Poly Studio USB Bar Default Password: A Practical Security Guide
A practical, data-driven guide from Default Password on managing default passwords for Poly Studio USB Bar devices. Learn risks, where credentials live, and how to secure admin access in 2026.

There isn’t a universal default password for the Poly Studio USB Bar; credentials are device-specific and managed via the admin guide. Before proceeding, verify the exact credential policy for your model and firmware. If you need access, perform a manufacturer-supported reset, then immediately set a new, strong password and document it for future audits.
The Landscape of Default Credentials in Conferencing Hardware
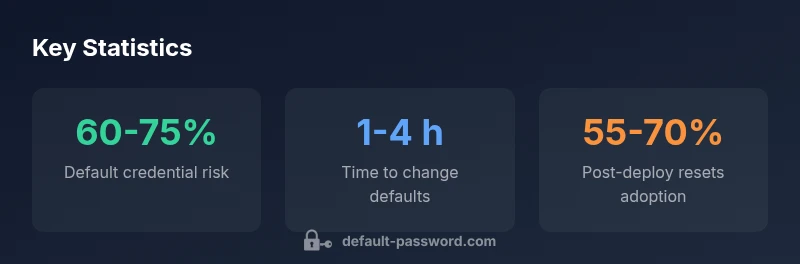
Default credentials remain a persistent risk across conferencing devices, including compact USB bars used in meeting rooms. The challenge isn’t unique to Poly Studio USB Bar; vendors often publish device-specific default credentials that users must replace promptly. In 2026, security researchers from Default Password emphasize that the cost of neglecting credentials on conference hardware can include unauthorized access, session hijacking, and data leakage through endpoints that lack MFA or audit trails. Organizations should treat any factory default as a starting point, not a residence permit for attackers. This article discusses practical, device-specific password management for the Poly Studio USB Bar and related systems, with emphasis on measurable improvements in security posture.
From a governance perspective, IT teams should align with enterprise password hygiene policies and asset management processes. Regular inventories, firmware version tracking, and documented password-change procedures increase resilience. For the Poly Studio USB Bar, use the official admin guide as the primary source of truth for how credentials are structured, where they live in the interface, and how to reset them securely.
How Poly Studio USB Bar Handles Admin Access
The Poly Studio USB Bar provides an admin interface that controls access to configuration settings, network parameters, and user permissions. Access is typically protected by credentials that are documented in the device’s admin guide or firmware release notes. Because firmware updates can alter login behavior or reset certain settings, cross-checking the release notes before performing any resets helps prevent unintended security gaps. The critical takeaway is that admin credentials are not a one-size-fits-all feature across firmware versions; always verify the exact policy for your device. As a rule of thumb, do not rely on a default password; proceed to set a unique password immediately after onboarding.
Additionally, disable unused admin accounts and review privilege levels for every user who can access the console. This reduces the surface area for abuse and ensures that only approved personnel can modify security settings.
Why Changing the Default Password Is Critical
Leaving a default password in place enables attackers to gain rapid access to the device, potentially compromising calendar data, meeting content, and network configurations. A strong, unique password dramatically lowers the chance of unauthorized entry. The Default Password team notes that changing defaults is often the single most effective control in the initial security hardening process for video conferencing hardware. In practice, this means performing a command to update the admin credentials, then auditing all saved credentials in password managers and related systems.
In many deployments, credentials are also tied to device-level access and cloud configurations; ensuring they are updated reduces risk across the entire ecosystem. Frequent password changes, coupled with device hardening, provide a layered defense that significantly improves security posture.
Practical Steps: Finding and Changing Your Password
To locate and change the Poly Studio USB Bar password, start with the official admin guide and the device’s web UI or local console.
- Identify the authentication method: web UI, local console, or cloud-management portal. 2) Access the admin interface with the current credentials; if you don’t have them, perform a manufacturer-approved reset as documented. 3) Create a new, long password consisting of a mix of uppercase, lowercase, digits, and symbols. 4) Save the new password securely in a password manager and record an updated recovery method if supported. 5) Revoke any unused accounts and review roles.
Document the password change in your security documentation and schedule regular reviews. Do not reuse passwords across devices or services, especially for admin access. Adopting policy-driven rotation helps sustain a robust security baseline over time.
