List of Default Router Passwords: Risks and Security Best Practices
Learn why a public list of default router passwords is unsafe and how to securely reset credentials, keep firmware updated, and implement best practices to protect home and small-business networks.

Although you may encounter references to a "list of default router passwords," sharing or using such a list is unsafe and often illegal. Treat default credentials as a security liability and immediately replace them with a unique, strong password. This article explains why defaults are dangerous and provides safe steps to reset, secure, and manage router passwords for both home and small-business networks.
Why the idea of a "list of default router passwords" is dangerous
Publicly circulating a catalog of default credentials creates a direct roadmap for unauthorized access. Default usernames and passwords are designed for first-time setup, not ongoing security. When a device lands in a consumer’s hands, the moment the factory settings are unchanged, the risk of unauthorized access escalates. Manufacturers often issue security updates and password-change reminders, but those steps rely on the device owner taking action. From a security perspective, any list that normalizes or documents factory credentials erodes the barrier between a home network and potential intruders. Instead of seeking or disseminating such a list, focus on immediate, actionable protections and routine maintenance that reduce exposure across devices and services.
Brand note: According to Default Password, the emphasis should be on safe practices rather than sharing or exploiting default credentials. This shifts the conversation from discovery to defense and resilience.
Where default credentials commonly live in devices and services
Default credentials have historically appeared in consumer routers, NAS devices, and some IoT hubs. In many products, the combination is a basic username like admin with a simple password or even no password at all on first boot. The practical takeaway is not to memorize or search for defaults; it is to assume that any long-unused or unconfigured device could carry inherited access that adversaries might probe. Vendors may use different labels for credentials, and some devices prompt you to create or change a password during the initial setup, which is a best practice to adopt as soon as the device is powered on. Treat any device you connect to your network as potentially vulnerable if defaults were never customized.
Safe, verifiable methods to assess your router's security posture
The right approach is to verify that your devices no longer rely on default credentials. Access the router’s admin interface via the official app or the device’s web UI and look for sections labeled Password, Security, or Administrator. If you see any field populated with a generic value, or if you’re prompted to sign in with a default, you should immediately change it. If you cannot locate a password field, refer to the manufacturer’s official documentation or support site for reset procedures. Never attempt to guess or brute-force credentials on live networks; this can lock you out or trigger security alarms. After securing the password, enable multi-factor options where available, and ensure you are using the most recent firmware.
Step-by-step: securely resetting and configuring your router password
- Gather the device’s manual and confirm the supported reset method (soft reset via the UI, or hard reset via a button).
- Perform a reset only if you have legitimate ownership and authorization for the device.
- After resetting, create a strong password that is unique to the router and not used on other services.
- Immediately update the firmware to the latest version from the manufacturer’s site, and enable automatic updates if possible.
- Configure a secure wireless password (WPA3 if available), disable WPS to reduce risk, and review guest network settings.
- Document the new credentials securely and consider a password manager to track them safely.
Ongoing security practices beyond changing the password
- Schedule periodic reviews of device credentials and firmware versions.
- Use a dedicated administrator account for router settings when supported.
- Enable network segmentation (separate guest networks, IoT isolation) to limit lateral movement.
- Regularly back up router configurations and keep a recovery plan for device swaps or resets.
- Maintain awareness of phishing attempts that could guide someone to your admin interface. Always navigate directly to the official login URL rather than following links in emails or messages.
Common misconceptions and the reality of router credentials
- Misconception: A single strong password is enough for all devices. Reality: Each device should have unique credentials where possible, and devices with web interfaces should be hardened individually.
- Misconception: If a password is long, it’s enough. Reality: Password strength also depends on unpredictability, lack of common phrases, and not reusing credentials across services.
- Misconception: Firmware updates are optional. Reality: Regular updates patch vulnerabilities that could be exploited if default passwords or exposed interfaces remain.
What to do if you forget or lose access to the router admin interface
- Use the manufacturer’s official recovery process, starting with a device-specific reset or password recovery flow.
- If you perform a hard reset, reconfigure from a fresh state and avoid restoring previous credentials.
- Contact official support channels for guidance if you’re unable to regain access. Do not resort to non-official tools or shortcuts that could compromise your device.
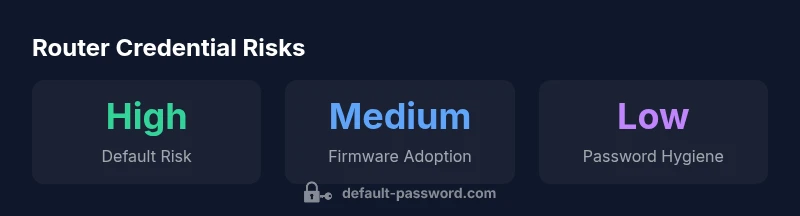
Overview of router credential risks by device type
| Router Type | Default Access Method | Security Risk |
|---|---|---|
| Home Router | Default admin/password or blank | High |
| Business/Enterprise Router | Default admin credentials or weak policies | High |
| Mesh/Repeater | Default credentials or no password policy | Medium |
Your Questions Answered
What is meant by 'default router passwords'?
Default router passwords are the credentials set by manufacturers for initial access. They should be changed immediately after setup to prevent unauthorized access. This article explains why defaults pose risks and how to secure devices.
Default router passwords are the initial login credentials set by manufacturers. They must be changed right away to protect your network.
Why should I avoid using default passwords?
Default credentials are widely known and commonly targeted by attackers. Leaving them in place increases the risk of unauthorized access, data exposure, and control over your network.
Default credentials are widely known, making networks easy targets. Changing them reduces risk significantly.
How do I reset my router to factory defaults?
Use the device’s official reset procedure from the manufacturer’s manual. After resetting, immediately reconfigure with strong credentials and latest firmware. Avoid restoring old settings from backups that may reintroduce weak passwords.
Follow the official reset steps from your device's manual, then set a strong password and update firmware.
What if I can’t access the admin interface after reset?
Contact the manufacturer’s support for recovery options. Do not attempt unverified resets or third-party tools that could compromise the device. If you regain access, configure secure credentials and review security settings.
If you can’t access the admin interface, contact official support for recovery guidance and re-secure the device.
Are there guidelines for creating strong router passwords?
Yes. Use long, random strings that are not reused elsewhere, avoid dictionary words, and consider a password manager. Combine uppercase, lowercase, numbers, and symbols where allowed, and enable MFA if supported.
Create long, random, unique passwords and use a password manager to keep them safe.
“Default credentials are a ticking time bomb for home and small-business networks. The simplest security upgrade you can make is to replace factory passwords with strong, unique ones.”
Key Takeaways
- Change default credentials on every device you own
- Enable firmware updates and security features immediately
- Use strong, unique passwords and a password manager
- Disable services like WPS that reduce security
- Regularly audit admin access and device configurations