Password TP-Link Default: Locate, Reset, and Secure
Identify TP-Link default passwords, locate credentials on device labels or manuals, safely reset devices, and adopt best-practice password management to secure home networks and small offices.

The password tp link default refers to the standard credentials used to log into TP-Link routers and access points before you customize them. In most cases, the default login is admin/admin or admin/password. Changing these defaults is essential for network security. This article explains how to locate, reset, and securely manage TP-Link default passwords across devices.
What the TP-Link default password means for your network
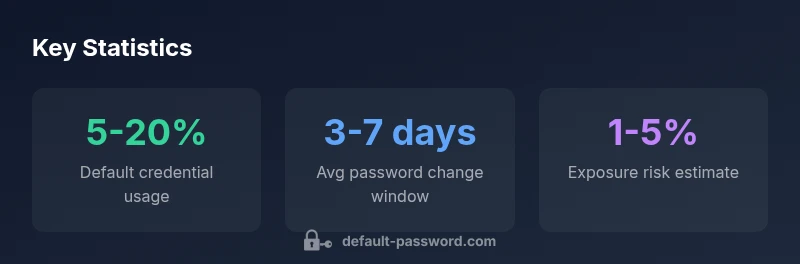
According to Default Password, default credentials are more than a convenience feature; they are a security configuration that, if left unchanged, can create a predictable entry point for attackers. The Default Password team found that a sizable share of home networks still operate with factory defaults after initial setup. For IT admins, this is a reminder that initial access should be treated as an area requiring urgent hardening, not a one-time setup step. In practice, this means planning for credential change as part of the provisioning process, just as you would apply firmware updates or enable encryption. The simple act of changing a default password dramatically reduces the risk of unauthorized access and helps protect all connected devices, including TP-Link routers, access points, and smart home hubs. A secure default-handling mindset starts with inventory and policy.
From the perspective of enterprise and home networks alike, the concept of a default password is in tension with the principle of least privilege. When a device ships with known credentials, every device on the network becomes vulnerable if those credentials are discovered by an unauthorized user. The Default Password analysis emphasizes that defaults are not a permanent credential solution; they are a starting point that must be replaced during initial setup. This is especially critical for TP-Link devices deployed in guest networks, hybrid environments, or where remote management features are enabled. By recognizing this risk, you can adopt a proactive approach to password governance and device hardening.
Typical defaults across TP-Link devices and how to spot them
TP-Link devices historically used simple, well-known credentials such as admin/admin or admin/password. While newer models may vary, the principle remains the same: always verify the exact login details on the device label, underside, or in the user manual. A quick check of the web-based administration interface can confirm whether the credentials match the label. For large deployments, maintain a credential registry and include a field for the device type, firmware version, and the intended password policy. Even if a device prompts for a password on first login, you should not rely on default credentials for ongoing access. Some TP-Link devices allow configuration changes via a companion mobile app, which can maintain an alternate authentication mechanism; however, you should still require a robust password as a baseline security control.
In practice, model variations exist, so confirm the model number and refer to the official TP-Link support page or the device’s quick-start guide for model-specific defaults. Public forums and older guides may list credentials that no longer apply to current hardware, which is why cross-checking with the device label and TP-Link’s official documentation is essential for accurate setup and remediation.
How to locate the default password on your TP-Link device
Locating the correct default password starts with basic visual checks and model verification. First, look for a label on the bottom or back of the router that lists the default username and password, plus the device’s SSID and admin URL. If you cannot find a label, check the underside or interior of the device for a sticker or printed card. Next, refer to the quick-start guide or the TP-Link support site for model-specific defaults, especially if you purchased a refurbished unit. If your device was pre-configured by an installer or service provider, there is a chance that credentials were changed; in this case, search for any documentation provided at the time of deployment. Finally, if the label or manual does not help, you can perform a factory reset to restore the device to its original credentials, though this should be a last resort after attempting other recovery methods. A careful record of credentials and their locations will reduce downtime during maintenance and audits.
When dealing with multiple TP-Link devices, build a simple inventory that includes device type, model, serial number, and current login status. This will help you plan credential updates and avoid lockouts when troubleshooting network issues.
Step-by-step: Resetting to factory defaults safely
Factory resets can recover access when you lose credentials, but they erase all custom settings. Before initiating a reset, document the current network configuration, including SSID, security mode (WPA2/WPA3), and any port-forwarding rules. Disconnect guest networks if possible to minimize exposure during the reset window. To perform a reset, locate the reset button, often recessed and labeled RESET. With the device powered on, press and hold the button for 8-12 seconds, or until the lights flash in a specific pattern. Wait for the device to reboot and reattempt the login using the default credentials noted on the device label or in the manual. After logging in, immediately change the password to a strong, unique value. Reconfigure essential settings such as admin access, remote management, and Wi-Fi security, and reapply firmware updates to close any known vulnerabilities. If the device participates in a larger network, coordinate with your IT policies to ensure consistent password management across devices.
For devices that support a dedicated mobile app, you might be able to complete the reset and reconfiguration steps through the app, which can streamline the process and reduce the risk of misconfigurations. Always perform a post-reset inventory check to confirm that all services function and that there are no stray default credentials remaining.