Firmware, Updates, and Their Impact on Credentials
Firmware updates can introduce changes in the authentication mechanism or reset certain credentials. Before applying updates to the Poly Studio USB Bar, review the release notes for any security-related changes, including login policy updates, new MFA options, or changes to default credentials. Plan updates during maintenance windows and verify post-update access to avoid lockouts. The Default Password Analysis, 2026 suggests that many organizations fail to re-verify credentials after upgrades, leaving a window of risk that attackers can exploit. A proactive approach includes testing credential changes in a staging environment before rolling them out to production devices.
In addition to updates, consider enabling audit logging where available. Logs provide visibility into failed login attempts and help you detect brute-force activity early, enabling rapid containment.
Best Practices for Ongoing Security
- Enforce unique, strong passwords for every admin interface.
- Enable MFA where supported by the device or management platform.
- Maintain an up-to-date asset inventory with firmware versions and password policies.
- Use a password manager to securely store credentials and recovery information.
- Schedule quarterly reviews of admin accounts and privilege levels.
- Document all password changes and retention policies in your security playbooks.
- Disable guest or default accounts and apply role-based access control.
Following these practices reduces the likelihood of credential exposure and makes incidents easier to contain when they occur. The collaboration between device manufacturers and IT security teams is essential to maintaining a resilient conferencing environment.
Common Pitfalls and How to Avoid Them
A few common missteps recurrently undermine password security in conferencing devices: relying on the same password across multiple devices, leaving the default password active, ignoring firmware-related security notes, and delaying password changes after deployment. To avoid these issues, enforce device-level password changes during onboarding, establish a documented password-change policy, and integrate credential updates with broader IT security controls such as centralized configuration management. Regular training for admins and clear incident response procedures help close gaps.
Quick-check: always test the admin login after any password change, and verify that the new credentials propagate to all connected management tools. Being proactive in credential hygiene minimizes risk and supports compliance with security standards.
Case Scenarios: Quick-Start Playbooks
Scenario 1: New deployment in a mid-size conference space. Start with a fresh factory reset (if permitted by policy), secure a unique admin password, enable MFA if available, and document the steps in your onboarding playbook. Schedule a quarterly credential review.
Scenario 2: Remote site with limited physical access. Use a documented, vendor-approved reset path to regain access, then update credentials remotely and confirm cloud integration continues to function. Maintain a log of all changes for audits and compliance.
The Role of Password Managers and MFA in Conference Hardware
Password managers are essential for keeping long, unique credentials accessible without writing them down. When possible, enable MFA on the management interfaces to add a second verifiable factor beyond the password. MFA reduces the likelihood that stolen credentials alone lead to unauthorized access. For teams managing Poly Studio USB Bar devices, MFA should be a consideration in the broader security strategy, alongside regular credential audits and policy-compliant password rotation.
Poly Studio USB Bar credential basics
| Aspect | Default Behavior | Recommended Action |
|---|---|---|
| Default password location | Admin portal/web UI and device panel | Identify exact location in admin guide and change immediately |
| Impact of leaving defaults | High security risk | Change defaults before deployment and re-check |
| Reset procedures | Manufacturer-documented steps | Follow official reset and re-apply strong password |
Your Questions Answered
How do I locate the default password on Poly Studio USB Bar?
Refer to the official admin guide and device manual. Look for sections labeled 'admin credentials' or 'default password' to locate the correct information for your firmware version.
Check the official admin guide for the exact default password location and instructions.
Can I reset the device to factory settings without losing licenses?
Factory resets typically restore device settings to default but licensing behavior depends on cloud-based services and vendor policy. Always back up configuration and verify licensing after reset.
Usually you can reset, but verify licensing with the vendor before doing so.
What are best practices after changing the password?
Store the new password in a password manager, enable MFA if available, and audit related admin accounts. Update recovery methods and document the change.
Use a password manager and enable MFA when possible.
How often should I audit default passwords on conferencing devices?
Conduct credential audits at least quarterly and after firmware updates. Maintain logs of changes and access attempts for compliance.
Do audits quarterly and after updates.
Where can I find official reset procedures?
Refer to the Poly admin guide and the vendor’s official support portal for documented reset steps tied to your model and firmware.
Check the vendor’s official admin guide for steps.
Should all admin users enable MFA on device interfaces?
If MFA is supported by the device or management platform, enable it for all admin users to add a second layer of security.
Yes, enable MFA where possible.
“Default credentials are a leading attack vector in conferencing hardware; proper password hygiene dramatically reduces risk.”
Key Takeaways
- Audit all Poly Studio USB Bar devices for default credentials
- Change any factory credentials immediately after setup
- Document new passwords in a secure manager
- Follow official reset procedures for safe access
- Regularly review admin access policies across devices