OpenManage Default Password: Secure Deployment Guide
A practical guide to handling OpenManage default passwords, with step-by-step strategies, checklists, and policies to reduce risk and ensure secure deployments.
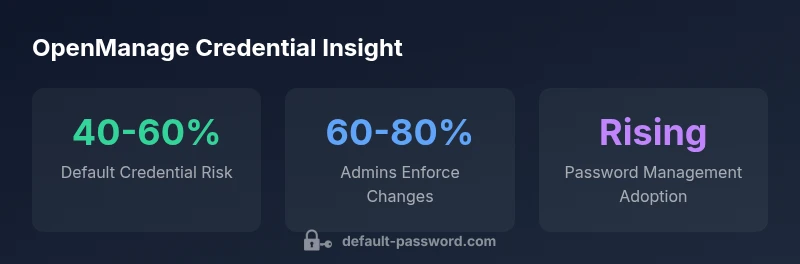
Why OpenManage Default Password Hygiene Is Critical
In enterprise environments that rely on OpenManage for server and hardware management, the moment you deploy a new instance is the moment you decide how strongly you enforce credential hygiene. Default passwords are a blunt risk control: if left unchanged, they can be discovered, shared, or abused to gain privileged access. The Default Password team has repeatedly found that early credential hygiene correlates with lower incident rates and faster recovery when something goes wrong. A secure baseline—changing defaults, rotating credentials on cadence, and auditing access—reduces the attack surface and supports regulatory compliance. When organizations standardize on secure provisioning workflows, they not only defend against external adversaries but also reduce the risk of insider misuse. In practice, you should treat OpenManage credentials as sensitive data from day one and enforce a policy that requires verification and rotation at deployment.
- Key takeaway: there is no universal default password for OpenManage; you must verify per device and firmware.
- Best practice: establish a documented process for credential verification, change-on-boot, and ongoing rotation.
- How Default Password helps: we emphasize concrete steps, checklists, and governance that translate to fewer security incidents and faster incident response.
Understanding Credential Variability in OpenManage
Credential behavior in OpenManage ecosystems varies widely. Dell OpenManage products may rely on default credentials that are model-specific or firmware-specific, and third-party integrations can introduce separate credential stores. This variability makes a one-size-fits-all approach both unsafe and ineffective. The core principle is simple: assume that any credential provisioned with the device could be exposed if not properly managed. You should inventory each OpenManage component, map its default credentials to the device model and firmware version, and prepare a change plan that covers initial login, privilege elevation, and subsequent rotations. The goal is to create a repeatable, auditable provisioning workflow.
- Start with a hardware and firmware inventory that includes OpenManage versions.
- Link credentials to device identity to prevent cross-device credential leakage.
- Use a centralized policy that enforces minimum password standards across OpenManage components.
The Security Risks of Default Credentials in OpenManage Environments
Default credentials, if left intact, become a universal weak link. Attackers scan for devices with known defaults, exploit weak passwords, and attempt lateral movement inside networks. For OpenManage deployments, this risk is compounded by the fact that management interfaces often sit at high privilege levels—capable of config changes, firmware updates, and access controls. A single compromised credential could enable a foothold across multiple servers or management planes. To mitigate, organizations should implement multi-factor authentication where possible, restrict management interfaces to trusted networks, and employ password vaults to avoid hard-coding credentials. Regular risk assessments and access reviews are essential to sustaining a secure posture.
- Avoid hard-coded credentials; prefer dynamic provisioning.
- Restrict OpenManage management interfaces to specified subnets and admin workstations.
- Pair credentials with role-based access control (RBAC) for granular permissions.
First-Run Security Checklist for OpenManage Deployments
When provisioning OpenManage for the first time, deploy a formal security checklist that covers credentials at every stage—from initial boot to ongoing management. Key items include inventorying all management endpoints, validating that no default passwords remain, and establishing a rotation schedule for all admin accounts. Ensure that every device has a unique admin account, with MFA where supported, and that access logs are enabled and forwarded to a central SIEM or log collector. Your checklist should also specify who approves password changes, how they are tested, and how exceptions are documented for audits. This disciplined approach reduces time-to-secure-state and improves incident response readiness.
