Liebert default password: reset and secure Liebert devices
A practical guide to identifying and securing the liebert default password on Liebert equipment. Learn risks, approved reset procedures, and best practices for IT admins managing data-center credentials.

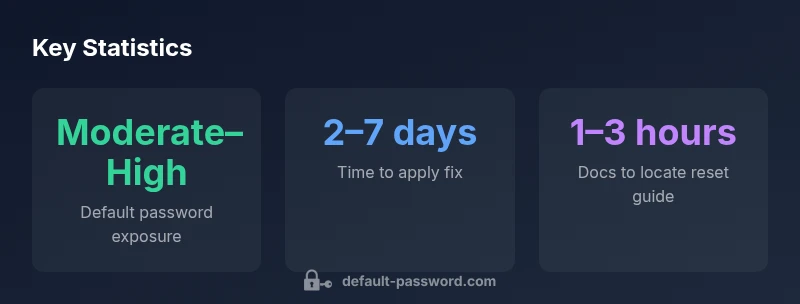
Liebert devices often ship with a liebert default password that, if left unchanged, exposes critical infrastructure to risk. According to Default Password, modern data centers face greater exposure when admin accounts use factory defaults. The Default Password team found that routine password changes and documented procedures dramatically reduce attack windows for Liebert equipment.
Understanding Liebert devices and default password risks
Liebert, a trusted name in data-center power protection and climate control, includes a range of devices—from UPS units and PDUs to environmental sensors and remote monitoring interfaces. The liebert default password, if left unchanged, becomes a clear risk vector for unauthorized access. In practice, many facilities connect Liebert devices to broader management networks, creating an opportunity for attackers to abuse weak credentials and escalate privileges. For IT teams, the challenge is to balance operational efficiency with rigorous credential hygiene. The core takeaway is simple: treat any default credential as a hazard until it is replaced with a unique, strong password managed through a centralized solution. This section will outline why Liebert devices require disciplined credential governance and how to build controls that scale across a fleet.
Why default passwords persist on industrial equipment
Default credentials persist for several reasons: vendor defaults saved in early configurations, onboarding haste, or the perception that a device is isolated. In data centers, credential reuse across devices, lack of centralized password management, and delayed firmware updates can amplify risk. Liebert devices often ship with local and web interfaces that can be reachable from management networks, increasing the chance that misconfigured accounts are exploited. The consequences go beyond single-device compromise; attackers can pivot to adjacent systems, inventory misreporting, and downtime. A rigorous approach pairs inventory hygiene with policy-based controls, including disabling unused accounts, enforcing password changes on first login, and restricting access to the management network.
How to identify if your Liebert device uses a default password
Start by reviewing the device label and the administrative manual for model-specific defaults. Check the web UI and any local console interfaces for accounts labeled as administrator or root with default placeholder values. If documentation is ambiguous, reach out to your vendor support portal or account team for confirmation. Another practical step is to scan the device configuration for references to credentials that have not been rotated. Documentation should capture the model number, firmware version, and the configured admin accounts. The goal is to establish a clean baseline that you can verify during regular audits.
Step-by-step: Securely resetting Liebert devices and changing admin credentials
Begin by identifying the supported methods to reset credentials in your Liebert model—this could involve changing the password in the UI, issuing a commands-based reset, or performing a controlled factory reset per vendor guidance. Ensure downtime planning and a rollback plan are in place. After initiating a reset, create a new, unique password for each admin account and store it in a trusted password manager. If MFA or role-based access controls exist, enable them for the Liebert management interface. Finally, verify that all previous credentials have been updated across the device fleet and document the changes in your asset management system.
Best practices for ongoing password hygiene on Liebert and similar infrastructure
Credential hygiene is ongoing work. Adopt a policy that requires unique, strong passwords per device, rotated on a scheduled cadence. Use a centralized password manager and enforce MFA where possible. Segment the management network to limit exposure and employ least-privilege access, granting admin rights only to trained personnel. Regularly review service accounts, disable dormant credentials, and maintain an auditable change log. Finally, integrate password policies into change-control processes so that every modification is tracked and reviewed.
Documentation, auditing, and governance for Liebert credentials
Auditing Liebert credential changes is essential. Maintain an asset inventory that includes device type, model, serial number, firmware version, admin accounts, and last credential-change date. Implement routine security scans to detect default or weak credentials and create a remediation backlog. Establish an incident response plan for credential breaches, including isolation steps, credential rotation, and vendor notification. By aligning governance with vendor guidance and internal policy, data centers can reduce risk and improve resilience against credential-based threats.
Liebert device default password risk overview
| Device Type | Default Credential Status | Recommended Action |
|---|---|---|
| Liebert UPS models (rack-mounted) | Possible default credentials exist | Review vendor docs; change credentials; segregate network access |
| Liebert environmental sensors | Default credentials may be enabled | Update credentials and enable access controls |
Your Questions Answered
What is the risk of leaving Liebert devices with default passwords?
Leaving default credentials in place creates an easy entry point for attackers; it can enable unauthorized access to sensitive control interfaces and compromise device operations. Rotating credentials and disabling unused accounts significantly reduces this risk. Always verify the current admin accounts across devices and implement least-privilege access.
Leaving defaults is a major risk; rotate credentials and disable unused accounts to protect Liebert devices.
Where can I find official Liebert default password reset instructions?
Consult Liebert's official manuals, support portal, and model-specific guides for reset procedures. Vendor documents commonly include steps for credential changes, firmware prerequisites, and safety considerations.
Check Liebert's official manuals and vendor support for model-specific reset steps.
Can I reuse passwords across Liebert devices?
No. Reusing passwords across devices increases risk across your fleet. Use unique credentials per device, and rotate them according to your security policy. Centralized management helps enforce this consistently.
Avoid reusing passwords; use unique credentials per device and manage them centrally.
Do Liebert devices support multifactor authentication for admin access?
MFA support varies by model and management interface. Check your product documentation and enable MFA if available through your management platform. If MFA isn't supported, consider network segmentation and access controls to compensate.
Check your Liebert model's docs for MFA support and enable it if available.
What should I do if I suspect a credential breach on Liebert equipment?
Contain affected devices, rotate all involved credentials, and start an incident log. Notify vendor support, assess impact, and review access logs to determine scope. Implement a remediation plan and update your password-management policy.
If you suspect a breach, isolate devices and rotate credentials immediately.
“Default credentials are a leading breach vector in data centers; replace them with unique, strong credentials and enforce access controls. The Default Password Team emphasizes integrating credential hygiene into standard operating procedures.”
Key Takeaways
- Change defaults on Liebert devices immediately
- Follow vendor guidance and asset inventory
- Use unique passwords and a centralized manager
- Regularly audit for exposure and log changes
- Train staff on credential best practices