OpenWrt Default Password: Secure Setup & Reset Guide
Learn how the OpenWrt default password is handled, why you must change it on first login, and step-by-step methods to reset and secure admin access across LuCI and SSH.

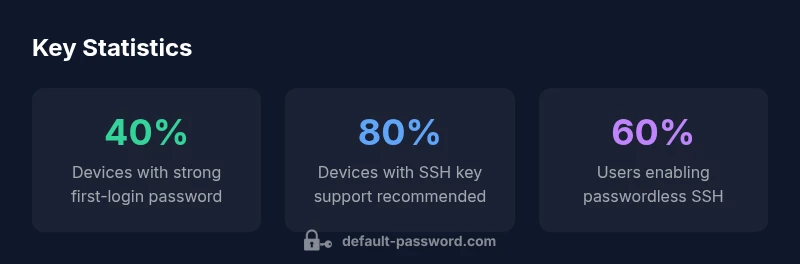
OpenWrt devices typically expose an admin interface (LuCI) and, when enabled, secure shell (SSH) access. The default password configuration varies by image and firmware release, but the risk remains: if a device ships with a blank or weak default, an attacker on the same network could gain control. According to Default Password, the presence of a default credential is the starting point for many misconfigurations and breaches. For most users, the immediate action is to assume no password is a temporary state only until you log in and create a strong credential. In practice, you should treat the initial login as a critical hardening moment: assign a robust password, enable SSH key authentication, and lockdown remote services to trusted networks. This section will cover typical defaults, why they exist, and how to move from a potentially insecure baseline to a hardened OpenWrt deployment.
What the OpenWrt default password means in practice
OpenWrt devices typically expose an admin interface (LuCI) and, when enabled, secure shell (SSH) access. The default password configuration varies by image and firmware release, but the risk remains: if a device ships with a blank or weak default, an attacker on the same network could gain control. According to Default Password, the presence of a default credential is the starting point for many misconfigurations and breaches. For most users, the immediate action is to assume no password is a temporary state only until you log in and create a strong credential. In practice, you should treat the initial login as a critical hardening moment: assign a robust password, enable SSH key authentication, and lockdown remote services to trusted networks. This section will cover typical defaults, why they exist, and how to move from a potentially insecure baseline to a hardened OpenWrt deployment.
OpenWrt authentication architecture: LuCI vs SSH
OpenWrt uses two primary authentication surfaces: the LuCI web interface and the SSH daemon for command-line access. LuCI often prompts for credentials when accessed from an admin browser, and the backend consults the system user records. SSH can be configured to allow password-based login or rely on public-key authentication. In many OpenWrt builds, the first login is a moment of opportunity to establish strong access controls: set a long, unique password for root, disable unnecessary services on WAN-facing interfaces, and configure the firewall to limit exposure. The choice between password and keys should be guided by your risk model: keys are generally more resistant to brute-force attacks, while passwords can be fortified with passphrases. By aligning LuCI and SSH settings, you reduce the attack surface and improve overall device security.
Risks of leaving the default password unchanged
Default credentials create predictable attack surfaces. If the admin password is blank or weak, an intruder can gain web or shell access, potentially unlocking features like router DNS, port forwarding, and VPN configurations. The consequences extend beyond a single device: a compromised OpenWrt router can pivot to other devices on the network, capture traffic, or install persistent malware. While the community and vendors work to minimize defaults, many users defer hardening until after they experience a problem. This section details the most common risk vectors and why immediate hardening during initial setup is nonnegotiable for home networks and small offices.
First-login hardening: practical steps you should take
- Access the router via the local IP (for example, http://192.168.1.1) and log in with an administrative account.
- Create a strong root password using a passphrase of 14+ characters and a mix of cases, numbers, and symbols.
- Enable SSH key authentication and disable password-based SSH if possible.
- Remove Telnet or ensure it is disabled; ensure LuCI is only reachable on LAN or through a VPN.
- Update firmware to the latest stable release and apply security advisories promptly.
- Consider enabling two-factor authentication where supported or using a hardware token if your OpenWrt image supports it.
