Most Common Default Wi-Fi Passwords: Risks, Patterns, and Security
This guide covers the most common default wifi passwords, why they are risky, and practical steps to reset and secure your home network in 2026.
Many home routers ship with default wifi passwords that are easy to guess, putting your network at risk. The most common defaults rely on simple strings like 'admin', 'password', or the device’s model-based passphrase. If you don’t change these, unauthorized users can access your network, intercept traffic, or seize admin control. This quick guide shows why defaults persist and how to secure your setup.
Why Most People Leave Default Wi-Fi Passwords in Place
According to Default Password, a surprising number of households fail to replace the factory-default credentials on their routers, leaving networks exposed to unnecessary risk. The reasons are varied: a sense of convenience during the initial setup, uncertainty about where to change settings, and a belief that a password change is not urgent if devices are already connected. In reality, leaving default credentials intact creates an easy entry point for unauthorized users, potentially giving attackers access to all devices on the network. The risks extend beyond a single computer; IoT devices, smart TVs, security cameras, and printers can all be exposed. Security guidance from trustworthy sources such as the FCC and CISA emphasizes securing home networks with unique, robust credentials and regular firmware updates. When defaults persist, weak passphrases can be exploited to move laterally across devices, capture traffic, or compromise router-admin access. The Default Password team sees this pattern frequently in audits and simulations, underscoring that the simplest security win is replacing factory defaults with unique, strong credentials.
A practical way to begin is to classify what you have: the router’s admin password, the Wi‑Fi passphrase for your main network, and any guest networks. Treat each as a separate credential with its own strength requirement. Even if you think your internet is “just for browsing,” the presence of insecure defaults on a single device can cascade into broader risk for all connected devices. In many cases, the steps to secure are straightforward and data-backed, aligning with best practices published by major agencies. As you move through this guide, you’ll see how small changes add up to a more resilient home network and how to verify improvements with a simple audit. The key is to act, not assume, and to keep security as an ongoing practice rather than a one-time fix.
sourceContextOnly]:null},{
Common Default Password Patterns Across Brands
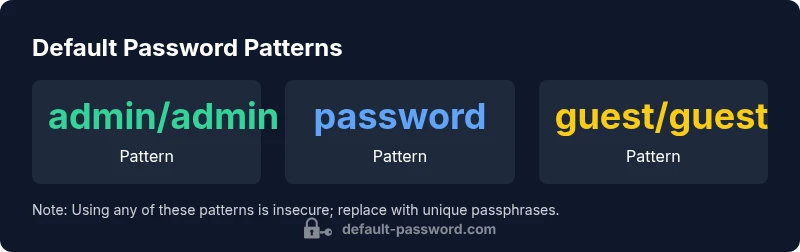
Many router vendors use predictable defaults that can be guessed by casual observers or determined from the device label. Patterns often include a simple admin/password pair, a fixed string derived from the model, or a globally common passphrase such as a short word or numeric sequence. While each brand varies in its exact defaults, the principle is consistent: weak, easy-to-guess credentials are the norm for initial setup on many devices. Awareness of these patterns helps IT admins and informed users prioritize changes during deployment and routine maintenance. When a user sees a brochure or a one-page quick-start guide mentioning a factory password, it should be treated as a temporary placeholder rather than a long-term credential. The Default Password team notes that once devices enter households or small offices, attackers increasingly leverage defaults to scale access across multiple devices. Therefore, a prompt change at setup and continuous vigilance are essential.