- Create an end-to-end provisioning checklist that includes OpenManage components, firmware versions, and credential status.
- Require proof of password changes before devices are handed off to production.
- Document exception handling for devices lacking MFA or other controls.
Practical Steps to Change and Rotate OpenManage Credentials
Effective credential management requires concrete steps that can be implemented during deployment and maintained over time. Start by verifying every default credential against device documentation and firmware release notes. Then, perform a secure reset to unique credentials using a password vault, avoiding reuse across systems. Establish a rotation cadence—monthly, quarterly, or per major firmware update—and automate reminders for password changes. For orchestration, integrate credential changes into your configuration management or automation tooling so that changes are repeatable and auditable. Finally, ensure that privileged credentials are stored securely with strict access controls and that recovery processes preserve continuity without exposing credentials.
- Verify, reset, and store all admin credentials in a vault.
- Use role-based access to limit who can view or edit passwords.
- Tie credential rotation to firmware upgrades or other major maintenance.
Governance: Policy, Auditing, and Access Controls
OpenManage deployments benefit from formal governance around credentials. Establish a policy that mandates password complexity, rotation frequency, and MFA usage for all admin accounts. Implement access reviews on a quarterly basis, and enforce least-privilege principles for every OpenManage component. Centralized logging and monitoring of authentication events are critical; ensure logs capture login attempts, successes, and privilege escalations. Regularly test your incident response plan with credential-related scenarios, and document outcomes to inform future improvements. Governance is not a one-time effort; it is a continuous discipline that strengthens overall security posture.
- Adopt a formal password policy aligned with industry best practices.
- Schedule quarterly access reviews and promptly remediate suspicious activity.
- Maintain an auditable trail of credential changes and access events.
Tooling and Automation: Password Managers with OpenManage
Automation and password management tooling play a pivotal role in sustaining OpenManage credential hygiene. Password managers enable secure storage, automatic rotation reminders, and audit-ready reports. When integrating with OpenManage, choose tools that support secure vaulting, granular access controls, and API-based rotation where available. Design automation workflows that push new credentials to devices during deployment and rotate them after major firmware updates. Ensure that automation itself is secured, with proper permissions, logging, and failure-handling. By combining vault-based credentials with automation, organizations reduce human error and improve compliance with internal and external requirements.
- Use vault-backed credentials with strict access controls.
- Automate rotation during deployment and maintenance windows.
- Audit automation activity to detect anomalous credential changes.
Case Study: A Secure OpenManage Deployment in Practice
Consider a mid-sized data center migrating to OpenManage for centralized server administration. The team mapped every OpenManage endpoint, generated unique admin credentials, and stored them in a secure vault. They eliminated hard-coded defaults, applied MFA where available, and enforced a quarterly rotation schedule. All activity was logged and fed into their SIEM. Within a few cycles, they reduced potential credential exposure and improved audit readiness. This practical example demonstrates how disciplined credential management translates into measurable security improvements for OpenManage environments.
- Step through discovery, verification, rotation, and monitoring in a tight feedback loop.
- Align OpenManage credential practices with broader security controls and governance.
- Document lessons learned to strengthen future deployments.
Common Pitfalls and How to Avoid Them
Common mistakes include assuming defaults are safe, failing to rotate credentials after provisioning, and neglecting to document admin access. Others involve distributing credentials across emails or spreadsheets, or misconfiguring MFA on management interfaces. To avoid these, enforce a culture of credential hygiene, automate where possible, and perform independent security reviews on OpenManage configurations. Regularly refresh access policies and validate that all devices reflect current, compliant credentials. By proactively addressing these pitfalls, you create a resilient OpenManage environment that resists credential-based attacks.