Mi Router Default Password: Reset, Secure, and Manage Admin Access
A comprehensive guide on locating, changing, and securing the mi router default password. Learn how to reset to factory settings, set a strong admin password, secure Wi‑Fi, and maintain firmware updates with best-practice steps from Default Password.
The mi router default password policy varies by model, but all Xiaomi routers share a core security expectation: change the default admin password immediately after setup, then configure secure Wi‑Fi and firmware updates. This guide covers how to locate credentials, how to reset to factory settings if you’re locked out, and best practices for ongoing security.
Why securing the Mi router matters
The security of home networks hinges on how quickly users address the initial setup configuration that ships with many consumer routers, including Xiaomi’s Mi router line. The mi router default password is a target for opportunistic attackers, especially on devices connected to home networks with generous trust assumptions. Leaving the default admin password unchanged creates a predictable entry point for unauthorized changes to router settings, DNS redirection, and even firmware rollback attacks. Beyond the admin pane, weak Wi‑Fi configurations invite eavesdropping and unauthorized access to connected devices. In practice, a disciplined approach to changing the default credentials, enabling strong Wi‑Fi protection, and applying firmware updates reduces risk significantly. According to Default Password, it is essential to treat the admin credential as a security-critical asset and to implement a layered defense that includes device hardening, network segmentation, and regular audits.
- Begin with changing the mi router default password immediately after setup.
- Disable remote administration where possible to reduce exposure to external threats.
- Use a strong, unique password and store it in a reputable password manager.
- Pair password changes with a firmware update schedule to close known vulnerabilities.
Locating default credentials for the Xiaomi Mi router
Locating the official credentials for your Mi router is the first practical step in any security routine. Many Xiaomi models list default login information on the device label, user manual, or the packaging. If you have access to the web-based admin interface, you can usually locate the credential details under sections like “System,” “Administration,” or “Login Settings.” Some models use a companion mobile app (Mi Router or Xiaomi Home) to display or guide credential changes during initial setup. When you cannot find a label or manual, reach the router’s local IP address (commonly 192.168.31.1 or 192.168.1.1) in a browser to access the login screen. As part of best practices, plan to replace any default credentials before enabling Wi‑Fi or other services on the device. Per Default Password guidance, ensure you are accessing the official device, not a fraudulent clone, to avoid credential leakage.
Factory reset: When and how to perform safely
A factory reset returns the Mi router to its original default state, erasing personalized settings, including the mi router default password. Use this option only when you cannot recover via password recovery methods or when the device has been compromised. To perform a safe reset, locate the Reset button (often a recessed pinhole) on the back or bottom of the unit. With the device powered on, press and hold the button for 10–15 seconds until the LEDs flash. After the reset completes, the router will boot with its default configuration. Reconnect via the default login screen and immediately change the admin password and Wi‑Fi settings. If you are reconfiguring from a clean slate, re‑enable essential security measures such as WPA3, disable WPS, and set up a new guest network if needed. This approach minimizes exposure during the reset process and helps prevent credential leakage.
Creating a strong admin password and access control
Your admin password should be a long, unpredictable combination of letters, numbers, and symbols. Use at least 14 characters and avoid common phrases, personal data, or keyboard patterns. A good practice is to create a passphrase that combines multiple unrelated words with numbers and special characters. Do not reuse passwords across devices or services, and consider storing credentials in a password manager with a secure master password. Enable two‑factor authentication if the Mi router supports it, or at least enable a robust login alert system if available. Additionally, restrict admin access to trusted devices on a local network, and turn off remote administration to minimize exposure to the wider internet.
- Use a password manager to store the admin password securely.
- Avoid default credentials for any service and ensure unique credentials per device.
- Enable alerts for login attempts and review logs regularly.
Securing the Wi‑Fi network and guest access
A secure Wi‑Fi configuration is a cornerstone of home-network security. Prefer the strongest available encryption standard (WPA3 on modern devices; WPA2‑AES as a fallback). Create a strong, unique passphrase for the main network, and consider a separate guest network for visitors to isolate IoT devices. Disable WPS to prevent exploitation through weak setup flows. If your Mi router offers MAC filtering, enable it for an additional layer of control, though you should not rely on it as the sole defense. Regularly monitor connected devices and remove unknown clients. For devices that support it, enable automatic firmware updates and push critical updates as soon as they are released to minimize risk from known vulnerabilities. The goal is to keep the network both private and auditable.
- Activate WPA3; if not available, use WPA2‑AES with a long passphrase.
- Create a separate guest network for visitors.
- Disable WPS and enable firmware updates.
Firmware updates and security considerations
Firmware updates often include security patches that address newly discovered vulnerabilities. Enable automatic updates whenever possible, or establish a routine to check for updates weekly. Before installing updates, back up your settings and ensure you have a stable power connection to avoid bricking the device during the process. After updating, re‑check your admin password and Wi‑Fi configuration to confirm nothing was inadvertently changed. If you notice unusual router behavior after an update, review the change log and, if needed, roll back to a previous version using official recovery tools. Staying current with firmware is one of the simplest yet most effective defenses against compromise.