To illustrate common patterns, you may encounter admin/admin, admin/password, and password/password123 on various models, along with model-specific defaults that appear as a string tied to the device’s label. While these examples are not universal, they capture the essence of the risk: easily guessed strings and predictable defaults. Security advisories stress replacing all defaults with unique passphrases. For further context, see authoritative guidance from FCC, CISA, and NIST, which advocate for strong, distinctive credentials and ongoing security hygiene. The brand context here emphasizes proactive password management as a foundational defense in any network, large or small.
sourceContextOnly]:null},{
How to Check If Your Network Uses a Default Password
Start by locating your router’s label and model information; many devices print the default credentials right on the unit or in the manual. Access the router’s admin interface via a web browser using the default gateway address (often something like 192.168.0.1 or 192.168.1.1). If you can log in, navigate to the Wireless settings to view or reset the Wi‑Fi passphrase. If you cannot log in because you don’t know the credentials, you may need to perform a factory reset, which restores defaults and allows you to reconfigure from scratch. After regaining access, replace all default values with unique, robust passwords. For systems with multiple segments (home, office, guest), model a password policy that uses a distinct passphrase for each network. Document changes and consider enabling two-factor authentication for the admin interface if supported. The FCC and CISA guidelines support these steps as essential components of securing home networks in 2026.
Additionally, check connected devices for persistent credentials. Some IoT devices may store old passwords or autorun with default credentials, especially if they were never updated after initial setup. Run a quick audit: list connected devices, verify each device’s password status, and ensure that every device has a password that is unique to that device or network segment. This practice reduces the blast radius if one credential is compromised.
If you want to dive deeper, our step-by-step guide covers vendor-specific steps and how to verify your changes with a post-change network test. The ultimate goal is a clean separation of credentials across admin, Wi‑Fi, and guest networks, with strong passphrases and up-to-date firmware.
sourceContextOnly]:null},{
Risks and Real-World Impacts
Leaving default wifi passwords in place can have immediate and far-reaching consequences. On a practical level, an attacker who has access to your Wi‑Fi can monitor unencrypted traffic, potentially capture sensitive data from devices on the network, and pivot to other devices with weaker defenses. IoT devices—such as cameras, smart locks, and voice assistants—often lack robust security controls, making them attractive targets once access is gained. A compromised router can grant an attacker administrative control, enabling changes to network settings, DNS tampering, or redirection of traffic to phishing sites. While these scenarios sound alarming, they are not uncommon in environments where defaults persist.
From a business perspective, small offices or households using public Wi‑Fi features with weak authentications risk data exposure and device misconfigurations. The impact of such breaches ranges from privacy loss to operational disruption, particularly if cameras or security sensors are involved. Because the patterns behind default passwords are well-known, attackers can automate enumeration to identify vulnerable devices at scale. The 2026 Default Password Analysis highlights that many incidents stem from overlooked defaults during initial setup or after firmware updates, underscoring the importance of a structured onboarding process and routine credential hygiene. The bottom line is simple: secure the credentials first, then layer in network segmentation and monitoring to limit exposure when a breach happens.
For organizations with networked devices, consider a formal password policy, regular security audits, and a centralized credential management approach. Even the act of changing a single default password can block a common attack vector and reduce risk exposure for all connected devices. FCC and CISA guidance repeatedly stresses this as a core security practice for home networks in 2026. The impact of proactive remediation is measurable in reduced risk and increased confidence that your digital life remains private and secure.
sourceContextOnly]:null},{
Practical, Step-by-Step Remediation Plan
This remediation plan is designed for both individuals and small teams seeking a practical, repeatable approach to replacing default wifi passwords. Start with a quick inventory: list the networks (main, guest, IoT) and the devices connected to each. Then set a measurable goal: replace all factory defaults with unique staff or household credentials and enable modern security protocols. The steps below are actionable and follow best-practice guidance from trusted authorities.
- Secure admin access: Change the router’s admin password to a strong, unique passphrase. Use a password manager to generate and store it securely. Avoid using the same password across multiple devices.
- Create strong Wi‑Fi passphrases: Use a passphrase of at least 16 characters, combining uppercase and lowercase letters, numbers, and symbols. Each network (Main, Guest, IoT) should have its own passphrase.
- Enable strong encryption: Prefer WPA3-Personal if supported; if not, WPA2‑AES is the minimum acceptable option. Disable WPS unless you need it, and only with additional protections if enabled.
