams can fall into common traps that keep Lantronix devices vulnerable. One frequent mistake is treating password changes as a one-time event rather than an ongoing requirement, which can lead to stale credentials and stale access controls. Another pitfall is underestimating the importance of firmware updates, since exploit kits frequently target known vulnerabilities in older releases. A third pitfall is excessive reliance on network segmentation without verifying the security of management interfaces—attackers can pivot if they gain access through weak credentials.
To avoid these issues, implement a documented onboarding checklist that includes a mandatory password change step, firmware validation, and configuration backups. Enforce least privilege for admin access and disable any management services that aren’t required in daily operation. Finally, educate administrators about the risks associated with default credentials and provide ongoing training that covers password hygiene, incident response, and secure device handling. By addressing these pitfalls proactively, you can significantly reduce the likelihood of a credential-based compromise in Lantronix deployments.
Authority notes and guidance
For authoritative guidance on credential hygiene and secure device management, refer to government and academic sources on cybersecurity best practices and authentication. You should consult resources from cyber defense authorities such as CISA and NIST for foundational controls, as well as university-led security research for in-depth explorations of device hardening. The combination of vendor-specific best practices and government guidance provides a solid basis for securing Lantronix devices in real-world deployments. See references to CISA and NIST guidance in the related materials for a more formal understanding of recommended controls and risk mitigation strategies.
Typical credential patterns and when they are changed across Lantronix access points
| Model/Area | Default Credential Pattern | Change Status |
|---|---|---|
| Web Management Interface | varies; common: 'admin'/'admin' or vendor-defaults | Changed on first login |
| SSH/Telnet Access | varies; often admin-related defaults | Disabled or renamed |
| Serial Console | varies; may rely on simple or no password | Changed during provisioning |
Your Questions Answered
What is a Lantronix default password?
Lantronix default passwords vary by model and firmware. The key point is that credentials are intended for initial setup only and must be changed before deployment to prevent unauthorized access.
Lantronix default passwords depend on the model, but they’re meant for initial setup and must be changed before deployment.
How do I find the default password for a Lantronix device?
Check the device label, the user manual, or the vendor’s support portal for model-specific defaults. If the device has been in use, perform a credential audit to confirm whether defaults were changed.
Check the label, manual, or vendor site for defaults; audit to confirm changes.
Is it safe to use a default password?
No. Default passwords create an immediate security risk. Always replace them during onboarding and implement unique admin accounts per device when possible.
No—default passwords are risky. Change them during onboarding and use unique admin accounts.
What are best practices for password management on Lantronix devices?
Adopt per-device admin accounts, enforce complex passwords, rotate regularly, and store credentials in a secure manager with access controls and auditing.
Use per-device admin accounts, strong passwords, rotation, and a secure password manager.
What if a Lantronix device still uses a default password after onboarding?
Isolate the device, verify configuration integrity, reset if necessary, apply the latest firmware, and enforce password changes. Document remediation steps.
If defaults remain, isolate the device, reset if needed, update firmware, and enforce password changes.
Do Lantronix devices support two-factor authentication for admin access?
Some models offer enhanced authentication options. Check the specific model’s documentation to enable any available multi-factor authentication features.
Check your model’s docs to see if 2FA is available and enable it if possible.
“Default passwords are a simple but effective entry point for attackers. Always change defaults during onboarding and enforce least privilege on Lantronix devices.”
Key Takeaways
- Change default credentials during onboarding
- Audit devices regularly for noncompliant defaults
- Disable unused management services and apply least privilege
- Document credentials and changes in asset inventories
- Enforce firmware updates and periodic credential reviews