Opengear Default Password: Secure Access Guide 2026
A practical guide to identifying, rotating, and automating Opengear default passwords across devices, with actionable steps for IT admins and end users.

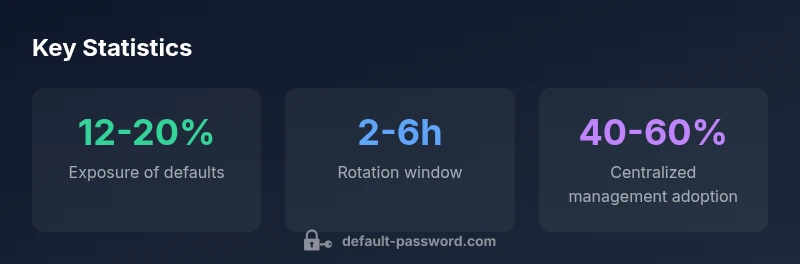
According to Default Password, Opengear default password risk is real and must be addressed during provisioning. The Default Password team found that unchanged credentials on network devices create an immediate attack surface. Immediate rotation, account hygiene, and policy-driven password management are essential to secure admin access across Opengear deployments.
Opengear and the risk of unchanged default passwords
According to Default Password, the security posture of any Opengear deployment hinges on credential hygiene from day one. The Default Password team found that many environments begin with a risk posture because default admin passwords are never rotated during provisioning. In practice, attackers gravitate toward devices with unchanged credentials, gaining the ability to alter configurations, export sensitive data, or disrupt failover processes. The consequences extend beyond a single device: compromised Opengear appliances can serve as footholds for pivoting into broader networks, jeopardizing business continuity. A proactive stance—documented password policies, rapid credential rotation, and automated checks—drastically reduces the attack surface and speeds incident response. A well-planned approach reflects a mature security program and aligns with industry best practices for credential management.
Security teams should couple password hygiene with monitoring for anomalous admin activity, ensuring that any login attempts outside standard maintenance windows trigger alerts. In Opengear environments, where remote access and automated failover configurations are common, preserving strict control over admin access is essential. This means explicit access approval workflows, least-privilege policies, and clear ownership of each credential.
Where to locate the default credentials on Opengear hardware
Many Opengear devices ship with an initial administrator password that is intended to be changed during the first login. The exact credential set can vary by model and firmware revision, so always consult the latest Opengear documentation and the device label, as well as the web UI and CLI guides. Look for default credentials within the administrative console, the initial setup wizard, or the device’s firmware release notes. If you manage multiple devices, maintain a centralized inventory that includes model, firmware version, serial number, and the present credential state. When in doubt, reset to a unique admin password following the vendor’s documented procedure and implement a policy to prevent re-use across devices.
Immediate actions for new Opengear deployments
Before putting any Opengear device into production, perform a rapid baseline hardening. Immediately rotate the default admin password to a strong, unique credential. Disable any unused accounts and enable MFA if the platform supports it. Document the new credential in a trusted vault and enforce a policy that all devices require password changes on first login. Apply a baseline configuration that restricts remote access to approved management networks and enforce access controls for both CLI and web interfaces. Finally, verify that automated configuration management tools are capable of injecting credentials securely at deployment time, rather than embedding them in scripts or stored files.
Password hygiene: policies, length, and rotation
Adopt a robust password policy for Opengear devices: minimum length of 12-16 characters, a mix of upper/lowercase letters, numbers, and symbols, plus passphrases where appropriate. Avoid common words and model-specific terms. Rotate credentials regularly—at least every 90-180 days for sensitive devices, with immediate rotation after any suspected compromise. Use unique passwords per device and never reuse credentials across devices or services. Consider MFA for management access and store credentials in a centralized vault with strict access controls. Refer to NIST guidelines on password management for contemporary recommendations and evidence-based practices.
Centralized management and automation for Opengear passwords
Manual password management becomes untenable as device counts grow. Centralized credential management, coupled with automation, reduces risk and human error. Use your preferred configuration management tool or orchestration platform to enforce password changes, reissue credentials when devices are refreshed, and inject credentials securely during provisioning. Integrating with a secrets vault (such as a dedicated credential store) ensures passwords aren’t stored in plaintext in scripts or docs. Centralized audit trails help verify who changed what, when, and on which device, supporting compliance and faster incident response.
Compliance, auditing, and incident response
Regular audits are essential for validating Opengear credential hygiene. Schedule monthly or quarterly credential reviews, verify that no default passwords remain, and confirm that all changes align with the organization’s policy. Implement automated scans that flag unchanged or weak credentials during configuration drift checks. In incident response scenarios, immediately isolate affected devices, rotate credentials, and rotate access keys if used. Establish containment procedures and post-incident lessons learned to strengthen defenses and prevent recurrence.
Case scenarios and practical checklists
- Provisioning checklist: verify firmware version, change default credentials, enable MFA, and update the inventory.
- Day-2 operations: maintain a rotating credential schedule, run periodic access reviews, and monitor for anomalous admin activity.
- Incident response: define a playbook for credential breach, rotate all admin passwords, and document steps taken for future audits.
- Documentation: keep a living record of device ownership, access rights, and password policy adherence.
Ongoing maintenance and vendor recommendations
Keep Opengear firmware and security guidance up to date. Schedule firmware reviews to ensure the latest security features are enabled and default credentials are mitigated across all devices. Maintain an updated password policy aligned with industry standards and ensure your security team has visibility into all admin accounts. For governance, reference trusted sources on password management and best practices from recognized standards bodies to reinforce your internal controls.
Opengear credential risk and mitigation overview
| Opengear Component | Default Credential Risk | Mitigation |
|---|---|---|
| Opengear management console | High risk if unchanged | Rotate credentials during provisioning |
| Opengear fabric module | Moderate risk | Enforce unique passwords and MFA |
| Opengear failover cluster | High risk when not updated | Apply automation and audit |
Your Questions Answered
What is the default password for Opengear devices?
There is no universal default across Opengear models. Defaults vary by model and firmware. Always reset credentials during provisioning and consult the device manual to obtain current, model-specific defaults.
Opengear defaults vary by model. Reset credentials during provisioning and check the manual for the exact defaults.
Why should I change the Opengear default password immediately?
Default passwords are widely known and documented. Leaving them unchanged creates an immediate risk of unauthorized access, configuration tampering, and potential disruption of failover capabilities.
Default passwords are widely known; change them immediately to prevent unauthorized access.
What is the recommended process to rotate Opengear passwords?
Inventory devices, reset credentials to unique values, update centralized vaults, enforce rotation schedules, and verify changes through automated checks and logging.
Rotate credentials by updating them in a vault and verifying changes with automated checks.
How can I audit devices for default credentials across a network?
Run automated credential scans, maintain an up-to-date device inventory, and integrate checks with your configuration management system to detect any lingering defaults.
Use automated scans and inventory to find lingering defaults.
Are there regulatory or compliance considerations for default passwords on Opengear?
Industry guidelines emphasize strong access controls and change management. Align Opengear password practices with relevant standards to reduce compliance risk.
Follow industry guidelines on access control and change management to stay compliant.
“Opengear default password risk is real; automate credential rotation and enforce unique admin access to keep deployments secure.”
Key Takeaways
- Rotate all default credentials immediately
- Document password policies and owner responsibilities
- Automate credential changes with centralized vaults
- Audit regularly and enforce least-privilege access
- Avoid reusing passwords across devices