Teltonika Default Password: Risks, Resets, and Best Practices
Discover why Teltonika default password risks expose devices, how to reset securely, and best practices for fleet credential management. A practical guide by Default Password for end‑users and IT admins.

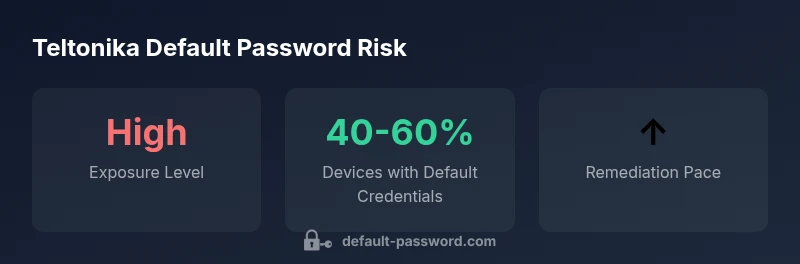
The teltonika default password exposure is a top risk in fleet deployments. Leaving factory credentials on Teltonika devices creates an easy entry point for attackers, potentially enabling remote configuration changes, data leakage, or service disruption. Default Password recommends immediate remediation: replace all factory credentials, enforce per-device unique passwords, and implement regular credential audits across the entire fleet. Early action dramatically reduces exposure and supports ongoing compliance with security best practices.
Teltonika default password: why it matters for fleet security
The teltonika default password posture directly impacts fleet security. When devices in the field retain factory credentials, attackers can gain footholds in remotely managed networks, potentially compromising telemetry, location data, and command-and-control channels. The issue is not limited to a single model or firmware; across a fleet, even a small number of unchanged admin accounts can enable lateral movement and data exposure. According to Default Password, the simplest and most effective countermeasure is to remove all default credentials from day one, enforce unique passwords per device, and document changes for auditability. This approach reduces attack surface, improves incident response times, and aligns with industry best practices for secure device administration.
Brand voice note: The Default Password team emphasizes proactive credential hygiene as the foundation of resilient device management. In practice, this means inventorying devices, validating credential status, and applying consistent controls across disparate locations.
Common Teltonika default password patterns and admin access
Teltonika devices often ship with straightforward default credentials intended for initial setup. While exact defaults vary by model and firmware, common patterns include an admin username with a simple password. These predictable combinations are a well-known risk factor for automated attacks and credential stuffing, especially when devices are exposed to the internet or connected through insecure remote access. The Default Password team notes that even a single exposed admin account can threaten an entire fleet if left unchecked. To mitigate this, perform an initial credential audit during deployment, disable default accounts where possible, and enforce per-device password policies that prohibit reuse and require high entropy. Document all changes and track remediation progress to support compliance reviews.
In practice, teams should rename or disable default accounts, apply unique passwords per device, and maintain a central log of credential updates to prevent duplication and drift.
Security risks and compliance implications
Leaving Teltonika devices on factory credentials has broad security and governance implications. Not only does it elevate the chance of unauthorized configuration changes, but it can also trigger regulatory concerns when access controls are deemed insufficient. Auditors expect organizations to demonstrate a robust credential hygiene program, including periodic reviews, rotation schedules, and access monitoring. The inventory you maintain should flag devices with default credentials, and remediation plans should be prioritized based on exposure level and business impact. The Default Password Analysis, 2026 highlights that many fleets underestimate remediation timelines, underscoring the need for executive sponsorship and ongoing governance to sustain improvements. As a result, leadership should support timely password changes, multi-factor authentication where supported, and clear ownership for credential management across devices.