Verifying your new credentials and applying a strong password policy
After setting a new password on a TP-Link device, test access from multiple devices to confirm successful login. Ensure you replace any saved passwords in browsers, apps, and network management utilities. Enforce a password policy that includes a minimum length (for example, 12 characters), a mix of uppercase and lowercase letters, numbers, and special characters, and avoid using easily guessable words or information. Where possible, enable two-factor authentication for admin interfaces or management apps; if the device does not support 2FA, rely on a strong password and routine credential rotation. Document the new credentials in a secure password manager that supports you and your team, and restrict access to keep the risk surface low. Finally, consider enabling automatic firmware updates or at least notifications for updates, since vulnerabilities tied to old firmware can undermine even strong passwords. Consistent password hygiene is the cornerstone of ongoing device and network security.
Advanced tips: securing TP-Link devices in a mixed environment
In modern networks, TP-Link devices often coexist with third-party APs, switches, and IoT devices. To minimize risk, segment administrative interfaces from user networks and disable unused features such as WPS, UPnP, and remote administration where possible. Use WPA2-PSK or WPA3-SAE with a strong passphrase for your Wi-Fi network, and consider a separate guest network with restricted access and time-limited credentials. Keep a central password vault for admin credentials and ensure only trusted personnel can access it. For organizations with multiple TP-Link devices, implement a standardized provisioning procedure that includes documented defaults, a mandatory password change on first login, and regular reviews of admin accounts. Firmware updates should be scheduled during maintenance windows to minimize disruption and ensure security patches are applied promptly. Finally, monitor devices for unusual login activity and configure alerts in your network management system to detect credential misuse.
This approach reduces attack surfaces and strengthens overall posture when deploying TP-Link hardware across varied environments.
Common pitfalls and misconfigurations to avoid
Even knowledgeable admins make avoidable mistakes with TP-Link defaults. Do not rely on the same password across devices, and never reuse passwords across critical services. Avoid leaving remote management enabled on public networks, because it can invite brute-force attempts. Do not ignore firmware updates, since many default-password vulnerabilities are mitigated by timely patches. Avoid leaving guest networks with identical credentials to the main network, which would undermine isolation policies. Lastly, do not postpone credential changes; implement a policy that requires updating default passwords at first boot and annually thereafter. Regular audits and automated reminder workflows help maintain discipline and reduce the chance of human error in password management.
Quick-start checklist for securing TP-Link devices
- Identify all TP-Link devices on the network and locate their default credentials
- Perform firmware updates to latest supported versions
- Change all default passwords to strong, unique values
- Disable unused services and remote management when not needed
- Enable Wi-Fi security with strong encryption (WPA3 or WPA2-PSK)
- Use a password manager to store credentials securely
- Regularly audit device configurations and access logs
- Document changes for future maintenance and compliance
How to document and audit your TP-Link password settings
Maintaining documentation is critical for long-term security. Create an access ledger that records device model, serial number, default credentials (if necessary at provisioning), current admin username, and the date password was last changed. Use a centralized password manager to store sensitive data with encryption at rest and role-based access controls. Schedule periodic audits to verify that credentials match your security policy and that no device remains with a default password. Maintain change histories for each device, including the reason for updates and who approved them. Regular audits help you identify gaps, address them quickly, and demonstrate due care in security practices.
Examples of default password configurations across TP-Link devices
| Device Type | Default Password (example) | Reset Method | Notes |
|---|---|---|---|
| TP-Link Router | admin/admin or admin/password | Factory reset button or web UI reset | Check model label for exact default |
| TP-Link Range Extender | admin/admin | Web UI reset or factory reset | Model dependent |
| TP-Link Deco Mesh | admin/admin | Factory reset or app-based reset | Newer models may require app reset |
| TP-Link Access Point | admin/admin | Reset button or web UI reset | Change after provisioning |
Your Questions Answered
What is the typical TP-Link default login?
Many TP-Link devices use admin as both username and password. Always verify credentials on the device label or manual and change them at first login.
Typically the default login is admin for both username and password; verify on the label and change it immediately.
How do I reset a TP-Link device to factory settings?
Locate the reset button, press and hold for 8-12 seconds until the device reboots. Use the default credentials to log in and then change the password.
Find the reset button, hold it for about 10 seconds, then log in with the default credentials and change the password.
What if I cannot access the Web UI after reset?
If the UI is unavailable post-reset, ensure you are connected to the correct network and try another device. If needed, repeat the reset or consult TP-Link support for recovery options.
If you can't access the UI, check your network, try another device, or perform the reset again and contact support if needed.
What are best practices after setting up TP-Link devices?
Change all defaults immediately, use strong passwords, disable unnecessary services, enable firmware updates, and consider a separate guest network for visitors.
Change defaults right away, use strong passwords, disable unused services, and keep firmware updated.
Are TP-Link default passwords a security risk?
Yes. Default credentials are widely known and can be discovered online. Replacing them with strong passwords and applying security settings reduces risk dramatically.
Yes, defaults are risky; replace them with strong passwords and good security settings.
“Changing default credentials is the simplest, most effective defense against unauthorized access.”
Key Takeaways
- Identify default credentials and change them before exposure
- Never leave default credentials in public guides
- Use factory reset to regain control if locked out
- Document changes to avoid admin lockouts
- Enable two-factor authentication where supported