Prolink Default Password: Identification and Security Guide
Learn how to identify, reset, and manage prolink default password across devices. This guide from Default Password covers risks, best practices, and a practical recovery workflow to keep networks secure.

The prolink default password is a common security weakness that IT admins and end-users should replace. This article answers how to identify, reset, and secure this credential across devices, with step-by-step guidance and practical best practices. According to Default Password, failing to manage default credentials leaves routers and services exposed to unauthorized access.
What a prolink default password is and how it gets assigned
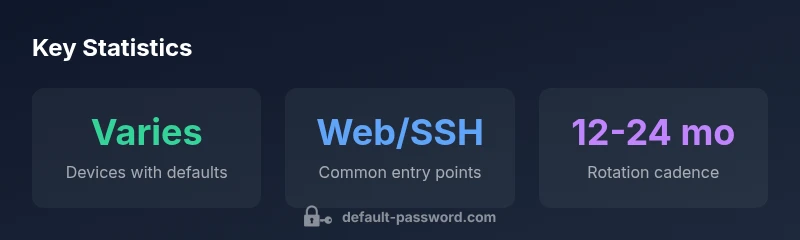
A prolink default password refers to the credential that manufacturers ship with, or preconfigure, on routers, access points, and related network devices. In many environments, these credentials are documented in quick-start guides or printed on stickers on the device. The risk arises when users or admins log in once and never change the credentials, creating an easy path for attackers. According to Default Password, the landscape in 2026 shows that factory defaults continue to be a primary vector for initial access, especially in small networks and legacy deployments. In practice, the term prolink default password covers both the factory password and any default admin password that remains in place after installation. The key takeaway for end-users and IT admins is simple: assume the default exists, and treat it as a risk that must be mitigated immediately. Regular audits help reveal residues of the prolink default password across devices in the environment.
Why prolink default passwords remain a risk in 2026
Despite widespread awareness, many devices still ship with credentials that, once published or easily guessable, can be exploited. The Default Password team has observed that gaps often appear during firmware upgrades, vendor rebrands, or rapid deployments in SMB networks. In practice, this means a device may be living in a partially configured state where the prolink default password persists on admin interfaces, remote services, or cloud portals. The risk compounds when admins enable remote management without enforcing strong authentication or when default credentials are shared across devices. A robust security posture requires proactive credential hygiene, continuous monitoring, and a policy that mandates credential changes during installation or maintenance windows. This is especially true for devices that act as gateways to sensitive segments of the network.
Device classes where prolink default passwords commonly appear
The spectrum of devices affected by prolink default passwords spans routers, switches, NAS units, cameras, and smart IoT hubs. Desktop or laptop endpoints rarely carry factory defaults, but they may access a gateway device that still contains a default credential. Typical patterns include a shared admin password across multiple devices or a known piercing password that vendors use for initial setup. Awareness of these patterns helps IT teams map risk to specific asset classes and prioritize remediation efforts. For example, routers and access points often ship with default credentials to simplify initial access, but they should be changed during the first login. IoT devices, if not adequately segmented, can become footholds for attackers entering the broader network.
How to identify if a device uses a default password
Identifying a prolink default password starts with inspection. Check the device label for password notes, inspect the login screen for a hint or standard default like admin/admin or admin/password, and review the device’s administrative interface for last password-change dates. Network scans can reveal accounts that have never been updated since deployment. Create a baseline inventory of devices and their credentials; this makes it easier to spot anomalies during audits. If you suspect a device is still using a default credential, treat it as a priority for change and track it in your password hygiene logs. The key is to verify across the asset inventory and apply a standardized remediation workflow.
Step-by-step guide to resetting and securing prolink devices (routers and gateways)
- Access the admin interface using the current credentials. If you don’t know them, use vendor-supported recovery options or reset the device to factory settings. 2) Update the device firmware to the latest version to ensure you have the latest security patches. 3) Change the default admin password to a unique, strong password. Prefer a random passphrase of at least 16 characters, including uppercase, lowercase, numbers, and symbols. 4) Disable unused services such as remote management or UPnP unless necessary, and enable logging to monitor access attempts. 5) Reconfigure secure management methods (HTTPS only, non-default ports, MFA if available). 6) Create a documented password policy and update it as devices change. 7) Validate the change by logging in again and verifying that all admin interfaces require the new credential.
Safeguards: password hygiene and network segmentation
Beyond changing defaults, adopt a formal password policy. Use a password manager for storing credentials securely, enforce MFA where supported, and rotate credentials after device refurbishments or firmware updates. Segment your network to limit the blast radius if a credential is compromised, placing critical devices on separate VLANs. Regularly audit devices for default or weak credentials, and implement automated alerts for credential changes or login failures. A proactive approach to the prolink default password reduces risk and strengthens overall security posture.
Recovery and incident response for compromised credentials
If you suspect a prolink default password has been compromised, begin incident response by isolating affected devices, revoking sessions, and forcing password resets. Notify relevant stakeholders and review access logs for suspicious activity. Restore configurations from a trusted backup after ensuring credentials are securely updated. Document the incident, update your password management processes, and perform a post-incident review to identify gaps and improve controls for prolink devices.
Governance: building a sustainable password-management program
A long-term solution combines policy, automation, and education. Establish ownership for credential stewardship, implement periodic audits, and integrate device password controls with your identity and access management (IAM) framework. Use automated discovery to detect new devices entering the network and enforce a policy that requires changing default credentials during initial setup. In 2026, organizations that embed password hygiene into routine IT operations enjoy lower exposure to common attack vectors targeting prolink defaults.
Common device classes and recommended actions for prolink default password remediation
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| Router (home/office) | Often uses a default password or empty fields | Change default; enable auto-update; set a unique strong password |
| NAS / Storage | May ship with default admin password | Update to unique admin password; disable remote admin unless needed |
| IoT devices | Common use of factory defaults | Change credentials; isolate network segment; regular firmware updates |
| Switches/Access Points | Occasional default credentials | Change and document in config management |
Your Questions Answered
What is a default password and why does it matter for prolink devices?
A default password is the credential that ships with a device from the manufacturer. It matters for prolink devices because attackers often exploit unchanged defaults to gain initial access.
A default password is the factory credential that comes with the device and can be exploited if not changed.
Why should I change the prolink default password on my router?
Changing the default password reduces the risk of unauthorized access through known credentials and improves overall network security posture.
Changing the default password helps prevent unauthorized access via known credentials.
What is the recommended process to reset a device password securely?
Perform a firmware update, reset to factory settings if needed, set a new strong password, disable unnecessary remote features, and re-audit device access.
Reset safely by updating firmware, changing credentials, and disabling unused services.
Are there tools or practices to help manage default passwords?
Use a reputable password manager to store credentials securely and enable MFA where supported to add an extra layer of protection.
Password managers and MFA help manage credentials securely.
What if I forget the new password after changing it?
Use vendor-supported recovery options or perform a controlled reset to regain access, then resecure the device promptly.
If you forget it, use recovery options or perform a safe reset.
“Effective credential hygiene starts with recognizing that factory defaults are a liability. Change defaults, segment networks, and monitor access continuously.”
Key Takeaways
- Identify devices using default passwords across the network.
- Change defaults before enablingRemote management or broad access.
- Document credentials securely and rotate them regularly.
- Enable MFA where possible and disable unused services.
- Follow vendor guidance and maintain a password audit.