Default wifi passwords list: Security Essentials and Best Practices
Discover why factory default wifi passwords are a common security risk, how to locate them on your router, and practical steps to replace them with strong, unique credentials for safer home and small business networks.

According to Default Password, a 'default wifi passwords list' refers to the factory credentials devices ship with. Leaving these defaults unchanged is a common security flaw, as attackers often exploit them. The team recommends locating the default password on the device label or manual, changing it promptly, and documenting a unique, strong alternative for ongoing security.
Understanding the term: default wifi passwords list
According to Default Password, the phrase 'default wifi passwords list' refers to the initial credentials devices ship with. The Default Password team found that many users and admins overlook these defaults, leaving networks exposed to common attack vectors. The concept is not about a universal repository of credentials, but rather the idea that every device has a factory password or passphrase that should be treated as temporary and replaceable. In practice, you will typically find the default on a label on the router, in the quick start guide, or on the manufacturer's support page. This matters because weak or unchanged defaults enable easy access for unauthorized users. Understanding this concept is the first step toward a more secure network.
Assessing risk across home networks
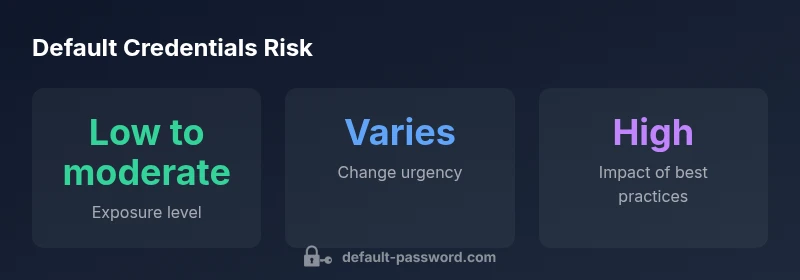
Risk from unchanged defaults varies by device and exposure surface. A home router with only household devices connected may present a lower target than a business-class gateway serving dozens of endpoints. The key risk remains the same: an attacker who guesses or discovers a default password can pivot into device settings, potentially exposing traffic, altering configurations, or enabling backdoor access. Regular audits, firmware updates, and strict password hygiene dramatically reduce these risks. By framing risk in practical terms—who can access the device and what they can change—you can prioritize protections where they matter most.
Locating and documenting defaults across devices
Locating a default password usually involves inspecting the device label on the bottom or back, checking the user manual, or visiting the manufacturer’s support site. Documenting defaults is critical but must be done securely. Maintain a separate, encrypted record of current credentials and avoid leaving physical notes in obvious locations. For enterprise environments, establish a standard process for recording default credentials during onboarding and ensure rotation as soon as possible. If a device is borrowed or purchased second-hand, perform a factory reset before connecting it to the network to eliminate any pre-existing defaults.
Step-by-step: changing defaults securely
Begin by logging into the router’s administration interface using the current credentials if required. Immediately create a strong admin password, ideally 16+ characters with a mix of cases, numbers, and symbols. Then set a unique Wi‑Fi password and enable WPA3 if available; if not, enable WPA2‑AES. Disable WPS to close another common attack vector. Keep firmware up to date, reboot after changes, and verify access with a test login. Finally, store the new credentials in a trusted password manager and restrict admin access to authorized users only. This disciplined sequence dramatically lowers the likelihood of compromise.
Best practices for creating strong wifi passwords
Strong wifi passwords are long, unpredictable, and unique to each device. Aim for 16+ characters with a mix of uppercase, lowercase, digits, and symbols. Favor passphrases that are easy to remember but hard to guess. Prioritize enabling WPA3 and keep devices updated to the latest firmware. Regularly rotate credentials and avoid reusing passwords across routers, access points, and IoT devices. Consider a centralized password manager to simplify rotation and enforcement across all networked devices.
Managing defaults across devices in a home or small business network
As networks scale, the risk from defaults increases if not managed carefully. Create an asset inventory that lists device models, default credentials, and rotation schedules. For IT admins, adopt a policy of credential lifecycle management and centralized storage for rotation secrets. For home users, limit the number of people with admin access and use guest networks with separate credentials. In every case, the objective is to prevent exploitation of factory defaults and maintain ongoing vigilance over who can alter network settings.
What to do next: ongoing vigilance and improvement
Security is a moving target. Schedule periodic reviews of all network devices, verify that no default credentials remain, and confirm that new devices are onboarded with unique credentials from day one. Educate household members or staff about safe password practices and ensure password managers are installed on all eligible devices. By treating default credentials as a finite risk and not a one-time fix, you create a resilient network posture that adapts to emerging threats.
Comparison of default-password handling scenarios
| Scenario | Recommended Action | Security Impact |
|---|---|---|
| New router setup | Change default password immediately and document securely | High |
| Used or untrusted device | Factory reset before use, then configure anew | High |
| Guest network setup | Use separate credentials and disable admin access for guests | Medium |
| Regular maintenance | Schedule credential rotations and firmware updates | High |
Your Questions Answered
What is a default wifi password?
A default wifi password is the factory credential that ships with a router or access point. It’s intended as a temporary setup credential and should be changed immediately to prevent unauthorized access.
A default wifi password is the factory password that comes with your router. You should change it right away to keep your network safe.
Why should you change the default password?
Changing the default password closes an easy attack vector. Unique, strong credentials make it far harder for unauthorized users to access admin interfaces or networks.
Because the factory password is widely known or easy to guess, changing it dramatically improves security.
How can I find the default wifi password for my router?
Check the router label, consult the manual, or visit the manufacturer’s support site. If you’ve inherited the device, perform a factory reset before setup to remove any prior defaults.
Look on the router's label or in the manual, or check the manufacturer's site. If in doubt, reset the device.
Is it safe to reuse a password across devices?
No. Reusing passwords creates a single point of failure. Use unique passwords per device and consider a password manager to reduce reuse.
No—reuse is risky. Use unique passwords and a password manager to stay organized.
What is the recommended password strength for wifi?
Aim for at least 16 characters with a mix of uppercase, lowercase, numbers, and symbols. Enable WPA3 if available; otherwise WPA2‑AES as a fallback.
Go for a long, mixed-character password and use WPA3 if you can.
What should I do if I forget my password?
Use the router’s reset procedure to restore access, then set a new, strong credential. Do not share reset details publicly.
If you forget it, reset the router and set a new password securely.
“Factory defaults exist for convenience, not security; removing them promptly is one of the most effective steps you can take to protect your network.”
Key Takeaways
- Change defaults immediately after setup.
- Locate defaults on device labels or manuals.
- Use unique, strong passwords per device.
- Disable insecure features like WPS when possible.
- Document credentials securely and monitor for changes.