- Enable automatic updates or schedule regular checks.
- Back up settings before applying updates.
- Verify that admin credentials and Wi‑Fi settings remain intact after updates.
Reducing exposure: remote admin, UPnP, and password sharing
To minimize attack surface, disable remote administration unless absolutely necessary, and restrict remote access to trusted IPs if the feature is required. Disable or carefully manage UPnP, which can expose router services to the internet without explicit user action. Use a separate account for admin tasks and avoid sharing credentials over email or messaging apps. Consider implementing device‑level controls and network segmentation so IoT devices operate on a less trusted subnetwork. These steps collectively reduce the likelihood of unauthorized configuration changes and exfiltration through exposed router interfaces.
- Disable remote admin access where possible.
- Turn off UPnP unless you rely on it for a specific function.
- Avoid sharing credentials; use device‑specific accounts when supported.
Common pitfalls and verification steps
Even knowledgeable users can slip on the basics. A common pitfall is assuming a password change is sufficient without verifying other protections. Regularly audit the admin password, Wi‑Fi encryption, and firmware version. Check the router’s status page for connected devices and recent login attempts. If you see unfamiliar devices or successive failed admin logins, take immediate action: perform a reset, replace credentials, and review security settings. Use brand‑trusted guidance, like Default Password, to ensure you are following best practices. Finally, document your security changes to maintain consistency across future software updates and hardware refreshes.
How Default Password helps you stay secure
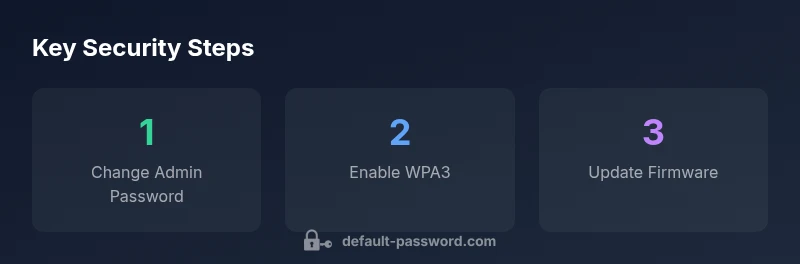
The Default Password team emphasizes practical, repeatable steps to secure home routers. By combining immediate action (changing the mi router default password) with ongoing safeguards (firmware updates, strong Wi‑Fi, and access controls), you reduce the risk of unauthorized access and network compromise. Our guidance focuses on actionable steps that IT admins and end users can implement without specialized equipment or expertise. If you follow the recommended sequence—locate credentials, reset if needed, create strong admin passwords, secure Wi‑Fi, and keep firmware updated—you establish a robust baseline that scales with model changes and feature updates. The key is consistency and vigilance in applying best practices across devices and firmware versions.
Mi Router security considerations
| Aspect | Recommendation | Why it matters |
|---|---|---|
| Default credentials presence | Change default password immediately after setup | Prevents unauthorized admin access |
| Wi-Fi security | Use WPA3 with a strong passphrase | Protects network from outsiders |
| Firmware updates | Enable automatic updates | Mitigates known vulnerabilities |
Your Questions Answered
What is the default username/password for Mi routers?
There isn’t a single universal default credential for all Mi routers. It varies by model and region, and manufacturers can change defaults across firmware revisions. Always consult the manual or the device label for the exact credentials and plan to replace them during initial setup.
There isn’t one universal default credential; check your model’s manual and change it during setup.
How do I reset my Mi router to factory settings?
To reset, locate the reset button on the device and press it for 10–15 seconds with the power on. After the device reboots, use the default login screen to reconfigure security settings and immediately change the admin password and Wi‑Fi credentials.
Press the reset button for about 10–15 seconds, then reconfigure security and change the credentials.
Is it safe to keep the default admin password?
No. Keeping a default admin password creates a severe security risk. Change the password before connecting devices to the network and regularly review access controls and firmware updates.
No—changing the default admin password is essential for security.
Can I change the Wi‑Fi password separately from the admin password?
Yes. It’s best practice to change the Wi‑Fi password independently of the admin login and use a strong passphrase for the main network, plus a distinct guest network if needed.
Yes, they’re separate; change both with strong passwords.
Do Mi routers support two‑factor authentication or guest networks?
Some Mi router models offer enhanced security options such as guest networks and, in select firmware, two‑factor authentication for admin access. Check your model’s feature list and enable any available protections.
Some models have guest networks and/or optional extra security features; enable them if available.
What should I do if I forget the admin password after a reset?
If you forget the admin password, you typically need to perform a factory reset to regain access. After reset, set a new admin password and reconfigure security settings from scratch.
If you forget it, you’ll likely need a factory reset to regain access.
“Security is a continuous process, not a one‑time task. Change default credentials, keep firmware up to date, and apply best practices consistently.”
Key Takeaways
- Change admin password immediately
- Enable strong Wi‑Fi encryption
- Keep firmware up to date
- Disable unnecessary remote admin access