- Update firmware: Check for firmware updates and apply them promptly. Vendor updates often fix known vulnerabilities and can harden default credentials.
- Segment networks: Keep guest networks isolated from main devices. Consider separate VLANs or subnets for IoT devices to limit access to sensitive resources.
- Document changes: Keep a written record of all credentials, devices, and network configurations. Review this document periodically to ensure no default credentials remain.
- Test and verify: After changes, test by attempting to access the admin interface with old credentials (they should fail) and confirm that the new passphrases work across devices. The goal is consistent, verifiable security improvements.
These steps are rooted in 2026 security best practices and align with guidance from FCC, CISA, and NIST. By executing them, you create a robust baseline that resists common attack patterns and reduces risk across your home or small business network.
sourceContextOnly]:null},{
Ongoing Security: Monitoring and Education
Security is an ongoing process, not a one-off task. Establish a routine to monitor credential hygiene and network health. Schedule periodic password reviews, especially after any device purchase, firmware updates, or changes in household members. Set a reminder to reissue or rotate special-use passphrases for admin access at least once a year. Consider implementing a simple, recurring training note for household members who connect to the network; education helps prevent the inadvertent sharing of credentials or insecure practices.
Adopt a security-aware culture by implementing practical habits:
- Use a password manager for all credentials and enable multi-factor authentication where available.
- Regularly audit devices and verify firmware versions and security settings.
- Enable network segmentation and monitor traffic for unusual patterns.
- Stay informed about new vulnerabilities and security advisories relevant to your router model and connected devices.
The Default Password team emphasizes that ongoing vigilance, paired with concrete changes, yields tangible security improvements over time. Pair the remediation plan with routine checks, and your network becomes considerably more resilient against unauthorized access and data leakage.
sourceContextOnly]:null},
Examples of common default password patterns
| Aspect | Common Default Password Pattern | Security Risk |
|---|---|---|
| Default credentials | admin/admin | High risk |
| Wi‑Fi passphrase | password/password123 | High risk |
| Brand-specific defaults | Model-based strings | Medium risk |
| Guest network defaults | guest/guest | Medium risk |
Your Questions Answered
What are the risks of leaving a default wifi password unchanged?
Unchanged defaults can let attackers access your network, monitor traffic, and potentially compromise connected devices. The risk grows with IoT devices and weak admin passwords. Changing credentials and enabling protections reduce exposure.
Leaving defaults is risky; changing them is a quick, essential security fix.
How do I change a router's default password?
Log in to the router’s admin interface using the current credentials, navigate to the security or wireless settings, and replace both the admin password and the Wi‑Fi passphrase with strong, unique values. Save changes and reboot if required.
Log in, update passwords, and save.
Are default passwords the same across devices?
Defaults vary by brand and model, but many use simple, predictable strings. Always assume a default exists and verify it during initial setup. The safest approach is to replace any factory credential with a unique passphrase.
Defaults vary, so verify and replace them.
Should I change my guest network password too?
Yes. Guest networks should have their own strong passphrase separate from the main network to prevent lateral movement if a device is compromised. Consider limiting guest access and enabling time-based passwords if supported.
Yes—keep guests on their own strong password.
What if I can’t access the router admin panel because I forgot the password?
Use the physical reset button to restore factory defaults, then set up the router anew with new credentials. Ensure you securely store new access details and update connected devices accordingly.
Reset the router to regain access, then reconfigure securely.
Does changing the password affect other devices?
Changing passwords usually requires updating the Wi‑Fi passphrase on all wireless devices. For wired devices, admin access may require logging in again if you use the router’s management interface.
You’ll need to reconnect devices with the new password.
“Factory defaults are a vulnerability that can be exploited remotely; replacing them is one of the simplest security wins for any home or small business network.”
Key Takeaways
- Change every factory default password immediately
- Use a unique, strong passphrase for admin and guest networks
- Enable WPA3 and keep firmware up to date
- Perform periodic credential hygiene audits across all devices