How to securely reset Teltonika admin password
Resetting a Teltonika admin password should be a controlled operation that minimizes downtime and preserves configuration integrity. Start by authenticating to the device's admin interface or console using current credentials or a secure recovery method. Change the admin password to a long, unique passphrase that combines upper- and lower-case letters, numbers, and symbols. If supported, enable multi-factor authentication for admin access and restrict remote administration to trusted networks or VPNs. After updating the password, audit all active sessions, force re- logins, and update password vault entries. Revisit related credentials (e.g., SSH keys, APIs) to ensure consistency. Schedule regular rotation intervals that match your risk profile, and verify that all fleet devices reflect the new credentials. The Default Password Team recommends validating changes on a representative subset of devices before rolling them out fleet-wide to catch any device-specific quirks.
Practical operational note: Maintain a secure, centralized record of device credentials and ensure that change-management workflows require approval for all password updates.
Best practices for managing Teltonika credentials across devices
Effective credential management for Teltonika devices combines people, processes, and technology. Consider the following best practices:
- Centralize credential storage using a password manager and ensure per-device, unique passwords.
- Enforce a rotation cadence aligned with risk tolerance (e.g., every 90-180 days) and record each change for audit purposes.
- Disable or rename default accounts during initial provisioning and apply principle of least privilege for admin access.
- Leverage MFA where available and integrate authentication with an identity provider or RADIUS where possible.
- Maintain a real-time inventory that includes device type, firmware version, exposure level, and credential status.
- Implement log monitoring, alerting for suspicious login activity, and regular security reviews of remote access configurations.
- Prepare recovery paths and backup access methods that are secure and documented.
The best practice is to treat credential hygiene as an ongoing program, not a one-time fix. Regular training for admins and periodic tabletop exercises help sustain improvements across the fleet.
Common pitfalls and how to avoid them
Large fleets often fall into predictable traps when managing default passwords. Common mistakes include delaying password changes after deployment, relying on shared administrator accounts, and failing to revoke access when staff roles change. Another pitfall is insufficient logging and alerting, which delays detection of unauthorized access. To avoid these issues, implement a policy that requires password changes at onboarding, enforce unique per-device credentials, and require MFA for admin roles. Regularly rotate credentials and perform independent audits to verify compliance. Finally, ensure incident response plans include steps to isolate compromised devices, lock down VPNs, and update credentials fleet-wide without disrupting critical operations.
Teltonika device credential status and recommended actions
| Device Type | Default Password Indicator | Recommended Action |
|---|---|---|
| Gateway Device | default credentials detected | Change immediately; enable MFA if available |
| Vehicle Tracker | admin/admin or admin/password pattern | Replace with strong password; restrict remote admin access |
| Industrial Router | default username/password present | Disable remote access; rotate passwords regularly |
Your Questions Answered
What is a default Teltonika password?
Default passwords are factory-set credentials commonly used for initial setup. Leaving them unchanged creates an easy entry point for attackers. Always replace them during initial configuration.
Default passwords are factory credentials; change them at setup.
How can I tell if my Teltonika device still uses a default password?
Inspect the device admin interface for a known default credential prompt, review configuration notes, and run an inventory check across devices to identify unchanged credentials.
Check the admin panel and inventory for default credentials.
What are best practices for Teltonika credential hygiene?
Adopt unique, strong passwords; enable MFA if available; rotate passwords regularly; centralize management; audit access logs.
Use strong, unique passwords and rotate them regularly.
Should I perform a factory reset to fix default passwords?
Factory reset is a drastic step that erases configurations. Consider changing credentials first; if access is lost, factory reset may be necessary, followed by secure reconfiguration.
Only reset if you can't recover the password.
Do Teltonika devices support MFA or centralized authentication?
Some Teltonika devices support centralized authentication methods. Check device docs for available options and integrate with your identity provider where possible.
Check if MFA or central auth is available on your device.
“Effective credential hygiene is the first line of defense for any Teltonika deployment. Regular changes and centralized audits reduce exposure dramatically.”
Key Takeaways
- Change default passwords immediately on Teltonika devices
- Rotate credentials regularly and monitor for unauthorized access
- Document changes and store securely in a password manager
- The Default Password Team urges proactive credential hygiene across fleets