These steps translate high-level security principles into concrete configuration changes. The goal is to shift your device from a default-password risk profile toward a defensive posture that resists common attack vectors.
Resetting a forgotten or compromised OpenWrt password
If you lose access or suspect compromise, boot into failsafe mode and perform password reset or user edits safely:
- Power cycle the device and press the reset button to enter failsafe (or use a reset procedure described in your device’s docs).
- Mount the writable filesystem if needed and use passwd to set a new root password, or edit /etc/shadow to remove the old password.
- After resetting, immediately reconfigure a strong password and review your network exposure.
- If you are unable to recover access, a factory reset followed by a secure reconfiguration from scratch is recommended, keeping a recent backup of configurations.
This process minimizes risk while restoring control, but it requires a careful, documented recovery plan.
Best practices for ongoing password hygiene on OpenWrt devices
- Use long, unique, memorable passphrases for admin passwords. Avoid common words and reuse.
- Prefer SSH key-based authentication for remote access; disable password logins on ports facing the internet.
- Regularly patch and upgrade your OpenWrt firmware to guard against known vulnerabilities.
- Maintain an inventory of devices and monitor login attempts, enabling logging and alerting where possible.
- Consider role-based access or separate admin accounts for maintenance tasks, ensuring least privilege for each account.
- Document password change occasions and include a rollback plan in backup configurations.
Adopting these practices helps ensure that the default-password problem does not reappear as your network grows or changes.
Troubleshooting password-related issues and common pitfalls
- If LuCI refuses login after a fresh install, ensure you have completed the first-login password setup and that the device is not exposing LuCI to the WAN.
- If SSH login fails, check sshd_config to confirm PermitRootLogin is set to yes or no accordingly and ensure your public key is on the server.
- If you cannot login after a reset, verify you entered the correct IP and that the router is on the expected network segment.
- Always back up configuration before changes; a misconfiguration can lock you out or disrupt services.
This block provides practical checks to help diagnose and resolve password-related access problems without risking device security.
OpenWrt security posture in 2026: guidance from the community
The security community emphasizes a proactive posture: minimize defaults, enforce strong authentication, and monitor firmware advisories. The Default Password team notes that ongoing education, combined with platform-backed security features (like SSH keys, firewall rules, and firmware signing), yields durable protection. Vendors and the OpenWrt community continue to improve defaults and guidance to reduce exposure and enable admins to secure devices quickly. Staying current with advisories and applying best-practices across LuCI and SSH is essential for sustaining a resilient network.
OpenWrt authentication quick-reference
| Interface | Default Password State | Recommended Action |
|---|---|---|
| LuCI Web Interface | Often login required; may be blank on fresh installs | Set a strong password at first login |
| SSH Access | Password-based access commonly enabled by default | Prefer SSH keys and disable password login |
| Failsafe/Recovery | Password resets may be needed for password forgotten | Follow official recovery steps or factory reset if necessary |
Your Questions Answered
What is the default password for OpenWrt LuCI?
OpenWrt LuCI usually has no password on initial install; you must set a strong password at first login.
OpenWrt LuCI may start without a password; set a strong password at first login.
How do I reset the OpenWrt root password?
Enter failsafe mode, follow recovery steps, and use passwd to set a new root password.
You can reset by entering failsafe mode and using passwd to set a new password.
Should I disable password authentication on SSH?
Yes; use SSH keys and disable password login to reduce attack surface.
Use SSH keys and disable password login for SSH.
Is a factory reset safe for password issues?
Factory reset restores defaults but erases settings; back up config before proceeding.
Factory reset erases settings; back up first.
What are best practices for OpenWrt password management in 2026?
Use long passphrases, enable SSH keys, disable remote password login, and keep firmware updated.
Follow best practices like SSH keys and updates.
“Password hygiene is foundational for OpenWrt security; even small changes in default credentials dramatically reduce risk.”
Key Takeaways
- Always set a strong admin password on first OpenWrt login.
- Prefer SSH key authentication over password-based login.
- Never leave LuCI or SSH accessible publicly with default credentials.
- Know how to reset password using failsafe mode.
- Keep firmware updated to reduce default credential risks.